Thank you. here are the logs.
Malwarebytes Anti-Malware 1.65.0.1400
www.malwarebytes.org
Database version: v2012.10.06.05
Windows 7 Service Pack 1 x86 NTFS
Internet Explorer 8.0.7601.17514
stewart :: STEWART-PC [administrator]
10/6/2012 5:38:04 PM
mbam-log-2012-10-06 (17-38-04).txt
Scan type: Quick scan
Scan options enabled: Memory | Startup | Registry | File System | Heuristics/Extra | Heuristics/Shuriken | PUP | PUM
Scan options disabled: P2P
Objects scanned: 238088
Time elapsed: 7 minute(s), 17 second(s)
Memory Processes Detected: 0
(No malicious items detected)
Memory Modules Detected: 0
(No malicious items detected)
Registry Keys Detected: 0
(No malicious items detected)
Registry Values Detected: 0
(No malicious items detected)
Registry Data Items Detected: 0
(No malicious items detected)
Folders Detected: 0
(No malicious items detected)
Files Detected: 1
E:\Users\stewart\Downloads\tvshows_2905.exe (PUP.BundleOffers.IIQ) -> Quarantined and deleted successfully.
(end)
_____________________________
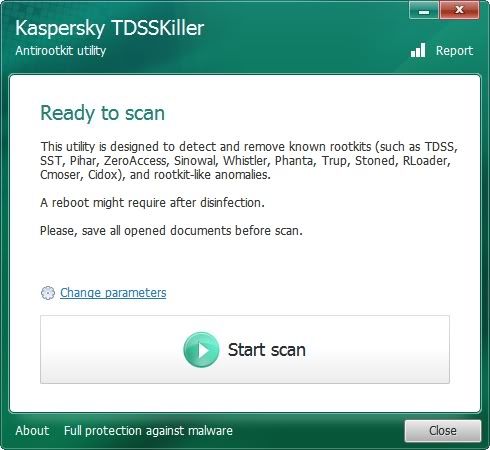
17:32:06.0566 5956 TDSS rootkit removing tool 2.8.10.0 Sep 17 2012 19:23:24
17:32:07.0658 5956 ============================================================
17:32:07.0658 5956 Current date / time: 2012/10/06 17:32:07.0658
17:32:07.0658 5956 SystemInfo:
17:32:07.0658 5956
17:32:07.0658 5956 OS Version: 6.1.7601 ServicePack: 1.0
17:32:07.0658 5956 Product type: Workstation
17:32:07.0658 5956 ComputerName: STEWART-PC
17:32:07.0658 5956 UserName: stewart
17:32:07.0658 5956 Windows directory: E:\Windows
17:32:07.0658 5956 System windows directory: E:\Windows
17:32:07.0658 5956 Processor architecture: Intel x86
17:32:07.0658 5956 Number of processors: 2
17:32:07.0658 5956 Page size: 0x1000
17:32:07.0658 5956 Boot type: Normal boot
17:32:07.0658 5956 ============================================================
17:32:13.0478 5956 BG loaded
17:32:14.0836 5956 Drive \Device\Harddisk0\DR0 - Size: 0x3A38B2E000 (232.89 Gb), SectorSize: 0x200, Cylinders: 0x76C1, SectorsPerTrack: 0x3F, TracksPerCylinder: 0xFF, Type 'K0', Flags 0x00000050
17:32:14.0914 5956 ============================================================
17:32:14.0914 5956 \Device\Harddisk0\DR0:
17:32:14.0945 5956 MBR partitions:
17:32:14.0945 5956 \Device\Harddisk0\DR0\Partition1: MBR, Type 0x7, StartLBA 0x3F, BlocksNum 0x1388AFC
17:32:14.0945 5956 \Device\Harddisk0\DR0\Partition2: MBR, Type 0x7, StartLBA 0x1389000, BlocksNum 0x1BE3C000
17:32:14.0945 5956 ============================================================
17:32:15.0304 5956 C: <-> \Device\Harddisk0\DR0\Partition1
17:32:15.0850 5956 E: <-> \Device\Harddisk0\DR0\Partition2
17:32:15.0850 5956 ============================================================
17:32:15.0850 5956 Initialize success
17:32:15.0850 5956 ============================================================
17:32:53.0388 5164 ============================================================
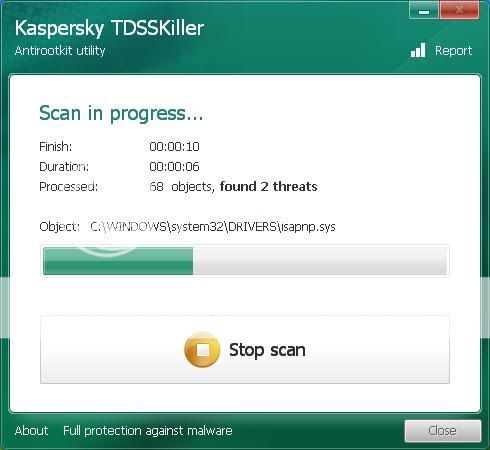
17:32:53.0388 5164 Scan started
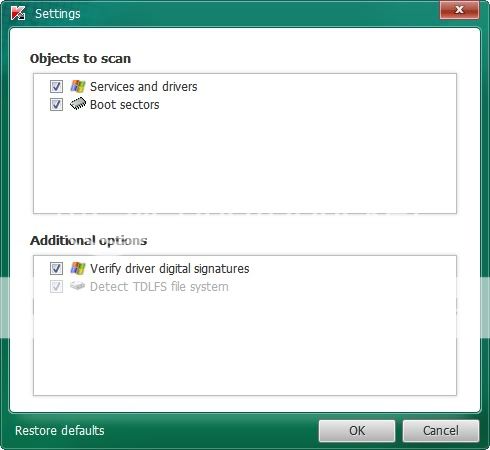
17:32:53.0388 5164 Mode: Manual; SigCheck; TDLFS;
17:32:53.0388 5164 ============================================================
17:32:55.0026 5164 ================ Scan system memory ========================
17:32:55.0026 5164 System memory - ok
17:32:55.0026 5164 ================ Scan services =============================
17:32:55.0400 5164 [ 1B133875B8AA8AC48969BD3458AFE9F5 ] 1394ohci E:\Windows\system32\DRIVERS\1394ohci.sys
17:32:55.0603 5164 1394ohci - ok
17:32:55.0666 5164 58789744 - ok
17:32:55.0759 5164 [ CEA80C80BED809AA0DA6FEBC04733349 ] ACPI E:\Windows\system32\drivers\ACPI.sys
17:32:55.0775 5164 ACPI - ok
17:32:55.0853 5164 [ 1EFBC664ABFF416D1D07DB115DCB264F ] AcpiPmi E:\Windows\system32\drivers\acpipmi.sys
17:32:55.0993 5164 AcpiPmi - ok
17:32:56.0258 5164 [ D19C4EE2AC7C47B8F5F84FFF1A789D8A ] AdobeARMservice E:\Program Files\Common Files\Adobe\ARM\1.0\armsvc.exe
17:32:56.0274 5164 AdobeARMservice - ok
17:32:56.0477 5164 [ E12CFCF1DDBFC50948A75E6E38793225 ] AdobeFlashPlayerUpdateSvc E:\Windows\system32\Macromed\Flash\FlashPlayerUpdateService.exe
17:32:56.0492 5164 AdobeFlashPlayerUpdateSvc - ok
17:32:56.0617 5164 [ 21E785EBD7DC90A06391141AAC7892FB ] adp94xx E:\Windows\system32\drivers\adp94xx.sys
17:32:56.0664 5164 adp94xx - ok
17:32:56.0726 5164 [ 0C676BC278D5B59FF5ABD57BBE9123F2 ] adpahci E:\Windows\system32\drivers\adpahci.sys
17:32:56.0758 5164 adpahci - ok
17:32:56.0836 5164 [ 7C7B5EE4B7B822EC85321FE23A27DB33 ] adpu320 E:\Windows\system32\drivers\adpu320.sys
17:32:56.0867 5164 adpu320 - ok
17:32:56.0960 5164 [ 8B5EEFEEC1E6D1A72A06C526628AD161 ] AeLookupSvc E:\Windows\System32\aelupsvc.dll
17:32:57.0132 5164 AeLookupSvc - ok
17:32:57.0148 5164 [ 1151FD4FB0216CFED887BFDE29EBD516 ] AFD E:\Windows\system32\drivers\afd.sys
17:32:57.0226 5164 AFD - ok
17:32:57.0257 5164 [ 507812C3054C21CEF746B6EE3D04DD6E ] agp440 E:\Windows\system32\drivers\agp440.sys
