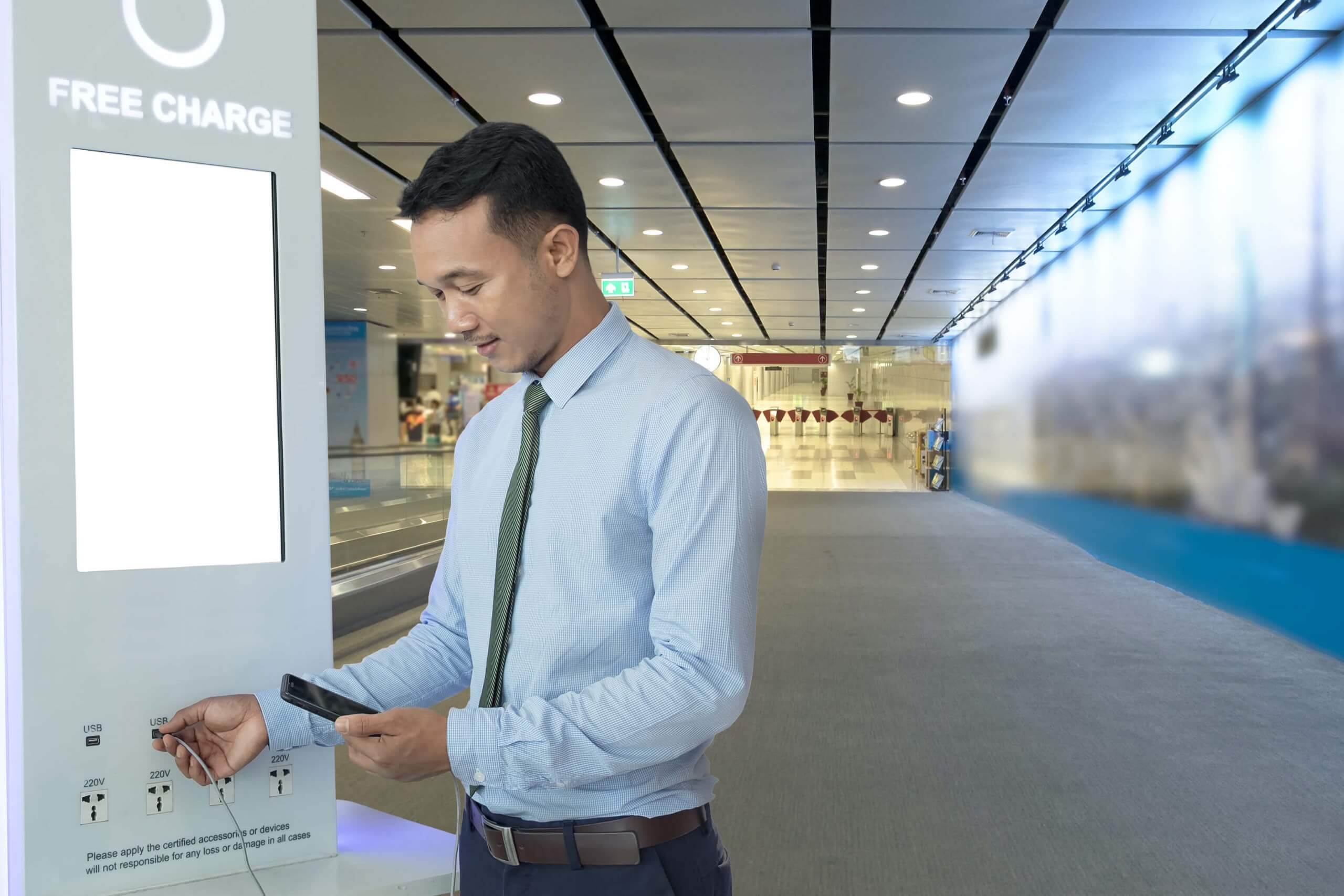
The big question: Officials in Southern California have issued an advisory declaring public smartphone charging stations unsafe. It believes the convenient plug-in kiosks could infect users with malware. However, it has no instances to point to where this has happened. So are they just crying wolf, or is there a real threat here?
On Friday, the Los Angeles District Attorney's Office issued a warning to travelers not to use public USB charging stations as their devices could get infected with malware that steals their data or locks up their phone.
"In the USB Charger Scam, often called 'juice jacking,' criminals load malware onto charging stations or cables they leave plugged in at the stations so they may infect the phones and other electronic devices of unsuspecting users. The malware may lock the device or export data and passwords directly to the scammer."
It's a pretty scary warning, but was it really necessary? Maybe not.
The advisory seems to have been dreamt up for a fraud-education campaign the office has been conducting called #FraudFriday and does not have any basis in real-world events.
The LA Country DA's office, when asked, admitted that it had not encountered any instances of someone's device being infected through a charging station in Los Angeles. It told TechCrunch that there were cases on the east coast of the US, but could not provide any details such as locations or dates that could be corroborated.
I haven't seen any evidence of malware being used in the wild on these things. It would be helpful if they could share evidence.
--- Kevin Beaumont (@GossiTheDog) November 14, 2019
Furthermore, security researcher Kevin Beaumont said in a tweet that he had never seen evidence that malware has been used on public charging stations. Digging into the subject a little deeper, TechSpot could not find any instances or reports where this has happened either.
That is not to say that the possibility does not exist. Several researchers have developed and demonstrated modified or cloned chargers and charging cables that can sniff data or execute commands on a device remotely, but these have all just been proof-of-concept projects.
It is also not the first time that authorities have issued a advisory on similar grounds. Back in 2016, the FBI issued a warning after security researcher Samy Kamkar demoed his KeySweeper proof-of-concept. It was an Arduino board small enough to fit inside the case of a USB charger and was capable of logging keystrokes from wireless Microsoft keyboards.
The bottom line is that more than likely, you are safe using a public charger --- at least for now. Frankly, there are just easier ways to accomplish the same task that don't involve tampering with private property in a highly secured facility or leaving suspect devices behind with cameras watching your every move.
That said, it never hurts to be vigilant and carry a wall charger with you when you travel. Most people probably already do, but it often ends up staying in the luggage.