Researchers at cyber security specialist Cylance in collaboration with CERT at Carnegie Mellon University have uncovered a zombie vulnerability that affects all versions of Windows, including the latest Windows 10 preview.
The vulnerability is described as a zombie due to the fact that it’s based on an earlier, reported vulnerability. In this case, it’s an extension of a vulnerability discovered by Aaron Spangler way back in 1997 which still isn’t defended against by default.
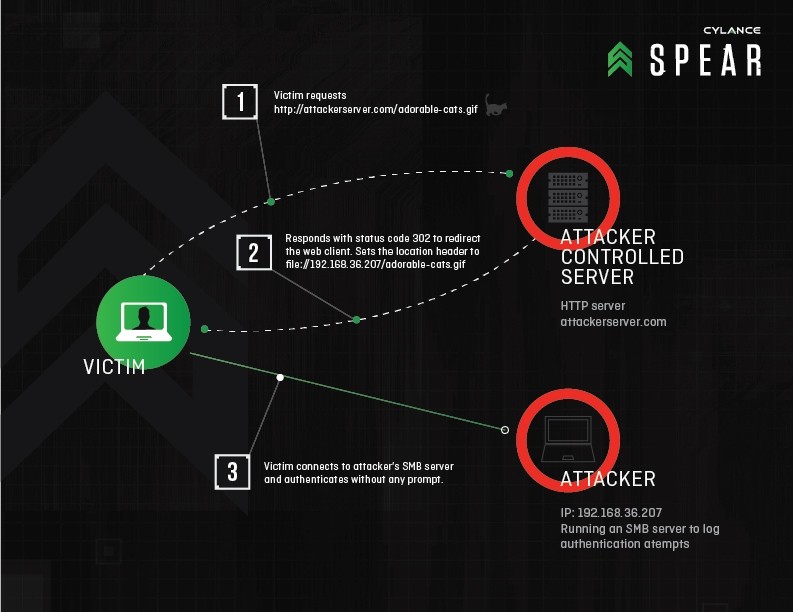
This new variant is being called Redirect to SMB (server message block). It’s essentially a way for hackers to hijack communications using man-in-the-middle attacks and force legitimate web servers to cough up login credentials including usernames and passwords.
The team has identified 31 software packages that are vulnerable to Redirect to SMB, many of which are programs you may use on a regular basis including Adobe Reader, QuickTime, Norton Security Scan, Windows Media Player, Excel 2010 and Internet Explorer 11.
Due to the advanced nature of the attack and the fact that the bad actor would need to have control over certain components, it’s most likely to be used in targeted attacks by skilled hackers.
Without an official fix from Microsoft, Cylance said the easiest workaround is to simply block outbound traffic from TCP 139 and TCP 445 at either the endpoint firewall or at the network gateway’s firewall. Microsoft never resolved the original issue in 1997 but perhaps this new method will convince them to finally take care of it.