17:32:57.0288 5164 agp440 - ok
17:32:57.0366 5164 [ 8B30250D573A8F6B4BD23195160D8707 ] aic78xx E:\Windows\system32\drivers\djsvs.sys
17:32:57.0413 5164 aic78xx - ok
17:32:57.0631 5164 [ 18A54E132947CD98FEA9ACCC57F98F13 ] ALG E:\Windows\System32\alg.exe
17:32:57.0678 5164 ALG - ok
17:32:57.0725 5164 [ 0D40BCF52EA90FC7DF2AEAB6503DEA44 ] aliide E:\Windows\system32\drivers\aliide.sys
17:32:57.0787 5164 aliide - ok
17:32:57.0818 5164 [ 3C6600A0696E90A463771C7422E23AB5 ] amdagp E:\Windows\system32\drivers\amdagp.sys
17:32:57.0850 5164 amdagp - ok
17:32:57.0865 5164 [ CD5914170297126B6266860198D1D4F0 ] amdide E:\Windows\system32\drivers\amdide.sys
17:32:57.0881 5164 amdide - ok
17:32:57.0959 5164 [ 00DDA200D71BAC534BF56A9DB5DFD666 ] AmdK8 E:\Windows\system32\drivers\amdk8.sys
17:32:58.0021 5164 AmdK8 - ok
17:32:58.0052 5164 [ 3CBF30F5370FDA40DD3E87DF38EA53B6 ] AmdPPM E:\Windows\system32\drivers\amdppm.sys
17:32:58.0115 5164 AmdPPM - ok
17:32:58.0193 5164 [ E7F4D42D8076EC60E21715CD11743A0D ] amdsata E:\Windows\system32\drivers\amdsata.sys
17:32:58.0224 5164 amdsata - ok
17:32:58.0302 5164 [ EA43AF0C423FF267355F74E7A53BDABA ] amdsbs E:\Windows\system32\drivers\amdsbs.sys
17:32:58.0349 5164 amdsbs - ok
17:32:58.0380 5164 [ 146459D2B08BFDCBFA856D9947043C81 ] amdxata E:\Windows\system32\drivers\amdxata.sys
17:32:58.0396 5164 amdxata - ok
17:32:58.0458 5164 [ AEA177F783E20150ACE5383EE368DA19 ] AppID E:\Windows\system32\drivers\appid.sys
17:32:58.0567 5164 AppID - ok
17:32:58.0598 5164 [ 62A9C86CB6085E20DB4823E4E97826F5 ] AppIDSvc E:\Windows\System32\appidsvc.dll
17:32:58.0692 5164 AppIDSvc - ok
17:32:58.0754 5164 [ FB1959012294D6AD43E5304DF65E3C26 ] Appinfo E:\Windows\System32\appinfo.dll
17:32:58.0832 5164 Appinfo - ok
17:32:58.0910 5164 [ 7EF47644B74EBE721CC32211D3C35E76 ] Apple Mobile Device E:\Program Files\Common Files\Apple\Mobile Device Support\AppleMobileDeviceService.exe
17:32:58.0926 5164 Apple Mobile Device - ok
17:32:59.0035 5164 [ A45D184DF6A8803DA13A0B329517A64A ] AppMgmt E:\Windows\System32\appmgmts.dll
17:32:59.0098 5164 AppMgmt - ok
17:32:59.0176 5164 [ 2932004F49677BD84DBC72EDB754FFB3 ] arc E:\Windows\system32\drivers\arc.sys
17:32:59.0191 5164 arc - ok
17:32:59.0222 5164 [ 5D6F36C46FD283AE1B57BD2E9FEB0BC7 ] arcsas E:\Windows\system32\drivers\arcsas.sys
17:32:59.0238 5164 arcsas - ok
17:32:59.0300 5164 [ ADD2ADE1C2B285AB8378D2DAAF991481 ] AsyncMac E:\Windows\system32\DRIVERS\asyncmac.sys
17:32:59.0441 5164 AsyncMac - ok
17:32:59.0472 5164 [ 338C86357871C167A96AB976519BF59E ] atapi E:\Windows\system32\drivers\atapi.sys
17:32:59.0488 5164 atapi - ok
17:32:59.0644 5164 [ 3426386F125DD820E0651E5833F9849B ] athur E:\Windows\system32\DRIVERS\athur.sys
17:32:59.0706 5164 athur - ok
17:32:59.0831 5164 [ CE3B4E731638D2EF62FCB419BE0D39F0 ] AudioEndpointBuilder E:\Windows\System32\Audiosrv.dll
17:32:59.0893 5164 AudioEndpointBuilder - ok
17:32:59.0924 5164 [ CE3B4E731638D2EF62FCB419BE0D39F0 ] Audiosrv E:\Windows\System32\Audiosrv.dll
17:32:59.0971 5164 Audiosrv - ok
17:33:00.0907 5164 [ D67719BCFDE5798F5C30D14EFED3BCAF ] AVGIDSAgent E:\Program Files\AVG\AVG2012\avgidsagent.exe
17:33:01.0219 5164 AVGIDSAgent - ok
17:33:01.0297 5164 [ EA1145DEBCD508FD25BD1E95C4346929 ] avgwd E:\Program Files\AVG\AVG2012\avgwdsvc.exe
17:33:01.0344 5164 avgwd - ok
17:33:01.0422 5164 [ 6E30D02AAC9CAC84F421622E3A2F6178 ] AxInstSV E:\Windows\System32\AxInstSV.dll
17:33:01.0500 5164 AxInstSV - ok
17:33:01.0640 5164 [ 1A231ABEC60FD316EC54C66715543CEC ] b06bdrv E:\Windows\system32\drivers\bxvbdx.sys
17:33:01.0734 5164 b06bdrv - ok
17:33:01.0828 5164 [ BD8869EB9CDE6BBE4508D869929869EE ] b57nd60x E:\Windows\system32\DRIVERS\b57nd60x.sys
17:33:01.0874 5164 b57nd60x - ok
17:33:01.0968 5164 [ 5E27B4D15C7DF6365C696DC9010187A4 ] bckd E:\Windows\system32\drivers\bckd.sys
17:33:01.0984 5164 bckd - ok
17:33:02.0155 5164 [ 2A113172238EB26D09A91578A9443846 ] bckwfs E:\Program Files\Blue Coat K9 Web Protection\k9filter.exe
17:33:02.0202 5164 bckwfs - ok
17:33:02.0297 5164 [ EE1E9C3BB8228AE423DD38DB69128E71 ] BDESVC E:\Windows\System32\bdesvc.dll
17:33:02.0390 5164 BDESVC - ok
17:33:02.0453 5164 [ 505506526A9D467307B3C393DEDAF858 ] Beep E:\Windows\system32\drivers\Beep.sys
17:33:02.0546 5164 Beep - ok
17:33:02.0718 5164 [ 1E2BAC209D184BB851E1A187D8A29136 ] BFE E:\Windows\System32\bfe.dll
17:33:02.0811 5164 BFE - ok
17:33:03.0248 5164 [ E585445D5021971FAE10393F0F1C3961 ] BITS E:\Windows\System32\qmgr.dll
17:33:03.0311 5164 BITS - ok
17:33:03.0357 5164 [ 2287078ED48FCFC477B05B20CF38F36F ] blbdrive E:\Windows\system32\DRIVERS\blbdrive.sys
17:33:03.0404 5164 blbdrive - ok
17:33:03.0576 5164 [ DB5BEA73EDAF19AC68B2C0FAD0F92B1A ] Bonjour Service E:\Program Files\Bonjour\mDNSResponder.exe
17:33:03.0607 5164 Bonjour Service - ok
17:33:03.0638 5164 [ FCAFAEF6798D7B51FF029F99A9898961 ] bowser E:\Windows\system32\DRIVERS\bowser.sys
17:33:03.0716 5164 bowser - ok
17:33:03.0763 5164 [ 9F9ACC7F7CCDE8A15C282D3F88B43309 ] BrFiltLo E:\Windows\system32\drivers\BrFiltLo.sys
