WTF?! A application in the Mac App Store has been found to exfiltrate a user's browsing history to a Chinese server without the user's permission. This undermines the entire premise of the App Store as a safer way to install applications as well as Apple's stance on privacy and security.
The most popular utility app in the Mac App Store, Adware Doctor, has been discovered to capture a user's browsing history and ex-filtrate it to a Chinese server.
The behavior was first discovered by twitter user @privacyis1st who then contacted Patrick Wardle, a former hacker at NSA and current chief research officer at startup Digita Security. Wardle subsequently did a comprehensive deep dive on the rogue app to discover exactly how it works and posted his findings on his blog.
Top Sold MacOS AppStore application is ROGUE. Adware Doctor is stealing your privacy. PoC: https://t.co/LmveX593q0#malware #virus #MacOS #Apple #MacBook #MacBookPro #CyberSecurity #privacy #GDPR #Hacking #hackers #cyberpunk #Alert
--- Privacy 1st (@privacyis1st) August 20, 2018
According Wardle, the app first asks for universal access in order to run. That might sound creepy by itself but most malware/virus scanners need access in order to scan your system. However, Adware Doctor was able to access running processes (normally protected by sandboxing) by using Apple's own code:
"It's (likely) just a copy and paste of Apple's GetBSDProcessList code (found in Technical Q&A QA1123 "Getting List of All Processes on Mac OS X"). Apparently this is how one can get a process listing from within the application sandbox! I'm guessing this method is unsanctioned (as it clearly goes against the design goals of sandbox isolation). And yes, rather amusing the code Adware Doctor uses to skirt the sandbox, is directly from Apple!"
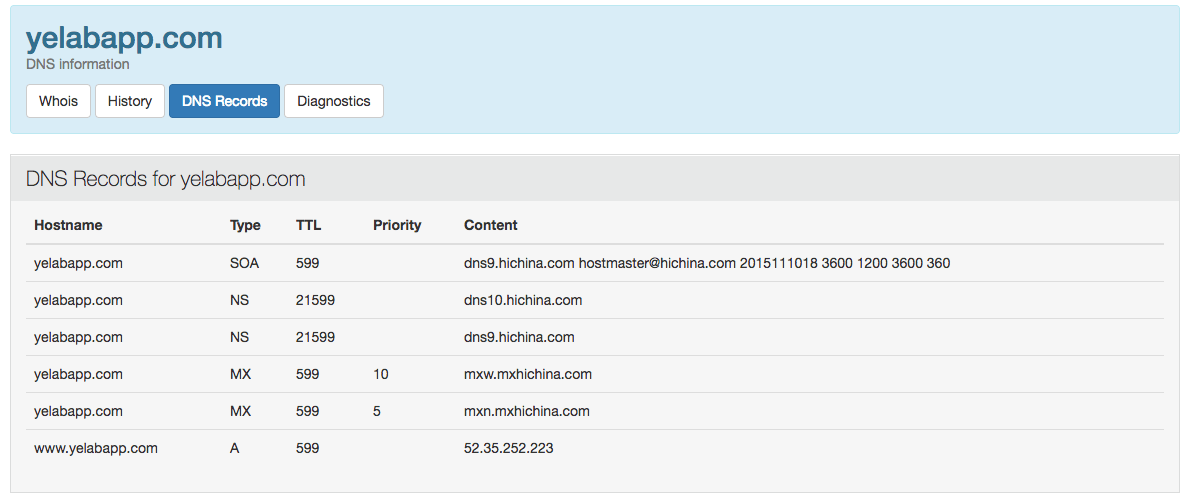
The app creates a file called 'history.zip' and uploads that file to a server based in China. Unpacking the zip file reveals the browsing history of all the browsers you have installed including Safari. Additionally, the app also captures data from all the apps you've downloaded.
Despite being a "popular" app, Adware Doctor has quite the checkered past. For example, it has blatantly violated App Store rules by attempting to elevate privileges in 2016 by using AppleScript. It was also caught using the name "Adware Medic" which was already being used by an existing app at the time. Apple pulled it from the Mac App Store only to reinstate it once the name was changed to the current Adware Doctor. Also, Wardle points out that many of the good reviews are likely fake in an effort to attract more users.
What's most alarming is that despite being notified about this a month ago, Apple has still refused to take action on an application that clearly violates privacy. Apple openly promotes both the Mac and iOS App Stores as the safest way to install applications specifically to avoid rogue applications like Adware Doctor. Presumably, every app is reviewed before it's allowed in the store and when there are issues, Apple is usually quick to remove it.
While the app itself is still available, the server itself is down (probably due to this revelation). On a positive note, Wardle's in-depth reverse engineering of the app is quite the lesson in cyber-security.
