Cyber attacks can cause headaches for businesses and loss of revenue. For one petrochemical operation in Saudi Arabia, a simple breach would have been preferred compared to what has been discovered. Malware found in the facility back in August was designed to damage equipment and potentially result in an explosion that would destroy the entire plant.
According to investigators looking into the matter, the only reason why the attack failed was due to a flaw in the offending code that caused a system shutdown. Had the malware been written correctly, there would be one less petroleum facility in existence. It is believed that political motives may be the reasoning for such an attack. Due to the complexity of the code, support from a government is somewhat likely.
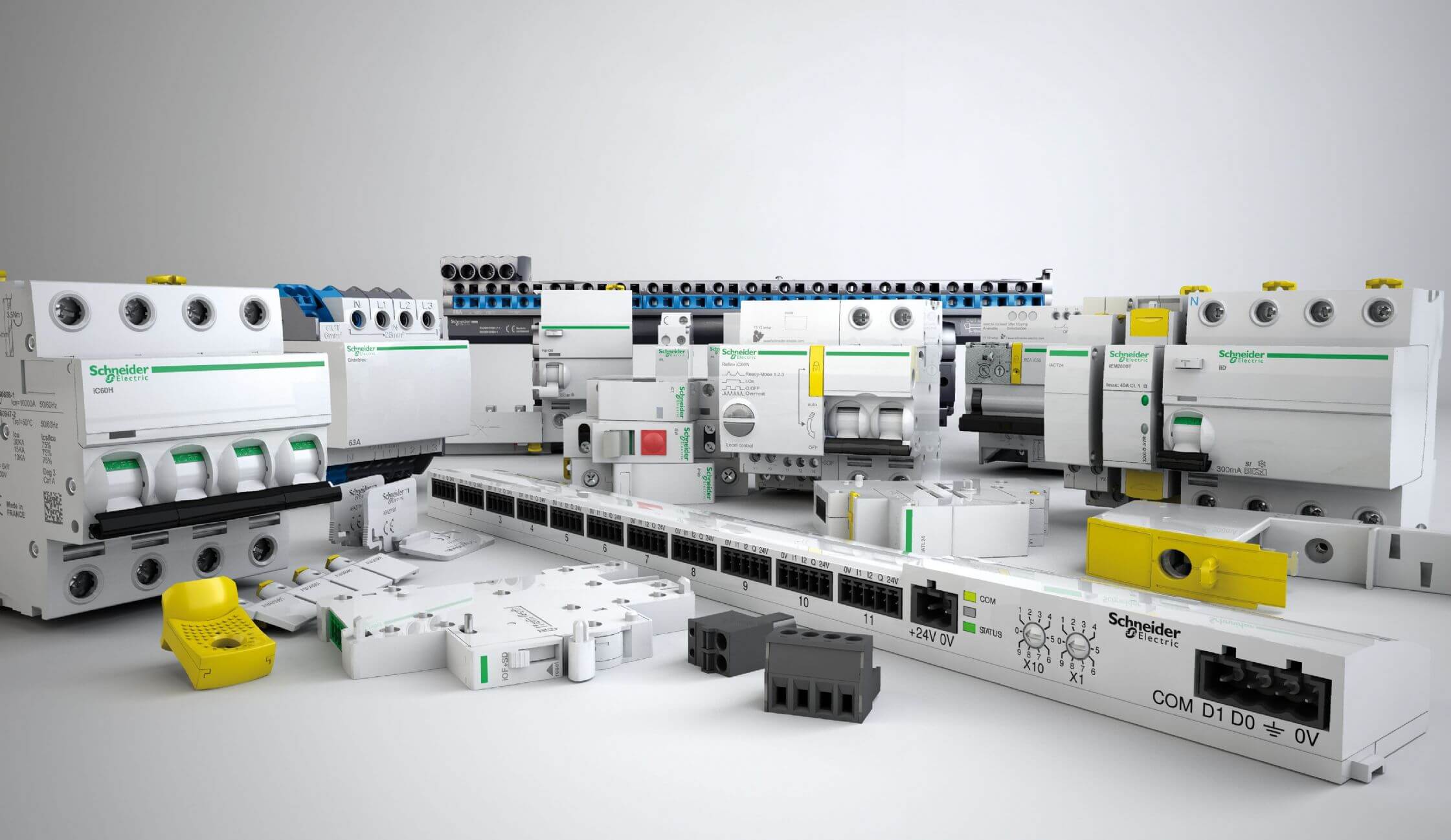
There is fear that the same attack could be launched against other chemical processing facilities since the same industrial controllers are used across the industry. Schneider Electric has sold more than 13,000 systems that make use of Triconex safety controller susceptible to attack.
Software analysis has shown that the code used has not been discovered on any other systems to date. In order to design the malware used, it is almost essential that the developers had access to the Triconex safety system components ahead of time for testing. Investigators have stated that the parts required cost about $40,000 on eBay.
Some experts familiar with the Saudi Arabian oil and chemical industry believe that the attack may have been a way to put Crown Prince Mohammed bin Salman's plans to diversify the local economy on hold.
United States government entities and private security firm Mandiant are all still working on the incident. The NSA, FBI, Department of Homeland Security, and also the Defense Advanced Research Projects Agency (DARPA) are all working to gather as much information as possible.
Although little information on how the attack actually works has been shared, it is believed that the malicious code can be injected remotely making the threat of another attack high.
Based on past history of attacks against Saudi Arabia and looking at the sophistication of the cyber attack leaves few likely perpetrators. The United States, Israel, Russia, China, and Iran are considered to have some of the best cyber capabilities related to industrial equipment. Out of those, only Iran has incentive to harm Saudi businesses.
Still, there is no evidence that has been shared that would be able to directly relate the attack back to a single entity. As researchers continue to gather information on the incident, it is not likely for further information to be made available.
