Bobbye
Posts: 16,313 +36
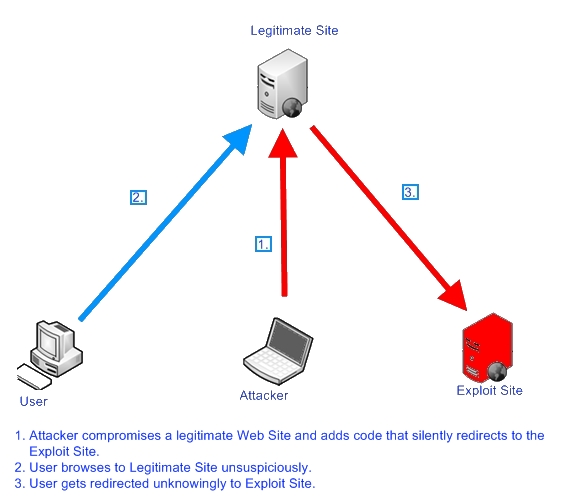
Anatomy of a Redirect: Part 1 The Basic How
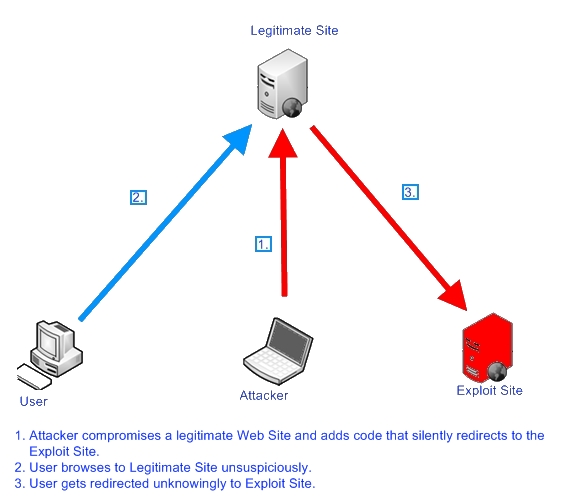


For the more technical-minded: http://securitylabs.websense.com/content/Blogs/3408.aspx
Anatomy of a Redirect: Part 2: The current What
Nine Ball, Gumlar and Beladen:
Nine Ball targets legitimate websites to redirect users to malicious sites owned by the attacker. The infected site will search the user's browser, Quicktime, and Adobe Reader for vulnerabilities that it can then exploit to load the malicious software. Once infected, anything the victim types can be monitored (keyloggers)and used to commit identity theft, such as credit card numbers, passwords and more.
Nine Ball is a particularly difficult foe for several reason:
http://www.switched.com/2009/06/18/here-comes-nine-ball-another-major-web-threat/
[*] It resists investigation by checking a visitor's IP address against a list of previous visitors.
[*] Trojans installed by Nine Ball on a PC are constantly mutating, making them very difficult to detect and destroy with traditional anti-virus software.
Gumblar> by ScanSafe and "Troj/JSRedir-R" by Sophos>> http://www.iss.net/threats/gumblar.html
Gumblar is a botnet that infects Web servers and infected Web site visitors for the purposes of installing malcode on Personal Computers (PCs) that redirects end-user Google searches to fraudulent Web sites.
Chinese Web domain gumblar.cn (associated with Russian and Latvian IP addresses) used to deliver the malicious code embedded in Web pages,delivering code from servers based in the U.K.-"delivering code from servers based in the U.K"> 95.129.144.0 - 95.129.145.255
marlor IP> RIPE network> 95.129.145.58 This domain stopped, but the malware continued to be delivered from a different source, the martuz.cn domain.Sites affected include Tennis.com, Variety.com, and Coldwellbanker.com, according to ScanSafe.
The scripts attempt to exploit vulnerabilities in Adobe's Acrobat Reader and Flash Player to deliver code that injects malicious search results when a user searches Google on Internet Explorer.
Infection means complete compromise of infected Web sites and PCs that they subsequently help to infect. Successful attacks may lead to exposure of confidential information, loss of productivity, and further compromise.
The malware affecting PCs targets prevalent Microsoft platforms: * Microsoft Windows 2000 * Microsoft Windows X * Microsoft Windows Server 2003
References
ScanSafe: http://blog.scansafe.com/
Unmask Parasites Blog: http://blog.unmaskparasites.com/2009/05/07/gumblar-cn-exploit-12-facts-about-this-injected-script/
Switched: http://www.switched.com/2009/06/18/here-comes-nine-ball-another-major-web-threat/
Beladen: a server-level exploit. All sites on exploited servers are affected. If you are on a shared hosting plan, there chances are you can’t resolve this issue without help of your hosting provider.
This code sets a cookie which expires in 1000 days (in my case it was sessionid=39128605A531) and loads external script from googleanalytlcs . net/ __utmj . js. Note, this domain doesn’t have anything to do with Google Analytics. It’s just trying to mimic it in hope to look trustworthy.
This script injects a hidden iframe with the following source: 46970e. beladen. net/e/ads.php?b=1010
The iframe tries to load malicious code from other beladen subdomains. “46970e . beladen . net“, “662577 . beladen . net”
Attack scheme: http://blog.unmaskparasites.com/2009/06/18/beladen-elusive-web-server-exploit/
Update: Beladen seems to have changed its name and now operates from shkarkimi . net. On Safe Browsing diagnostic pages Google now mention malicious domains as:
Malicious software is hosted on 2 domain(s), including googleanalytlcs . net/, shkarkimi . net/.