17:33:03.0810 5164 BrFiltLo - ok
17:33:03.0857 5164 [ 56801AD62213A41F6497F96DEE83755A ] BrFiltUp E:\Windows\system32\drivers\BrFiltUp.sys
17:33:03.0919 5164 BrFiltUp - ok
17:33:03.0981 5164 [ 77361D72A04F18809D0EFB6CCEB74D4B ] BridgeMP E:\Windows\system32\DRIVERS\bridge.sys
17:33:04.0059 5164 BridgeMP - ok
17:33:04.0106 5164 [ 6E11F33D14D020F58D5E02E4D67DFA19 ] Browser E:\Windows\System32\browser.dll
17:33:04.0184 5164 Browser - ok
17:33:04.0231 5164 [ 845B8CE732E67F3B4133164868C666EA ] Brserid E:\Windows\System32\Drivers\Brserid.sys
17:33:04.0278 5164 Brserid - ok
17:33:04.0293 5164 [ 203F0B1E73ADADBBB7B7B1FABD901F6B ] BrSerWdm E:\Windows\System32\Drivers\BrSerWdm.sys
17:33:04.0356 5164 BrSerWdm - ok
17:33:04.0387 5164 [ BD456606156BA17E60A04E18016AE54B ] BrUsbMdm E:\Windows\System32\Drivers\BrUsbMdm.sys
17:33:04.0481 5164 BrUsbMdm - ok
17:33:04.0512 5164 [ AF72ED54503F717A43268B3CC5FAEC2E ] BrUsbSer E:\Windows\System32\Drivers\BrUsbSer.sys
17:33:04.0559 5164 BrUsbSer - ok
17:33:04.0605 5164 [ ED3DF7C56CE0084EB2034432FC56565A ] BTHMODEM E:\Windows\system32\drivers\bthmodem.sys
17:33:04.0637 5164 BTHMODEM - ok
17:33:04.0715 5164 [ 1DF19C96EEF6C29D1C3E1A8678E07190 ] bthserv E:\Windows\system32\bthserv.dll
17:33:04.0793 5164 bthserv - ok
17:33:04.0949 5164 catchme - ok
17:33:05.0027 5164 [ 77EA11B065E0A8AB902D78145CA51E10 ] cdfs E:\Windows\system32\DRIVERS\cdfs.sys
17:33:05.0120 5164 cdfs - ok
17:33:05.0183 5164 [ BE167ED0FDB9C1FA1133953C18D5A6C9 ] cdrom E:\Windows\system32\DRIVERS\cdrom.sys
17:33:05.0229 5164 cdrom - ok
17:33:05.0307 5164 [ 319C6B309773D063541D01DF8AC6F55F ] CertPropSvc E:\Windows\System32\certprop.dll
17:33:05.0385 5164 CertPropSvc - ok
17:33:05.0432 5164 [ 3FE3FE94A34DF6FB06E6418D0F6A0060 ] circlass E:\Windows\system32\drivers\circlass.sys
17:33:05.0463 5164 circlass - ok
17:33:05.0495 5164 [ 635181E0E9BBF16871BF5380D71DB02D ] CLFS E:\Windows\system32\CLFS.sys
17:33:05.0526 5164 CLFS - ok
17:33:05.0838 5164 [ D88040F816FDA31C3B466F0FA0918F29 ] clr_optimization_v2.0.50727_32 E:\Windows\Microsoft.NET\Framework\v2.0.50727\mscorsvw.exe
17:33:05.0853 5164 clr_optimization_v2.0.50727_32 - ok
17:33:05.0885 5164 [ DEA805815E587DAD1DD2C502220B5616 ] CmBatt E:\Windows\system32\DRIVERS\CmBatt.sys
17:33:05.0947 5164 CmBatt - ok
17:33:05.0978 5164 [ C537B1DB64D495B9B4717B4D6D9EDBF2 ] cmdide E:\Windows\system32\drivers\cmdide.sys
17:33:06.0009 5164 cmdide - ok
17:33:06.0056 5164 [ 1B675691ED940766149C93E8F4488D68 ] CNG E:\Windows\system32\Drivers\cng.sys
17:33:06.0150 5164 CNG - ok
17:33:06.0228 5164 [ A6023D3823C37043986713F118A89BEE ] Compbatt E:\Windows\system32\DRIVERS\compbatt.sys
17:33:06.0243 5164 Compbatt - ok
17:33:06.0306 5164 [ CBE8C58A8579CFE5FCCF809E6F114E89 ] CompositeBus E:\Windows\system32\DRIVERS\CompositeBus.sys
17:33:06.0337 5164 CompositeBus - ok
17:33:06.0462 5164 COMSysApp - ok
17:33:06.0493 5164 [ 2C4EBCFC84A9B44F209DFF6C6E6C61D1 ] crcdisk E:\Windows\system32\drivers\crcdisk.sys
17:33:06.0524 5164 crcdisk - ok
17:33:06.0649 5164 [ A585BEBF7D054BD9618EDA0922D5484A ] CryptSvc E:\Windows\system32\cryptsvc.dll
17:33:06.0727 5164 CryptSvc - ok
17:33:06.0836 5164 [ 3C2177A897B4CA2788C6FB0C3FD81D4B ] CSC E:\Windows\system32\drivers\csc.sys
17:33:06.0930 5164 CSC - ok
17:33:07.0023 5164 [ 15F93B37F6801943360D9EB42485D5D3 ] CscService E:\Windows\System32\cscsvc.dll
17:33:07.0101 5164 CscService - ok
17:33:07.0226 5164 [ 0732328832DE5D31A5FFAF3BA99B9DB7 ] dalwdmservice E:\Windows\system32\drivers\dalwdm.sys
17:33:07.0242 5164 dalwdmservice - ok
17:33:07.0320 5164 [ 7660F01D3B38ACA1747E397D21D790AF ] DcomLaunch E:\Windows\system32\rpcss.dll
17:33:07.0445 5164 DcomLaunch - ok
17:33:07.0491 5164 [ 8D6E10A2D9A5EED59562D9B82CF804E1 ] defragsvc E:\Windows\System32\defragsvc.dll
17:33:07.0585 5164 defragsvc - ok
17:33:07.0647 5164 [ F024449C97EC1E464AAFFDA18593DB88 ] DfsC E:\Windows\system32\Drivers\dfsc.sys
17:33:07.0741 5164 DfsC - ok
17:33:07.0850 5164 [ E9E01EB683C132F7FA27CD607B8A2B63 ] Dhcp E:\Windows\system32\dhcpcore.dll
17:33:07.0928 5164 Dhcp - ok
17:33:08.0053 5164 [ E70AC14F6ADDCC9589CF513AF725178C ] DigiNet E:\Windows\system32\DRIVERS\diginet.sys
17:33:08.0053 5164 DigiNet - ok
17:33:08.0303 5164 DigiRefresh - ok
17:33:08.0521 5164 [ 52E112E8B13522352DB42B78AC9BAB0C ] digiSPTIService E:\Program Files\Digidesign\Pro Tools\digiSPTIService.exe
17:33:08.0630 5164 digiSPTIService ( UnsignedFile.Multi.Generic ) - warning
17:33:08.0630 5164 digiSPTIService - detected UnsignedFile.Multi.Generic (1)
17:33:08.0661 5164 [ 1A050B0274BFB3890703D490F330C0DA ] discache E:\Windows\system32\drivers\discache.sys
17:33:08.0739 5164 discache - ok
17:33:08.0849 5164 [ 565003F326F99802E68CA78F2A68E9FF ] Disk E:\Windows\system32\drivers\disk.sys
17:33:08.0864 5164 Disk - ok
17:33:09.0566 5164 [ 0037AC70A244EAE245C46A89A7B446DD ] DisplayLinkService E:\Program Files\DisplayLink Core Software\DisplayLinkManager.exe
