A hot potato: In early July, hackers hit remote management and IT platform Kaseya with a ransomware attack from the REvil ransomware gang. Towards the end of that month, it received a decryption key from the FBI, used to unlock the victims' systems. Earlier this month, security firm Bitdefender released a universal decryptor to help those affected. This week, current and former US officials told the Washington Post that the FBI held the key back for almost three weeks, during which some victims suffered.

Soon after Kaseya reported the attack by REvil on July 2, the Federal Bureau of Investigation got the decryption key for the ransomware by accessing that gang's servers. In agreement with other agencies, the FBI initially withheld the key because it was planning an operation to disrupt REvil, and was afraid using the key to help victims would've tipped off the gang. However, REvil disappeared on July 13, before the FBI could enact its plan. According to the Washington Post, that disappearance was not due to any US government action.
"The questions we ask each time are: What would be the value of a key if disclosed? How many victims are there? Who could be helped?" an anonymous source told the Washington Post. "And on the flip side, what would be the value of a potential longer-term operation in disrupting an ecosystem? Those are the questions we will continue to have to balance."
The FBI shared the key with Kaseya on July 21, and security firm Emsisoft was able to use it to have a decryption tool ready by the following day. FBI Director Christopher Wray suggested at a Senate Homeland Security Committee hearing that the decryptor also needed to be tested and validated. However, Emsisoft Chief Technology Officer Fabian Wosar claimed that the company took less than 10 minutes to test it once it received the key. In the worst-case scenario, it would have taken about four hours, the CTO said.
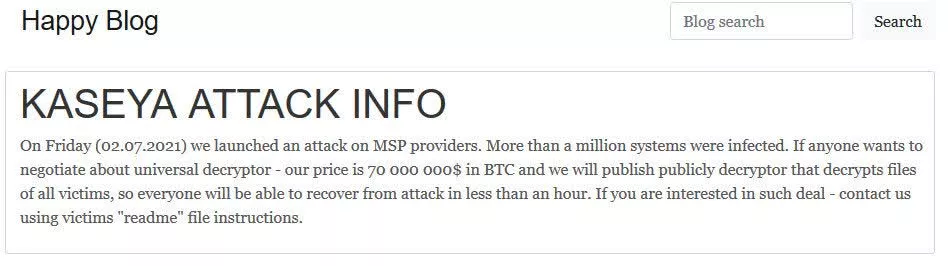
Image courtesy of Bleeping Computer
Although assessments from Kaseya and the US government determined the damage from REvil's attack was lighter than initially feared, it still brought a substantial cost to some victims during the period before the FBI released the key.
"The decryptor key would have been nice three weeks before we got it, but we had already begun a complete restoration of our clients' systems," Maryland IT company JustTech owner Joshua Justice told the Washington Post.
JustTech is one of Kaseya's clients affected by the attack, and about 120 of JustTech's consumers were also affected.
"I had grown individuals crying to me in person and over the phone asking if their business was going to continue," JustTech related. "I had one man say, 'Should I just retire? Should I let my employees go?'"
Bitdefender's universal decryptor should help any victim hit before REvil's July 13th disappearance. Sources told the Washington Post the law enforcement agency which Bitdefender worked with to release the decryptor was not the FBI.
REvil has since reappeared and has already announced new victims. The universal decryptor doesn't work for victims of those more recent attacks.
https://www.techspot.com/news/91402-fbi-withheld-ransomware-decryption-key-weeks-run-operation.html