A prison work program that involves inmates recycling old computer parts might sound like a good idea, but a couple of incarcerated criminals used it to build two working PCs and hide them in the ceiling of a training room.
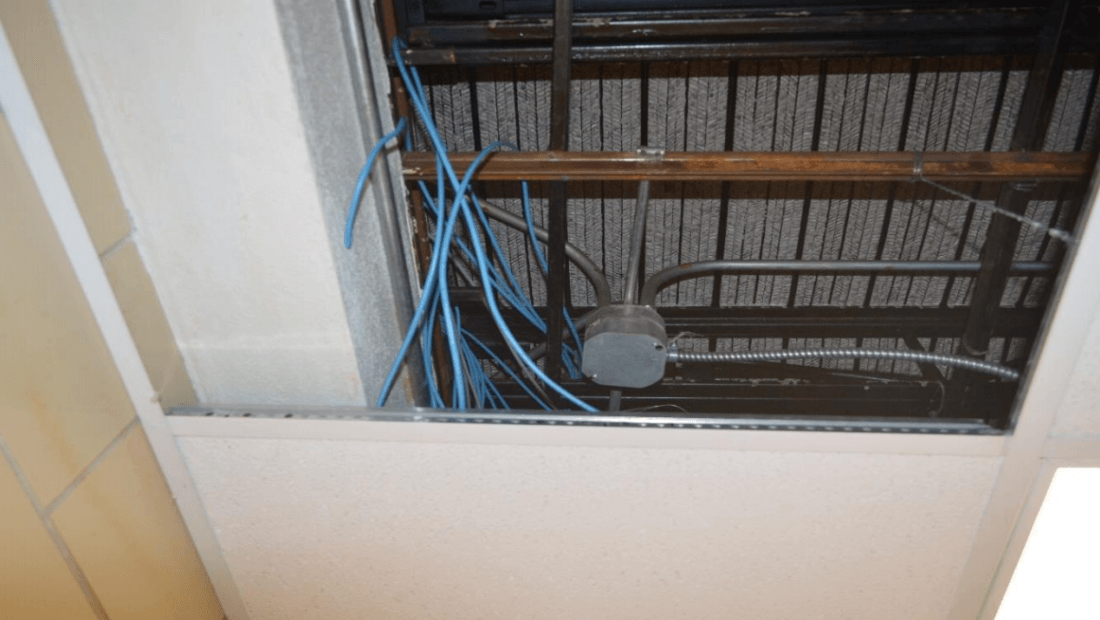
The Marion Correctional Institute in Ohio recycles the computers as part of the non-profit RET3 program. But for Adam Johnston and Scott Spriggs, it was an opportunity to commit more crimes while in the prison. The unsupervised pair were able to sneak away some of the computer parts, using them to build two working machines that were "hidden on a plywood board in the ceiling above a closet." Once constructed, they "connected to [Ohio Department of Rehabilitation and Correction's] computer network."
The convicts even managed to run an ethernet cable from the ceiling to the network switch, where it was connected to port 16. By using credentials belonging to a retired prison employee who'd become an ODRC contractor, they obtained internet access.
When examining the PCs, investigators found "password-cracking tools, virtual private network (VPN) tools, network enumeration tools, hand-crafted software, numerous proxy tools, and other software used for various types of malicious activity." There was also "self-signed certificates, Pidgin chat accounts, Tor sites, Tor geo exit nodes, ether soft, virtual phone, pornography, videos, VideoLan, and other various software." As well as articles on bomb-making, cooking up drugs, and credit card fraud.
"Findings of bitcoin wallets, stripe accounts, bank accounts, and credit card accounts point toward possible identity fraud, along with other possible cybercrimes," wrote the forensics team.
The prisoners even accessed the internal records of other inmates to issue them passes for gaining access to various areas of the prison. Fellow cons were also given thumb drives packed with porn.
The PCs were only discovered after a staff member was informed of excessive daily internet usage by the contractor whose credentials had been stolen. The automated message itself wasn't totally unusual, but it arrived on a day when the contractor wasn't working. Whoever was using the account had tried to access certain file-sharing sites but had been blocked by the prison network's proxy server, which denies access to certain online content, according to the BBC.
The user "then spent the next three hours straight trying to find sites that would circumvent the proxy and our policies," an email to IT employees noted.
All prisoners involved in the scheme have now been moved to other facilities. You can read the full 50-page report on the incident here.