17:33:09.0800 5164 DisplayLinkService - ok
17:33:09.0941 5164 [ 2A958EF85DB1B61FFCA65044FA4BCE9E ] dmvsc E:\Windows\system32\drivers\dmvsc.sys
17:33:10.0050 5164 dmvsc - ok
17:33:10.0159 5164 [ 2FE30D71919C51131405797620E0A714 ] Dnscache E:\Windows\System32\dnsrslvr.dll
17:33:10.0253 5164 Dnscache - ok
17:33:10.0331 5164 [ 366BA8FB4B7BB7435E3B9EACB3843F67 ] dot3svc E:\Windows\System32\dot3svc.dll
17:33:10.0424 5164 dot3svc - ok
17:33:10.0471 5164 [ 8EC04CA86F1D68DA9E11952EB85973D6 ] DPS E:\Windows\system32\dps.dll
17:33:10.0565 5164 DPS - ok
17:33:10.0736 5164 [ B918E7C5F9BF77202F89E1A9539F2EB4 ] drmkaud E:\Windows\system32\drivers\drmkaud.sys
17:33:10.0783 5164 drmkaud - ok
17:33:10.0877 5164 [ 23F5D28378A160352BA8F817BD8C71CB ] DXGKrnl E:\Windows\System32\drivers\dxgkrnl.sys
17:33:10.0923 5164 DXGKrnl - ok
17:33:11.0017 5164 [ 8600142FA91C1B96367D3300AD0F3F3A ] EapHost E:\Windows\System32\eapsvc.dll
17:33:11.0142 5164 EapHost - ok
17:33:11.0469 5164 [ 024E1B5CAC09731E4D868E64DBFB4AB0 ] ebdrv E:\Windows\system32\drivers\evbdx.sys
17:33:11.0657 5164 ebdrv - ok
17:33:11.0797 5164 [ F42309C4191C506B71DB5D1126D26318 ] EFS E:\Windows\System32\lsass.exe
17:33:11.0875 5164 EFS - ok
17:33:11.0984 5164 [ A8C362018EFC87BEB013EE28F29C0863 ] ehRecvr E:\Windows\ehome\ehRecvr.exe
17:33:12.0062 5164 ehRecvr - ok
17:33:12.0078 5164 [ D389BFF34F80CAEDE417BF9D1507996A ] ehSched E:\Windows\ehome\ehsched.exe
17:33:12.0499 5164 ehSched - ok
17:33:12.0577 5164 [ 0ED67910C8C326796FAA00B2BF6D9D3C ] elxstor E:\Windows\system32\drivers\elxstor.sys
17:33:12.0639 5164 elxstor - ok
17:33:12.0671 5164 [ 8FC3208352DD3912C94367A206AB3F11 ] ErrDev E:\Windows\system32\drivers\errdev.sys
17:33:12.0717 5164 ErrDev - ok
17:33:12.0811 5164 [ F6916EFC29D9953D5D0DF06882AE8E16 ] EventSystem E:\Windows\system32\es.dll
17:33:12.0873 5164 EventSystem - ok
17:33:12.0936 5164 [ 2DC9108D74081149CC8B651D3A26207F ] exfat E:\Windows\system32\drivers\exfat.sys
17:33:12.0983 5164 exfat - ok
17:33:13.0029 5164 [ 7E0AB74553476622FB6AE36F73D97D35 ] fastfat E:\Windows\system32\drivers\fastfat.sys
17:33:13.0107 5164 fastfat - ok
17:33:13.0201 5164 [ 967EA5B213E9984CBE270205DF37755B ] Fax E:\Windows\system32\fxssvc.exe
17:33:13.0295 5164 Fax - ok
17:33:13.0357 5164 [ E817A017F82DF2A1F8CFDBDA29388B29 ] fdc E:\Windows\system32\drivers\fdc.sys
17:33:13.0497 5164 fdc - ok
17:33:13.0653 5164 [ F3222C893BD2F5821A0179E5C71E88FB ] fdPHost E:\Windows\system32\fdPHost.dll
17:33:13.0747 5164 fdPHost - ok
17:33:13.0778 5164 [ 7DBE8CBFE79EFBDEB98C9FB08D3A9A5B ] FDResPub E:\Windows\system32\fdrespub.dll
17:33:13.0872 5164 FDResPub - ok
17:33:13.0903 5164 [ 6CF00369C97F3CF563BE99BE983D13D8 ] FileInfo E:\Windows\system32\drivers\fileinfo.sys
17:33:13.0981 5164 FileInfo - ok
17:33:14.0043 5164 [ 42C51DC94C91DA21CB9196EB64C45DB9 ] Filetrace E:\Windows\system32\drivers\filetrace.sys
17:33:14.0153 5164 Filetrace - ok
17:33:14.0184 5164 [ 87907AA70CB3C56600F1C2FB8841579B ] flpydisk E:\Windows\system32\drivers\flpydisk.sys
17:33:14.0246 5164 flpydisk - ok
17:33:14.0355 5164 [ 7520EC808E0C35E0EE6F841294316653 ] FltMgr E:\Windows\system32\drivers\fltmgr.sys
17:33:14.0511 5164 FltMgr - ok
17:33:14.0683 5164 [ FA6C66E4364D7DA57AADE5DCC03BB999 ] FontCache E:\Windows\system32\FntCache.dll
17:33:14.0808 5164 FontCache - ok
17:33:14.0933 5164 [ E56F39F6B7FDA0AC77A79B0FD3DE1A2F ] FontCache3.0.0.0 E:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe
17:33:14.0948 5164 FontCache3.0.0.0 - ok
17:33:14.0979 5164 [ 1A16B57943853E598CFF37FE2B8CBF1D ] FsDepends E:\Windows\system32\drivers\FsDepends.sys
17:33:14.0995 5164 FsDepends - ok
17:33:15.0073 5164 [ A574B4360E438977038AAE4BF60D79A2 ] Fs_Rec E:\Windows\system32\drivers\Fs_Rec.sys
17:33:15.0104 5164 Fs_Rec - ok
17:33:15.0151 5164 [ 8A73E79089B282100B9393B644CB853B ] fvevol E:\Windows\system32\DRIVERS\fvevol.sys
17:33:15.0182 5164 fvevol - ok
17:33:15.0276 5164 [ 65EE0C7A58B65E74AE05637418153938 ] gagp30kx E:\Windows\system32\drivers\gagp30kx.sys
17:33:15.0307 5164 gagp30kx - ok
17:33:15.0401 5164 [ 8182FF89C65E4D38B2DE4BB0FB18564E ] GEARAspiWDM E:\Windows\system32\DRIVERS\GEARAspiWDM.sys
17:33:15.0416 5164 GEARAspiWDM - ok
17:33:15.0463 5164 [ E897EAF5ED6BA41E081060C9B447A673 ] gpsvc E:\Windows\System32\gpsvc.dll
17:33:15.0541 5164 gpsvc - ok
17:33:15.0635 5164 [ 506708142BC63DABA64F2D3AD1DCD5BF ] gupdate E:\Program Files\Google\Update\GoogleUpdate.exe
17:33:15.0666 5164 gupdate - ok
17:33:15.0681 5164 [ 506708142BC63DABA64F2D3AD1DCD5BF ] gupdatem E:\Program Files\Google\Update\GoogleUpdate.exe
17:33:15.0697 5164 gupdatem - ok
17:33:15.0744 5164 [ 5D4BC124FAAE6730AC002CDB67BF1A1C ] gusvc E:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
17:33:15.0775 5164 gusvc - ok
17:33:15.0822 5164 [ C44E3C2BAB6837DB337DDEE7544736DB ] hcw85cir E:\Windows\system32\drivers\hcw85cir.sys
17:33:15.0853 5164 hcw85cir - ok
17:33:15.0978 5164 [ A5EF29D5315111C80A5C1ABAD14C8972 ] HdAudAddService E:\Windows\system32\drivers\HdAudio.sys
