The big picture: With the transition to a hybrid work model, security has become a much more complex problem that spans even more variables than before. Companies like Intel and AMD are now facing a wave of newly discovered firmware issues that cannot be patched soon enough.
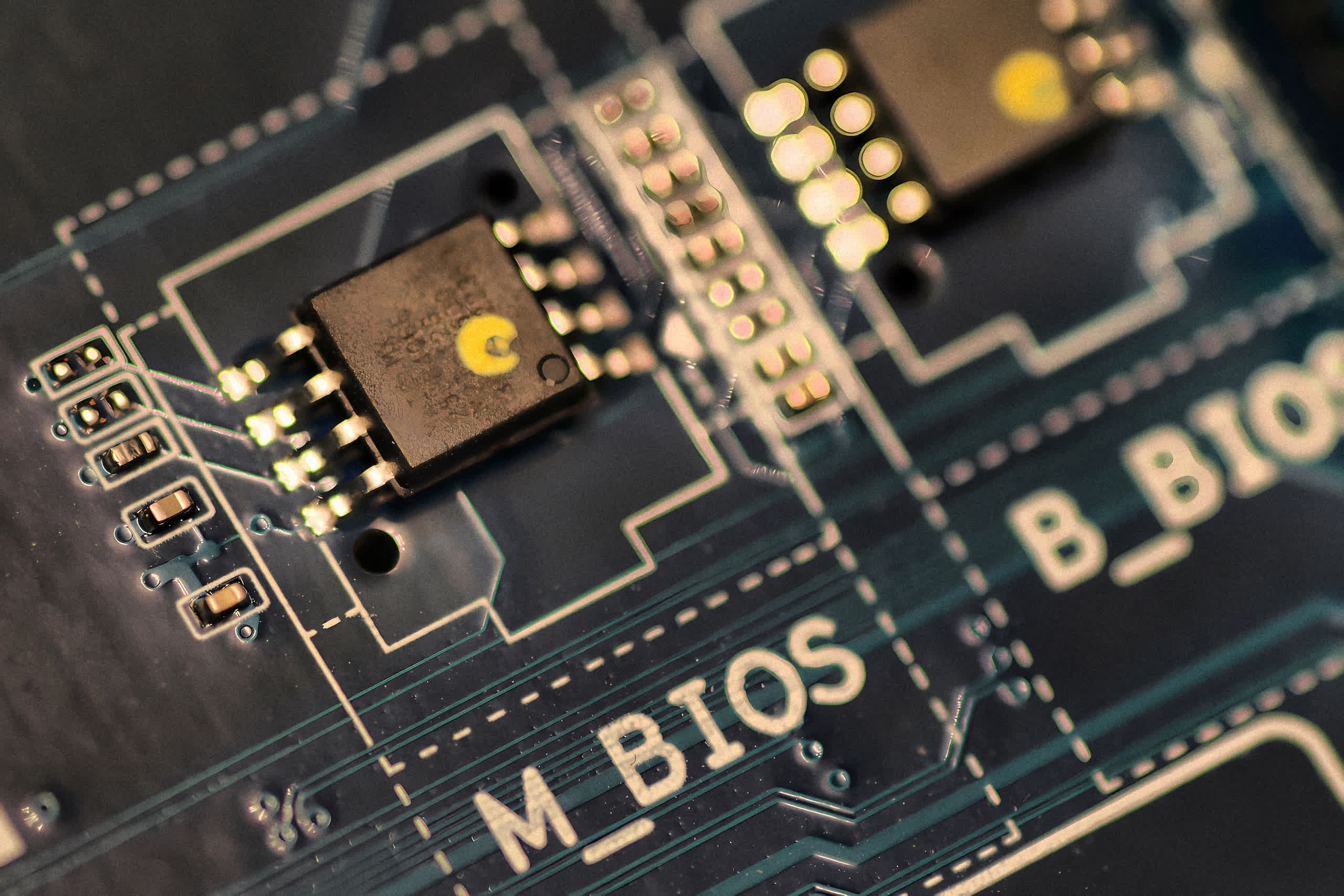
Intel says it has discovered no less than 16 new BIOS/UEFI vulnerabilities that allow malicious actors to perform escalation of privilege and denial of service attacks on affected systems. That means they can be leveraged to bypass many operating system protections as well as traditional endpoint security solutions, allowing hackers to extract sensitive information or lock it with ransomware.
Most of the flaws have a high severity rating, while three are described as medium severity and one is low severity. Intel explains the impacted systems include those powered by 6th to 11th generation Core processors, Xeon models from the W, E, D, and Scalable families, Core X-Series, and models from the Atom C3XXX family.

The good news is that none of the flaws can be exploited by an attacker unless they have physical access to the target machine. However, they do pose a risk in the case of professionals using work-provided laptops.
Intel is currently working on coordinating firmware updates with several vendors to mitigate these issues, but there’s no clear release roadmap as of writing this. The company credits Hugo Magalhaes from Oracle for reporting half of the disclosed vulnerabilities.
It’s worth noting these flaws aren’t related to the BIOS/UEFI flaws disclosed earlier this month by security firm Binarly, which can be exploited remotely and allow attackers to bypass hardware security features on affected systems.
https://www.techspot.com/news/93330-intel-issues-advisory-16-new-firmware-vulnerabilities.html