I am having strange pop ups like for example "ms.paint.exe - Bad Image: The application or DLL C:\WINDOWS\system32\napipsec32.dll is not a a valid Windows image. Please check this against your installation diskette," whenever I open any program as well as getting Google redirects whenever I search a link using Google Chrome. This occurred after I did a System Restore after deleting the "Sigma Tel Audio" on accident for a Dell Vostro 1000 Notebook Laptop as these malware begin appearing.
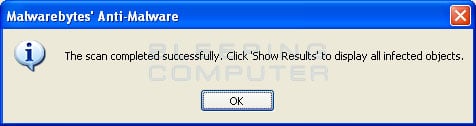
[All Logs have been posted in the following order - MBAM, GMER, DDS, & ATTACHMENT]
[All Logs have been posted in the following order - MBAM, GMER, DDS, & ATTACHMENT]