17:33:16.0040 5164 HdAudAddService - ok
17:33:16.0118 5164 [ 9036377B8A6C15DC2EEC53E489D159B5 ] HDAudBus E:\Windows\system32\DRIVERS\HDAudBus.sys
17:33:16.0165 5164 HDAudBus - ok
17:33:16.0243 5164 [ 1D58A7F3E11A9731D0EAAAA8405ACC36 ] HidBatt E:\Windows\system32\drivers\HidBatt.sys
17:33:16.0305 5164 HidBatt - ok
17:33:16.0337 5164 [ 89448F40E6DF260C206A193A4683BA78 ] HidBth E:\Windows\system32\drivers\hidbth.sys
17:33:16.0399 5164 HidBth - ok
17:33:16.0461 5164 [ CF50B4CF4A4F229B9F3C08351F99CA5E ] HidIr E:\Windows\system32\drivers\hidir.sys
17:33:16.0508 5164 HidIr - ok
17:33:16.0586 5164 [ 2BC6F6A1992B3A77F5F41432CA6B3B6B ] hidserv E:\Windows\System32\hidserv.dll
17:33:16.0664 5164 hidserv - ok
17:33:16.0727 5164 [ 10C19F8290891AF023EAEC0832E1EB4D ] HidUsb E:\Windows\system32\DRIVERS\hidusb.sys
17:33:16.0773 5164 HidUsb - ok
17:33:16.0836 5164 [ 196B4E3F4CCCC24AF836CE58FACBB699 ] hkmsvc E:\Windows\system32\kmsvc.dll
17:33:16.0883 5164 hkmsvc - ok
17:33:16.0914 5164 [ 6658F4404DE03D75FE3BA09F7ABA6A30 ] HomeGroupListener E:\Windows\system32\ListSvc.dll
17:33:17.0007 5164 HomeGroupListener - ok
17:33:17.0054 5164 [ DBC02D918FFF1CAD628ACBE0C0EAA8E8 ] HomeGroupProvider E:\Windows\system32\provsvc.dll
17:33:17.0117 5164 HomeGroupProvider - ok
17:33:17.0210 5164 [ 295FDC419039090EB8B49FFDBB374549 ] HpSAMD E:\Windows\system32\drivers\HpSAMD.sys
17:33:17.0226 5164 HpSAMD - ok
17:33:17.0273 5164 [ 871917B07A141BFF43D76D8844D48106 ] HTTP E:\Windows\system32\drivers\HTTP.sys
17:33:17.0335 5164 HTTP - ok
17:33:17.0366 5164 [ 0C4E035C7F105F1299258C90886C64C5 ] hwpolicy E:\Windows\system32\drivers\hwpolicy.sys
17:33:17.0382 5164 hwpolicy - ok
17:33:17.0460 5164 [ F151F0BDC47F4A28B1B20A0818EA36D6 ] i8042prt E:\Windows\system32\DRIVERS\i8042prt.sys
17:33:17.0491 5164 i8042prt - ok
17:33:17.0553 5164 [ A3CAE5D281DB4CFF7CFF8233507EE5AD ] iaStorV E:\Windows\system32\drivers\iaStorV.sys
17:33:17.0585 5164 iaStorV - ok
17:33:17.0678 5164 [ C521D7EB6497BB1AF6AFA89E322FB43C ] idsvc E:\Windows\Microsoft.NET\Framework\v3.0\Windows Communication Foundation\infocard.exe
17:33:17.0741 5164 idsvc - ok
17:33:18.0131 5164 [ AD626F6964F4D364D226C39E06872DD3 ] igfx E:\Windows\system32\DRIVERS\igdkmd32.sys
17:33:18.0287 5164 igfx - ok
17:33:18.0365 5164 [ 4173FF5708F3236CF25195FECD742915 ] iirsp E:\Windows\system32\drivers\iirsp.sys
17:33:18.0380 5164 iirsp - ok
17:33:18.0427 5164 [ F95622F161474511B8D80D6B093AA610 ] IKEEXT E:\Windows\System32\ikeext.dll
17:33:18.0521 5164 IKEEXT - ok
17:33:18.0661 5164 [ 4A0F260DF9A5333C07F4AB40CA9D4F4B ] IntcAzAudAddService E:\Windows\system32\drivers\RTKVHDA.sys
17:33:18.0755 5164 IntcAzAudAddService - ok
17:33:18.0786 5164 [ A0F12F2C9BA6C72F3987CE780E77C130 ] intelide E:\Windows\system32\drivers\intelide.sys
17:33:18.0801 5164 intelide - ok
17:33:18.0942 5164 [ 3B514D27BFC4ACCB4037BC6685F766E0 ] intelppm E:\Windows\system32\DRIVERS\intelppm.sys
17:33:18.0957 5164 intelppm - ok
17:33:19.0129 5164 [ 3DC635B66DD7412E1C9C3A77B8D78F25 ] IntuitUpdateService E:\Program Files\Common Files\Intuit\Update Service\IntuitUpdateService.exe
17:33:19.0129 5164 IntuitUpdateService - ok
17:33:19.0176 5164 [ ACB364B9075A45C0736E5C47BE5CAE19 ] IPBusEnum E:\Windows\system32\ipbusenum.dll
17:33:19.0223 5164 IPBusEnum - ok
17:33:19.0238 5164 [ 709D1761D3B19A932FF0238EA6D50200 ] IpFilterDriver E:\Windows\system32\DRIVERS\ipfltdrv.sys
17:33:19.0301 5164 IpFilterDriver - ok
17:33:19.0379 5164 [ 4D65A07B795D6674312F879D09AA7663 ] iphlpsvc E:\Windows\System32\iphlpsvc.dll
17:33:19.0441 5164 iphlpsvc - ok
17:33:19.0472 5164 [ 4BD7134618C1D2A27466A099062547BF ] IPMIDRV E:\Windows\system32\drivers\IPMIDrv.sys
17:33:19.0503 5164 IPMIDRV - ok
17:33:19.0519 5164 [ A5FA468D67ABCDAA36264E463A7BB0CD ] IPNAT E:\Windows\system32\drivers\ipnat.sys
17:33:19.0581 5164 IPNAT - ok
17:33:19.0659 5164 [ CE004777B92DEA56FE14EC900D20BAA4 ] iPod Service E:\Program Files\iPod\bin\iPodService.exe
17:33:19.0706 5164 iPod Service - ok
17:33:19.0769 5164 [ 42996CFF20A3084A56017B7902307E9F ] IRENUM E:\Windows\system32\drivers\irenum.sys
17:33:19.0815 5164 IRENUM - ok
17:33:19.0847 5164 [ 1F32BB6B38F62F7DF1A7AB7292638A35 ] isapnp E:\Windows\system32\drivers\isapnp.sys
17:33:19.0878 5164 isapnp - ok
17:33:19.0893 5164 [ CB7A9ABB12B8415BCE5D74994C7BA3AE ] iScsiPrt E:\Windows\system32\drivers\msiscsi.sys
17:33:19.0925 5164 iScsiPrt - ok
17:33:20.0049 5164 [ CF9BA304B8047B9582D72D9BFEF42EAE ] jswpsapi E:\Program Files\NETGEAR\WNA1100\jswpsapi.exe
17:33:20.0112 5164 jswpsapi - ok
17:33:20.0190 5164 [ 55C9B4252B751226B838EED2BC50BB64 ] jswpslwf E:\Windows\system32\DRIVERS\jswpslwf.sys
17:33:20.0237 5164 jswpslwf - ok
17:33:20.0315 5164 [ ADEF52CA1AEAE82B50DF86B56413107E ] kbdclass E:\Windows\system32\DRIVERS\kbdclass.sys
17:33:20.0330 5164 kbdclass - ok
17:33:20.0393 5164 [ 9E3CED91863E6EE98C24794D05E27A71 ] kbdhid E:\Windows\system32\drivers\kbdhid.sys
17:33:20.0455 5164 kbdhid - ok
