Malwarebytes' Anti-Malware 1.51.2.1300
www.malwarebytes.org
Database version: 911122704
Windows 5.1.2600 Service Pack 2
Internet Explorer 6.0.2900.2180
12/27/2011 3:56:38 PM
mbam-log-2011-12-27 (15-56-38).txt
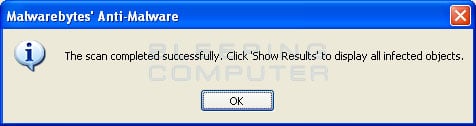
Scan type: Quick scan
Objects scanned: 205972
Time elapsed: 15 minute(s), 5 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 3
Registry Values Infected: 5
Registry Data Items Infected: 4
Folders Infected: 1
Files Infected: 3
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{BEAC7DC8-E106-4C6A-931E-5A42E7362883} (Adware.GameVance) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{BEAC7DC8-E106-4C6A-931E-5A42E7362883} (Adware.GameVance) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\RelevantKnowledge (Adware.RelevantKnowledge) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_CLASSES_ROOT\.exe\shell\open\command\(default) (Hijack.ExeFile) -> Value: (default) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run\Policies (Trojan.Agent) -> Value: Policies -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\HKCU (Trojan.Agent) -> Value: HKCU -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run\Policies (Trojan.Agent) -> Value: Policies -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\HKLM (Trojan.Agent) -> Value: HKLM -> Quarantined and deleted successfully.
Registry Data Items Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\IEXPLORE.EXE\shell\open\command\(default) (Hijack.StartMenuInternet) -> Bad: ("C:\Documents and Settings\matthew.YOUR-3DFB6AE27C.001\Local Settings\Application Data\xom.exe" -a "C:\Program Files\Internet Explorer\iexplore.exe") Good: (iexplore.exe) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\AntiVirusDisableNotify (PUM.Disabled.SecurityCenter) -> Bad: (1) Good: (0) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\FirewallDisableNotify (PUM.Disabled.SecurityCenter) -> Bad: (1) Good: (0) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\UpdatesDisableNotify (PUM.Disabled.SecurityCenter) -> Bad: (1) Good: (0) -> Quarantined and deleted successfully.
Folders Infected:
c:\documents and settings\matthew.your-3dfb6ae27c.000\application data\antispywarebot (Rogue.AntiSpywareBot) -> Quarantined and deleted successfully.
Files Infected:
c:\windows\temp\oiu0.42202161191372256.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
c:\windows\temp\oiu0.6951081937186443.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
c:\documents and settings\matthew.your-3dfb6ae27c.001\local settings\application data\xom.exe (Trojan.ExeShell.Gen) -> Quarantined and deleted successfully.