1 domain(s) appear to be functioning as intermediaries for distributing malware to visitors of this site, including googleanalytlcs . net/.
Backdoor scripts still reside on thousands of web servers and hackers can activate new attacks whenever they want.
Beladen.net Q&A: http://blog.scansafe.com/journal/2009/6/1/beladennet-qa.html
the malware being delivered are rogue scanners (aka scareware). Also known as fake AV
Edite: Additional Source: Zone Labs


For the more technical-minded: http://securitylabs.websense.com/content/Blogs/3408.aspx
Anatomy of a Redirect: Part 2: The current What
Nine Ball, Gumlar and Beladen:
Nine Ball targets legitimate websites to redirect users to malicious sites owned by the attacker. The infected site will search the user's browser, Quicktime, and Adobe Reader for vulnerabilities that it can then exploit to load the malicious software. Once infected, anything the victim types can be monitored (keyloggers)and used to commit identity theft, such as credit card numbers, passwords and more.
Nine Ball is a particularly difficult foe for several reason:
http://www.switched.com/2009/06/18/here-comes-nine-ball-another-major-web-threat/
[*] It resists investigation by checking a visitor's IP address against a list of previous visitors.
[*] Trojans installed by Nine Ball on a PC are constantly mutating, making them very difficult to detect and destroy with traditional anti-virus software.
Gumblar> by ScanSafe and "Troj/JSRedir-R" by Sophos>> http://www.iss.net/threats/gumblar.html
Gumblar is a botnet that infects Web servers and infected Web site visitors for the purposes of installing malcode on Personal Computers (PCs) that redirects end-user Google searches to fraudulent Web sites.
Chinese Web domain gumblar.cn (associated with Russian and Latvian IP addresses) used to deliver the malicious code embedded in Web pages,delivering code from servers based in the U.K.-"delivering code from servers based in the U.K"> 95.129.144.0 - 95.129.145.255
marlor IP> RIPE network> 95.129.145.58 This domain stopped, but the malware continued to be delivered from a different source, the martuz.cn domain.Sites affected include Tennis.com, Variety.com, and Coldwellbanker.com, according to ScanSafe.
The scripts attempt to exploit vulnerabilities in Adobe's Acrobat Reader and Flash Player to deliver code that injects malicious search results when a user searches Google on Internet Explorer.
Infection means complete compromise of infected Web sites and PCs that they subsequently help to infect. Successful attacks may lead to exposure of confidential information, loss of productivity, and further compromise.
The malware affecting PCs targets prevalent Microsoft platforms: * Microsoft Windows 2000 * Microsoft Windows X * Microsoft Windows Server 2003
References
ScanSafe: http://blog.scansafe.com/
Unmask Parasites Blog: http://blog.unmaskparasites.com/2009/05/07/gumblar-cn-exploit-12-facts-about-this-injected-script/
Switched: http://www.switched.com/2009/06/18/here-comes-nine-ball-another-major-web-threat/
Beladen: a server-level exploit. All sites on exploited servers are affected. If you are on a shared hosting plan, there chances are you can’t resolve this issue without help of your hosting provider.
This code sets a cookie which expires in 1000 days (in my case it was sessionid=39128605A531) and loads external script from googleanalytlcs . net/ __utmj . js. Note, this domain doesn’t have anything to do with Google Analytics. It’s just trying to mimic it in hope to look trustworthy.
This script injects a hidden iframe with the following source: 46970e. beladen. net/e/ads.php?b=1010
The iframe tries to load malicious code from other beladen subdomains. “46970e . beladen . net“, “662577 . beladen . net”
Attack scheme: http://blog.unmaskparasites.com/2009/06/18/beladen-elusive-web-server-exploit/
- Step 1. Hackers managed to compromise one account on a web server. Most likely (as in many recent exploits) FTP credentials had been stolen and used to upload a backdoor PHP script. The script (as per David Wenzel) is placed into some images directory.
- Step 2. Hackers call this script via HTTP and pass long encrypted parameters using the POST method. POST parameters are usually not reflected in Apache logs and the corresponding entry won’t be prominent. One of the parameters is a PHP script that checks if the system is vulnerable and then creates a file on disk (the content is extracted from another encrypted POST parameter) and executes it.
- Step 3. The new process starts intercepting random Apache requests for all sites residing on the compromised server and replacing legitimate responses with malicious content.
Update: Beladen seems to have changed its name and now operates from shkarkimi . net. On Safe Browsing diagnostic pages Google now mention malicious domains as:
Malicious software is hosted on 2 domain(s), including googleanalytlcs . net/, shkarkimi . net/.
1 domain(s) appear to be functioning as intermediaries for distributing malware to visitors of this site, including googleanalytlcs . net/.
Backdoor scripts still reside on thousands of web servers and hackers can activate new attacks whenever they want.
Beladen.net Q&A: http://blog.scansafe.com/journal/2009/6/1/beladennet-qa.html
the malware being delivered are rogue scanners (aka scareware). Also known as fake AV
Edite: Additional Source: Zone Labs