17:33:20.0471 5164 [ F42309C4191C506B71DB5D1126D26318 ] KeyIso E:\Windows\system32\lsass.exe
17:33:20.0502 5164 KeyIso - ok
17:33:20.0533 5164 [ 412CEA1AA78CC02A447F5C9E62B32FF1 ] KSecDD E:\Windows\system32\Drivers\ksecdd.sys
17:33:20.0549 5164 KSecDD - ok
17:33:20.0580 5164 [ 26C046977E85B95036453D7B88BA1820 ] KSecPkg E:\Windows\system32\Drivers\ksecpkg.sys
17:33:20.0595 5164 KSecPkg - ok
17:33:20.0642 5164 [ 89A7B9CC98D0D80C6F31B91C0A310FCD ] KtmRm E:\Windows\system32\msdtckrm.dll
17:33:20.0720 5164 KtmRm - ok
17:33:20.0798 5164 [ D64AF876D53ECA3668BB97B51B4E70AB ] LanmanServer E:\Windows\System32\srvsvc.dll
17:33:20.0876 5164 LanmanServer - ok
17:33:20.0923 5164 [ 58405E4F68BA8E4057C6E914F326ABA2 ] LanmanWorkstation E:\Windows\System32\wkssvc.dll
17:33:20.0985 5164 LanmanWorkstation - ok
17:33:21.0063 5164 [ F7611EC07349979DA9B0AE1F18CCC7A6 ] lltdio E:\Windows\system32\DRIVERS\lltdio.sys
17:33:21.0141 5164 lltdio - ok
17:33:21.0188 5164 [ 5700673E13A2117FA3B9020C852C01E2 ] lltdsvc E:\Windows\System32\lltdsvc.dll
17:33:21.0251 5164 lltdsvc - ok
17:33:21.0282 5164 [ 55CA01BA19D0006C8F2639B6C045E08B ] lmhosts E:\Windows\System32\lmhsvc.dll
17:33:21.0344 5164 lmhosts - ok
17:33:21.0422 5164 [ EB119A53CCF2ACC000AC71B065B78FEF ] LSI_FC E:\Windows\system32\drivers\lsi_fc.sys
17:33:21.0453 5164 LSI_FC - ok
17:33:21.0485 5164 [ 8ADE1C877256A22E49B75D1CC9161F9C ] LSI_SAS E:\Windows\system32\drivers\lsi_sas.sys
17:33:21.0500 5164 LSI_SAS - ok
17:33:21.0531 5164 [ DC9DC3D3DAA0E276FD2EC262E38B11E9 ] LSI_SAS2 E:\Windows\system32\drivers\lsi_sas2.sys
17:33:21.0547 5164 LSI_SAS2 - ok
17:33:21.0578 5164 [ 0A036C7D7CAB643A7F07135AC47E0524 ] LSI_SCSI E:\Windows\system32\drivers\lsi_scsi.sys
17:33:21.0609 5164 LSI_SCSI - ok
17:33:21.0673 5164 [ 6703E366CC18D3B6E534F5CF7DF39CEE ] luafv E:\Windows\system32\drivers\luafv.sys
17:33:21.0766 5164 luafv - ok
17:33:21.0829 5164 [ 65E794E86468B61F2BC79ABC48BC4433 ] MBAMProtector E:\Windows\system32\drivers\mbam.sys
17:33:21.0844 5164 MBAMProtector - ok
17:33:21.0954 5164 [ 0DCF16B1449811EFA47AB52CAC84093C ] MBAMScheduler E:\Program Files\Malwarebytes' Anti-Malware\mbamscheduler.exe
17:33:21.0969 5164 MBAMScheduler - ok
17:33:22.0047 5164 [ 9EAABA4D601004BEA4DAA6E146E19A96 ] MBAMService E:\Program Files\Malwarebytes' Anti-Malware\mbamservice.exe
17:33:22.0094 5164 MBAMService - ok
17:33:22.0219 5164 [ 0DB7527DB188C7D967A37BB51BBF3963 ] MBAMSwissArmy E:\Windows\system32\drivers\mbamswissarmy.sys
17:33:22.0266 5164 MBAMSwissArmy - ok
17:33:22.0375 5164 [ 64753FE65431B92D6FB64CC338757E32 ] MBX2DFU E:\Windows\system32\DRIVERS\MBX2DFU.sys
17:33:22.0390 5164 MBX2DFU - ok
17:33:22.0453 5164 [ 0F110335DDBE99A683E6646812D23C43 ] MBX2MIDK E:\Windows\system32\drivers\mbx2midk.sys
17:33:22.0468 5164 MBX2MIDK - ok
17:33:22.0500 5164 [ BFB9EE8EE977EFE85D1A3105ABEF6DD1 ] Mcx2Svc E:\Windows\system32\Mcx2Svc.dll
17:33:22.0578 5164 Mcx2Svc - ok
17:33:22.0688 5164 [ 0FFF5B045293002AB38EB1FD1FC2FB74 ] megasas E:\Windows\system32\drivers\megasas.sys
17:33:22.0707 5164 megasas - ok
17:33:22.0896 5164 [ DCBAB2920C75F390CAF1D29F675D03D6 ] MegaSR E:\Windows\system32\drivers\MegaSR.sys
17:33:22.0922 5164 MegaSR - ok
17:33:23.0162 5164 [ FAFE367D032ED82E9332B4C741A20216 ] Microsoft Office Groove Audit Service E:\Program Files\Microsoft Office\Office12\GrooveAuditService.exe
17:33:23.0179 5164 Microsoft Office Groove Audit Service - ok
17:33:23.0228 5164 [ 146B6F43A673379A3C670E86D89BE5EA ] MMCSS E:\Windows\system32\mmcss.dll
17:33:23.0323 5164 MMCSS - ok
17:33:23.0353 5164 [ F001861E5700EE84E2D4E52C712F4964 ] Modem E:\Windows\system32\drivers\modem.sys
17:33:23.0423 5164 Modem - ok
17:33:23.0499 5164 [ 79D10964DE86B292320E9DFE02282A23 ] monitor E:\Windows\system32\DRIVERS\monitor.sys
17:33:23.0551 5164 monitor - ok
17:33:23.0621 5164 [ FB18CC1D4C2E716B6B903B0AC0CC0609 ] mouclass E:\Windows\system32\DRIVERS\mouclass.sys
17:33:23.0652 5164 mouclass - ok
17:33:23.0679 5164 [ 2C388D2CD01C9042596CF3C8F3C7B24D ] mouhid E:\Windows\system32\DRIVERS\mouhid.sys
17:33:23.0726 5164 mouhid - ok
17:33:23.0764 5164 [ FC8771F45ECCCFD89684E38842539B9B ] mountmgr E:\Windows\system32\drivers\mountmgr.sys
17:33:23.0795 5164 mountmgr - ok
17:33:24.0147 5164 [ 8EE7B1A0AFF41151210A8ACE8E162E33 ] MozillaMaintenance E:\Program Files\Mozilla Maintenance Service\maintenanceservice.exe
17:33:24.0174 5164 Suspicious file (Forged): E:\Program Files\Mozilla Maintenance Service\maintenanceservice.exe. Real md5: 8EE7B1A0AFF41151210A8ACE8E162E33, Fake md5: BF161D1D4EB8A069C9B2DEF882C0E55C
17:33:24.0175 5164 MozillaMaintenance ( ForgedFile.Multi.Generic ) - warning
17:33:24.0175 5164 MozillaMaintenance - detected ForgedFile.Multi.Generic (1)
17:33:24.0239 5164 [ 2D699FB6E89CE0D8DA14ECC03B3EDFE0 ] mpio E:\Windows\system32\drivers\mpio.sys
17:33:24.0267 5164 mpio - ok
17:33:24.0297 5164 [ AD2723A7B53DD1AACAE6AD8C0BFBF4D0 ] mpsdrv E:\Windows\system32\drivers\mpsdrv.sys
17:33:24.0372 5164 mpsdrv - ok
