Investigations by Russian antivirus firm Dr. Web have concluded that more than 600,000 Mac computers are currently infected by the new strain of Flashback Trojan, with a massive 56.6% of the total infected machines believed to be in the US alone. Apple released an update earlier this week to patch vulnerabilities in Java that could be exploited to run malicious code in a victim's computer, including the newest strain written of the Trojan in question, but this will only protect those that are not already compromised by the malware.
Dr. Web revealed on their website yesterday morning that the Flashback botnet was some 550,000 strong. Later that day, malware analyst Sorokin Ivan revised that figure to more than 600,000 on Twitter.

According to Dr. Web, the US has the most infections with 56.6% of the total infected with the BackDoor.Flashback.39 malware. Of the 300,000 plus infected machines, the Russian antivirus firm also revealed 274 were from Cupertino. Canada had the second highest infection rate with 19.8%, the UK has 12.8% and in fourth place with 6.1% of the total number of infected machines in Australia.
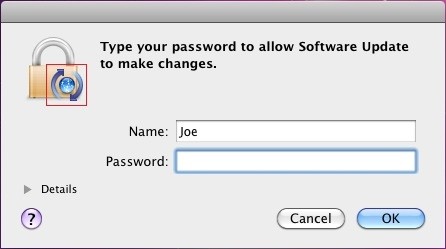
Internet security firm F-Secure has published detailed instructions on how to verify and remove the Trojan should your Mac computer already be infected. Interestingly, they state that the malware can infect a computer even without administrative permissions. "Whether or not the user inputs the administrator password, the malware will attempt to infect the system, though entering the password will affect how the infection is done."
The initial route to infection follows the same path. First the user visits a website which has been infected with the Flashback malware. Upon loading the infected webpage the script is executed, and it then immediately checks for the presence of several antivirus products. Should the presence of any be detected, the script then deletes itself and takes no further action.
If it doesn't find anything, the malware then connects to a specified URL and downloads the payload. It then proceeds to install this payload, and infects the Mac computer. It appears to do this in one of two separate ways, dependent on whether you give administrative permissions.
.
For those that refuse to grant them, the malware searches for Microsoft Office 2008, 2011 and Word applications, as well as for Skype. If it fails to find these it then creates several files in the userspace area and creates a launch point in the "~/.MacOSX/environment.plist" location of the Mac user's home folder.
Those that grant administrative permission will find the infection follows another pathway, creating several files inside Safari's "/Applications/Safari.app/Contents/Resources" folder, and the creation of a launch point in "/Applications/Safari.app/Contents/Info.plist" to start the malware when Safari is run.
Another note of particular interest is the way the code has been written. It appears to take complete advantage of the average Mac users' notion that their computer can't get infected and therefore doesn't need an antivirus product installed. Those using certain internet security products will therefore not have been infected but it appears to have been written to specifically target those that don't have any installed.
It's also important to note that the installation of the latest security patches from Apple is not enough to resolve the issue for those already infected. Many are now questioning whether Apple could have done more to prevent infections on such a massive scale, especially since Oracle had patches available back in February, but Apple took almost two months longer to release them on their platform.