In brief: Kaspersky Lab data indicates that attackers are using less sophisticated methods like UDP flooding to test the waters, presumably reserving coordinated and complex attacks such as HTTP floods for vulnerable targets.
Kaspersky Lab in its latest DDoS Intelligence report recorded 13 percent less DDoS activity in 2018 compared to the previous year.
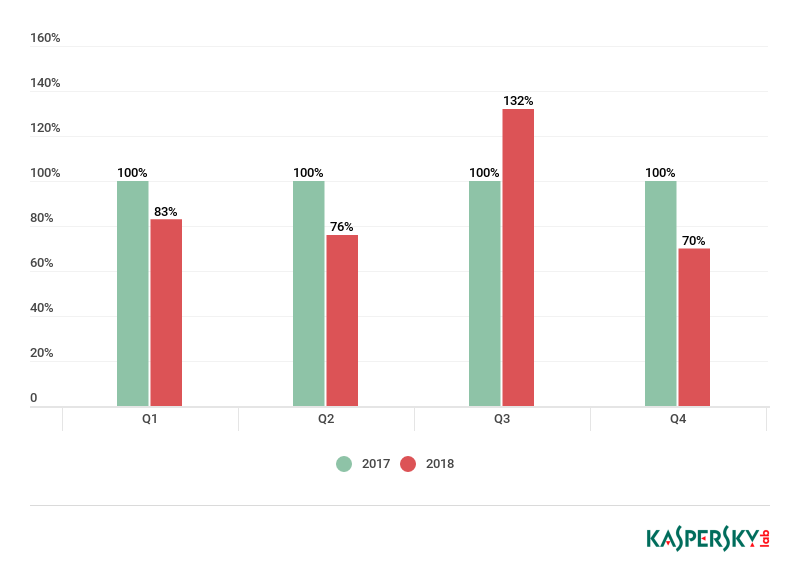
The number of attacks was down in each quarter of 2018 compared to 2017 save for the third quarter due to an unusually active September. Q4 was the least active quarter as attacks were down 30 percent year-over-year.
While the sheer number of attacks may have dropped, the duration of attacks is on the rise. According to Kaspersky Lab, the average length of an attack climbed from 95 minutes in the first quarter to 218 minutes in the fourth quarter.
The cybersecurity firm points out that UDP flooding is the most common type of attack by a wide margin although when comparing attacks by their duration, you get an entirely different picture. HTTP floods and mixed attacks with an HTTP element account for roughly 80 percent of all DDoS attack activity. Why the discrepancy, you ask?
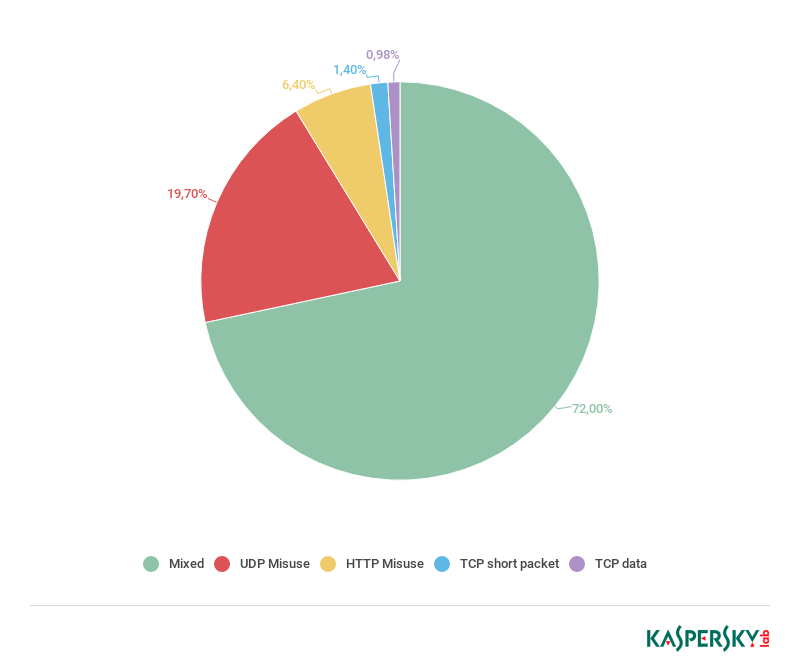
Standard DDoS attacks have been rendered virtually useless thanks to improved attack defenses. It is believed that attackers use UDP flooding largely to test the waters, hoping to find a target that isn't secure. It only takes a few minutes to determine if a target has the proper safeguards in place to thwart an attack of this nature, Kaspersky said.
Lead image courtesy FrameStockFootages via Shutterstock
