Microsoft is on the hot seat over a previously unknown bug in its Windows operating system that's being exploited to infect computers with the Duqu virus, piped by some experts to be the next big cyber threat. The Duqu virus was discovered last month, but at the time security specialists were still investigating how it worked and how it arrived on computers. It was later found to be a sibling of the Stuxnet worm that crippled an Iranian nuclear fuel plant last year.
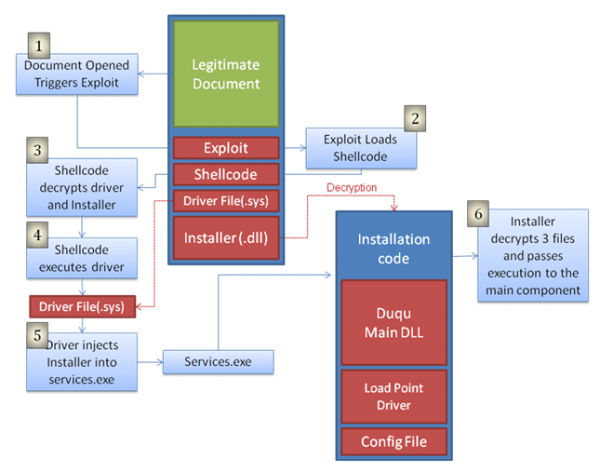
In a statement on their website, Symantec said, "we contacted Microsoft regarding the vulnerability and they're working diligently towards issuing a patch and advisory. When the file is opened, malicious code executes and installs the main Duqu binaries. The chart below explains how the exploit in the Word document file leads to the installation of Duqu."
Symantec has confirmed that the virus is very close to the Stuxnet worm and even shares some of its source code. The Duqu virus was designed to gather industrial control system data, including engineer's keystrokes, which it compiles for further use in an attack later on. The security firm found the installer file is a Microsoft Word Document (.doc) that exploits a previously unknown kernel vulnerability allowing code execution.
Infected Word documents were worded in such a way as to definitively target the intended receiving organization, according to researchers. No workarounds currently exist for those infected with the virus. "Once Duqu is able to get a foothold in an organisation through the zero-day exploit, the attackers can command it to spread to other computers," Symantec wrote.
So far, Duqu appears to have infected approximately six organizations in France, Netherlands, Switzerland, Ukraine, as well as India, Iran, Sudan and Vietnam. Other security vendors have reported infections in Austria, Hungary, Indonesia, Iran (with different infections to those reported by Symantec) and the UK.
Microsoft acknowledged the problem with its security response team posting the following statement on Twitter: "we are working to address a vulnerability believed to be connected to the Duqu malware."