17:33:24.0403 5164 [ CEB46AB7C01C9F825F8CC6BABC18166A ] MRxDAV E:\Windows\system32\drivers\mrxdav.sys
17:33:24.0474 5164 MRxDAV - ok
17:33:24.0525 5164 [ B272B4C3E085EA860C12F2E4FAF2FFA2 ] mrxsmb E:\Windows\system32\DRIVERS\mrxsmb.sys
17:33:24.0604 5164 mrxsmb - ok
17:33:24.0638 5164 [ 9AC33EF26C8A3AD0F117D00EB7301D03 ] mrxsmb10 E:\Windows\system32\DRIVERS\mrxsmb10.sys
17:33:24.0721 5164 mrxsmb10 - ok
17:33:24.0750 5164 [ E0ABDB5ED7E199E242A7D028E76C1D3A ] mrxsmb20 E:\Windows\system32\DRIVERS\mrxsmb20.sys
17:33:24.0862 5164 mrxsmb20 - ok
17:33:24.0906 5164 [ 012C5F4E9349E711E11E0F19A8589F0A ] msahci E:\Windows\system32\drivers\msahci.sys
17:33:24.0933 5164 msahci - ok
17:33:24.0951 5164 [ 55055F8AD8BE27A64C831322A780A228 ] msdsm E:\Windows\system32\drivers\msdsm.sys
17:33:25.0016 5164 msdsm - ok
17:33:25.0051 5164 [ E1BCE74A3BD9902B72599C0192A07E27 ] MSDTC E:\Windows\System32\msdtc.exe
17:33:25.0098 5164 MSDTC - ok
17:33:25.0191 5164 [ DAEFB28E3AF5A76ABCC2C3078C07327F ] Msfs E:\Windows\system32\drivers\Msfs.sys
17:33:25.0222 5164 Msfs - ok
17:33:25.0285 5164 [ 3E1E5767043C5AF9367F0056295E9F84 ] mshidkmdf E:\Windows\System32\drivers\mshidkmdf.sys
17:33:25.0378 5164 mshidkmdf - ok
17:33:25.0425 5164 [ 0A4E5757AE09FA9622E3158CC1AEF114 ] msisadrv E:\Windows\system32\drivers\msisadrv.sys
17:33:25.0441 5164 msisadrv - ok
17:33:25.0472 5164 [ 90F7D9E6B6F27E1A707D4A297F077828 ] MSiSCSI E:\Windows\system32\iscsiexe.dll
17:33:25.0534 5164 MSiSCSI - ok
17:33:25.0550 5164 msiserver - ok
17:33:25.0612 5164 [ 8C0860D6366AAFFB6C5BB9DF9448E631 ] MSKSSRV E:\Windows\system32\drivers\MSKSSRV.sys
17:33:25.0675 5164 MSKSSRV - ok
17:33:25.0753 5164 [ 3EA8B949F963562CEDBB549EAC0C11CE ] MSPCLOCK E:\Windows\system32\drivers\MSPCLOCK.sys
17:33:25.0862 5164 MSPCLOCK - ok
17:33:25.0878 5164 [ F456E973590D663B1073E9C463B40932 ] MSPQM E:\Windows\system32\drivers\MSPQM.sys
17:33:25.0956 5164 MSPQM - ok
17:33:26.0002 5164 [ 0E008FC4819D238C51D7C93E7B41E560 ] MsRPC E:\Windows\system32\drivers\MsRPC.sys
17:33:26.0018 5164 MsRPC - ok
17:33:26.0049 5164 [ FC6B9FF600CC585EA38B12589BD4E246 ] mssmbios E:\Windows\system32\DRIVERS\mssmbios.sys
17:33:26.0065 5164 mssmbios - ok
17:33:26.0096 5164 [ B42C6B921F61A6E55159B8BE6CD54A36 ] MSTEE E:\Windows\system32\drivers\MSTEE.sys
17:33:26.0190 5164 MSTEE - ok
17:33:26.0205 5164 [ 33599130F44E1F34631CEA241DE8AC84 ] MTConfig E:\Windows\system32\drivers\MTConfig.sys
17:33:26.0252 5164 MTConfig - ok
17:33:26.0283 5164 [ 159FAD02F64E6381758C990F753BCC80 ] Mup E:\Windows\system32\Drivers\mup.sys
17:33:26.0314 5164 Mup - ok
17:33:26.0346 5164 [ 61D57A5D7C6D9AFE10E77DAE6E1B445E ] napagent E:\Windows\system32\qagentRT.dll
17:33:26.0424 5164 napagent - ok
17:33:26.0502 5164 [ 26384429FCD85D83746F63E798AB1480 ] NativeWifiP E:\Windows\system32\DRIVERS\nwifi.sys
17:33:26.0533 5164 NativeWifiP - ok
17:33:26.0673 5164 [ 9D1CCE440552500DED3A62F9D779CDB4 ] NAUpdate E:\Program Files\Nero\Update\NASvc.exe
17:33:26.0704 5164 NAUpdate - ok
17:33:26.0782 5164 [ E7C54812A2AAF43316EB6930C1FFA108 ] NDIS E:\Windows\system32\drivers\ndis.sys
17:33:26.0845 5164 NDIS - ok
17:33:26.0907 5164 [ 0E1787AA6C9191D3D319E8BAFE86F80C ] NdisCap E:\Windows\system32\DRIVERS\ndiscap.sys
17:33:26.0985 5164 NdisCap - ok
17:33:27.0048 5164 [ E4A8AEC125A2E43A9E32AFEEA7C9C888 ] NdisTapi E:\Windows\system32\DRIVERS\ndistapi.sys
17:33:27.0110 5164 NdisTapi - ok
17:33:27.0157 5164 [ D8A65DAFB3EB41CBB622745676FCD072 ] Ndisuio E:\Windows\system32\DRIVERS\ndisuio.sys
17:33:27.0219 5164 Ndisuio - ok
17:33:27.0266 5164 [ 38FBE267E7E6983311179230FACB1017 ] NdisWan E:\Windows\system32\DRIVERS\ndiswan.sys
17:33:27.0313 5164 NdisWan - ok
17:33:27.0344 5164 [ A4BDC541E69674FBFF1A8FF00BE913F2 ] NDProxy E:\Windows\system32\drivers\NDProxy.sys
17:33:27.0391 5164 NDProxy - ok
17:33:27.0453 5164 [ 80B275B1CE3B0E79909DB7B39AF74D51 ] NetBIOS E:\Windows\system32\DRIVERS\netbios.sys
17:33:27.0547 5164 NetBIOS - ok
17:33:27.0578 5164 [ 280122DDCF04B378EDD1AD54D71C1E54 ] NetBT E:\Windows\system32\DRIVERS\netbt.sys
17:33:27.0656 5164 NetBT - ok
17:33:27.0703 5164 [ F42309C4191C506B71DB5D1126D26318 ] Netlogon E:\Windows\system32\lsass.exe
17:33:27.0734 5164 Netlogon - ok
17:33:27.0828 5164 [ 7CCCFCA7510684768DA22092D1FA4DB2 ] Netman E:\Windows\System32\netman.dll
17:33:27.0890 5164 Netman - ok
17:33:27.0906 5164 [ 8C338238C16777A802D6A9211EB2BA50 ] netprofm E:\Windows\System32\netprofm.dll
17:33:27.0984 5164 netprofm - ok
17:33:28.0030 5164 [ F476EC40033CDB91EFBE73EB99B8362D ] NetTcpPortSharing E:\Windows\Microsoft.NET\Framework\v3.0\Windows Communication Foundation\SMSvcHost.exe
17:33:28.0046 5164 NetTcpPortSharing - ok
17:33:28.0327 5164 [ FEB745E4669476C8D368F6C1CA7C7442 ] netw5v32 E:\Windows\system32\DRIVERS\netw5v32.sys
17:33:28.0670 5164 netw5v32 - ok
17:33:28.0748 5164 [ 1D85C4B390B0EE09C7A46B91EFB2C097 ] nfrd960 E:\Windows\system32\drivers\nfrd960.sys
17:33:28.0764 5164 nfrd960 - ok
