uber_beetle
Posts: 91 +0
I've read lots of the other forum threads about this, and I've come up with two facts:
1) Run all the malware removal tools you can think of and it won't go away.
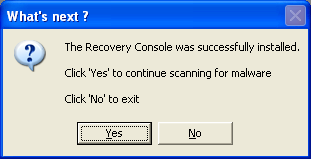
2) Combofix apparently is instrumental in getting rid of it, but I need your advice before implementing...
So... I've tried all I can think of and it won't go away. Please help!! =)
1) Run all the malware removal tools you can think of and it won't go away.
2) Combofix apparently is instrumental in getting rid of it, but I need your advice before implementing...
So... I've tried all I can think of and it won't go away. Please help!! =)