Well, that was fast. Less than a week after reports emerged about a workaround to allow any unsigned ARM-based application run on Windows RT, a senior member at the XDA-Developers forums has crafted a jailbreak tool that automates the process and makes it accessible to non-technical users.
As originally reported, the restriction of installing only Metro-style apps on Windows RT is enforced through a code integrity mechanism that checks the application's signature before allowing it to be installed. This mechanism is hardcoded in the kernel itself and cannot be modified permanently in systems using UEFI Secure Boot. But it can be changed in memory after locating the setting in question.
The Windows RT jailbreak tool is based on the same tethered technique demonstrated by the hacker clrokr. That means it will need to be reapplied each time the machine is rebooted, but it will save you from having to poke around the Windows kernel. It simply runs and unlocks your Windows RT device.
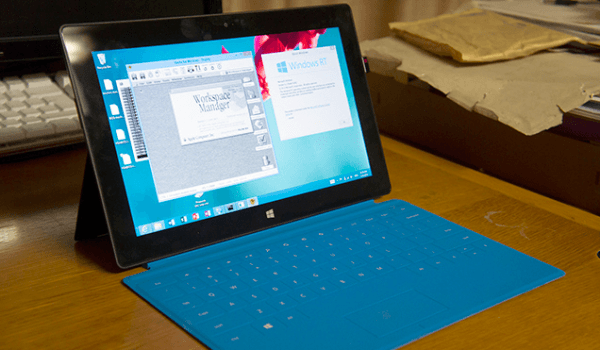
It should be noted that x86 desktop programs can't simply be installed on Windows RT with this hack, they need to be recompiled for the ARM architecture. Nevertheless the hack and jailbreak tool open up possibilities for a homebrew scene of desktop apps – there are already nine desktop apps available over at XDA. Someone even got an early version of Apple's OS X server running on a Surface RT tablet.
It remains to be seen if Microsoft plans decides to issue a patch for its ARM-based operating system or embrace the homebrew community. Earlier this week the company issued a statement saying it does not consider the findings to be part of a security vulnerability, and applauded the hacker for his ingenuity.