17:33:28.0810 5164 [ 912084381D30D8B89EC4E293053F4710 ] NlaSvc E:\Windows\System32\nlasvc.dll
17:33:28.0888 5164 NlaSvc - ok
17:33:28.0935 5164 [ 1DB262A9F8C087E8153D89BEF3D2235F ] Npfs E:\Windows\system32\drivers\Npfs.sys
17:33:28.0982 5164 Npfs - ok
17:33:28.0998 5164 [ BA387E955E890C8A88306D9B8D06BF17 ] nsi E:\Windows\system32\nsisvc.dll
17:33:29.0060 5164 nsi - ok
17:33:29.0091 5164 [ E9A0A4D07E53D8FEA2BB8387A3293C58 ] nsiproxy E:\Windows\system32\drivers\nsiproxy.sys
17:33:29.0169 5164 nsiproxy - ok
17:33:29.0434 5164 [ 42CE5E77721E60F39858FF2A35450342 ] NSUService E:\Program Files\Sony\Network Utility\NSUService.exe
17:33:29.0512 5164 NSUService ( UnsignedFile.Multi.Generic ) - warning
17:33:29.0512 5164 NSUService - detected UnsignedFile.Multi.Generic (1)
17:33:29.0762 5164 [ 33C3093D09017CFE2E219F2472BFF6EB ] Ntfs E:\Windows\system32\drivers\Ntfs.sys
17:33:29.0840 5164 Ntfs - ok
17:33:29.0887 5164 [ F9756A98D69098DCA8945D62858A812C ] Null E:\Windows\system32\drivers\Null.sys
17:33:29.0965 5164 Null - ok
17:33:30.0012 5164 [ AF2EEC9580C1D32FB7EAF105D9784061 ] nvraid E:\Windows\system32\drivers\nvraid.sys
17:33:30.0043 5164 nvraid - ok
17:33:30.0058 5164 [ 9283C58EBAA2618F93482EB5DABCEC82 ] nvstor E:\Windows\system32\drivers\nvstor.sys
17:33:30.0090 5164 nvstor - ok
17:33:30.0105 5164 [ 5A0983915F02BAE73267CC2A041F717D ] nv_agp E:\Windows\system32\drivers\nv_agp.sys
17:33:30.0136 5164 nv_agp - ok
17:33:30.0292 5164 [ 84DE1DD996B48B05ACE31AD015FA108A ] odserv E:\Program Files\Common Files\Microsoft Shared\OFFICE12\ODSERV.EXE
17:33:30.0324 5164 odserv - ok
17:33:30.0355 5164 [ 08A70A1F2CDDE9BB49B885CB817A66EB ] ohci1394 E:\Windows\system32\drivers\ohci1394.sys
17:33:30.0402 5164 ohci1394 - ok
17:33:30.0464 5164 [ 5A432A042DAE460ABE7199B758E8606C ] ose E:\Program Files\Common Files\Microsoft Shared\Source Engine\OSE.EXE
17:33:30.0495 5164 ose - ok
17:33:30.0526 5164 [ 82A8521DDC60710C3D3D3E7325209BEC ] p2pimsvc E:\Windows\system32\pnrpsvc.dll
17:33:30.0589 5164 p2pimsvc - ok
17:33:30.0636 5164 [ 59C3DDD501E39E006DAC31BF55150D91 ] p2psvc E:\Windows\system32\p2psvc.dll
17:33:30.0667 5164 p2psvc - ok
17:33:30.0682 5164 [ 2EA877ED5DD9713C5AC74E8EA7348D14 ] Parport E:\Windows\system32\drivers\parport.sys
17:33:30.0714 5164 Parport - ok
17:33:30.0729 5164 [ BF8F6AF06DA75B336F07E23AEF97D93B ] partmgr E:\Windows\system32\drivers\partmgr.sys
17:33:30.0760 5164 partmgr - ok
17:33:30.0776 5164 [ EB0A59F29C19B86479D36B35983DAADC ] Parvdm E:\Windows\system32\drivers\parvdm.sys
17:33:30.0823 5164 Parvdm - ok
17:33:30.0854 5164 [ 358AB7956D3160000726574083DFC8A6 ] PcaSvc E:\Windows\System32\pcasvc.dll
17:33:30.0885 5164 PcaSvc - ok
17:33:30.0901 5164 [ 673E55C3498EB970088E812EA820AA8F ] pci E:\Windows\system32\drivers\pci.sys
17:33:30.0932 5164 pci - ok
17:33:30.0948 5164 [ AFE86F419014DB4E5593F69FFE26CE0A ] pciide E:\Windows\system32\drivers\pciide.sys
17:33:30.0963 5164 pciide - ok
17:33:30.0994 5164 [ F396431B31693E71E8A80687EF523506 ] pcmcia E:\Windows\system32\DRIVERS\pcmcia.sys
17:33:31.0026 5164 pcmcia - ok
17:33:31.0166 5164 [ A0E7D752514A7D99341D5F2A834224A9 ] PCToolsSSDMonitorSvc E:\Program Files\Common Files\PC Tools\sMonitor\StartManSvc.exe
17:33:31.0197 5164 PCToolsSSDMonitorSvc - ok
17:33:31.0228 5164 [ 250F6B43D2B613172035C6747AEEB19F ] pcw E:\Windows\system32\drivers\pcw.sys
17:33:31.0244 5164 pcw - ok
17:33:31.0322 5164 [ 9E0104BA49F4E6973749A02BF41344ED ] PEAUTH E:\Windows\system32\drivers\peauth.sys
17:33:31.0416 5164 PEAUTH - ok
17:33:31.0478 5164 [ AF4D64D2A57B9772CF3801950B8058A6 ] PeerDistSvc E:\Windows\system32\peerdistsvc.dll
17:33:31.0587 5164 PeerDistSvc - ok
17:33:31.0587 5164 Scan interrupted by user!
17:33:31.0587 5164 ================ Scan global ===============================
17:33:31.0587 5164 Scan interrupted by user!
17:33:31.0587 5164 ================ Scan MBR ==================================
17:33:31.0587 5164 Scan interrupted by user!
17:33:31.0587 5164 ================ Scan VBR ==================================
17:33:31.0587 5164 Scan interrupted by user!
17:33:31.0587 5164 ============================================================
17:33:31.0587 5164 Scan finished
17:33:31.0587 5164 ============================================================
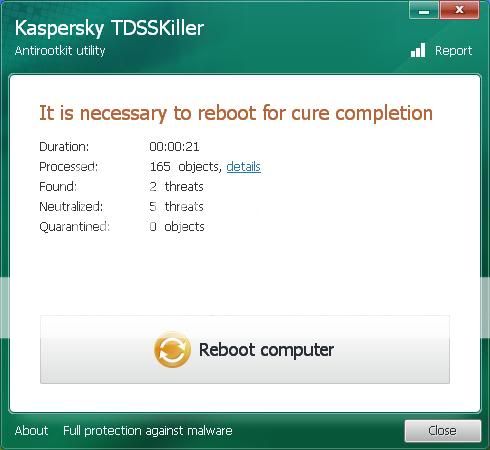
17:33:31.0618 4436 Detected object count: 3
17:33:31.0618 4436 Actual detected object count: 3
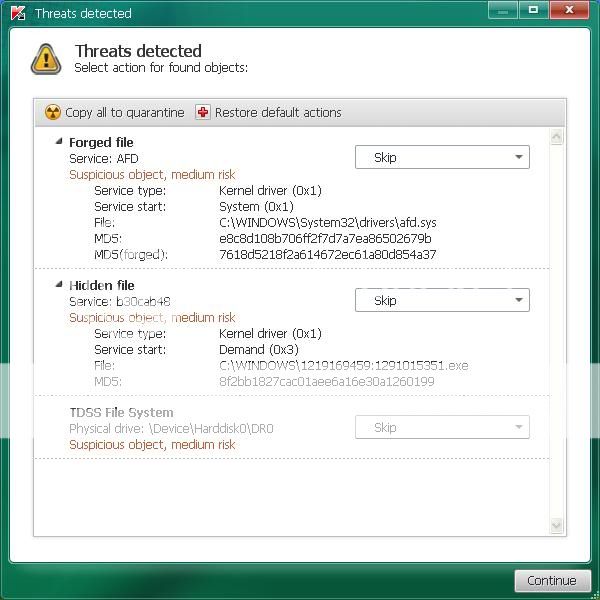
17:33:33.0553 4436 digiSPTIService ( UnsignedFile.Multi.Generic ) - skipped by user
17:33:33.0553 4436 digiSPTIService ( UnsignedFile.Multi.Generic ) - User select action: Skip
17:33:33.0568 4436 MozillaMaintenance ( ForgedFile.Multi.Generic ) - skipped by user
17:33:33.0568 4436 MozillaMaintenance ( ForgedFile.Multi.Generic ) - User select action: Skip
17:33:33.0568 4436 NSUService ( UnsignedFile.Multi.Generic ) - skipped by user
17:33:33.0568 4436 NSUService ( UnsignedFile.Multi.Generic ) - User select action: Skip
17:33:35.0487 5836 Deinitialize success