What just happened? Acer has confirmed an unauthorized user recently broke into one of its data servers. Although the company's investigation remains ongoing, the Taiwanese PC specialist said there is no indication that any consumer data was stored on the victimized server. Still, that doesn't mean it isn't a problem as technical documents and corporate IP can still be very damaging in the wrong hands.
Earlier this week, a hacker published a classified ad for 160GB of "various confidential stuff" from Acer. The seller claimed the haul consists of 2,869 files across 655 directories and includes a variety of content such as service manuals, ISO files, BIOS and ROM files, confidential slides / presentations and more.
The hacker said there is so much content that it will take days just to catalog it all. The seller added they will only accept Monero (a decentralized cryptocurrency) for payment, and would only do the deal with a middleman. No price was listed; whoever makes the highest bid will presumably get the goods.
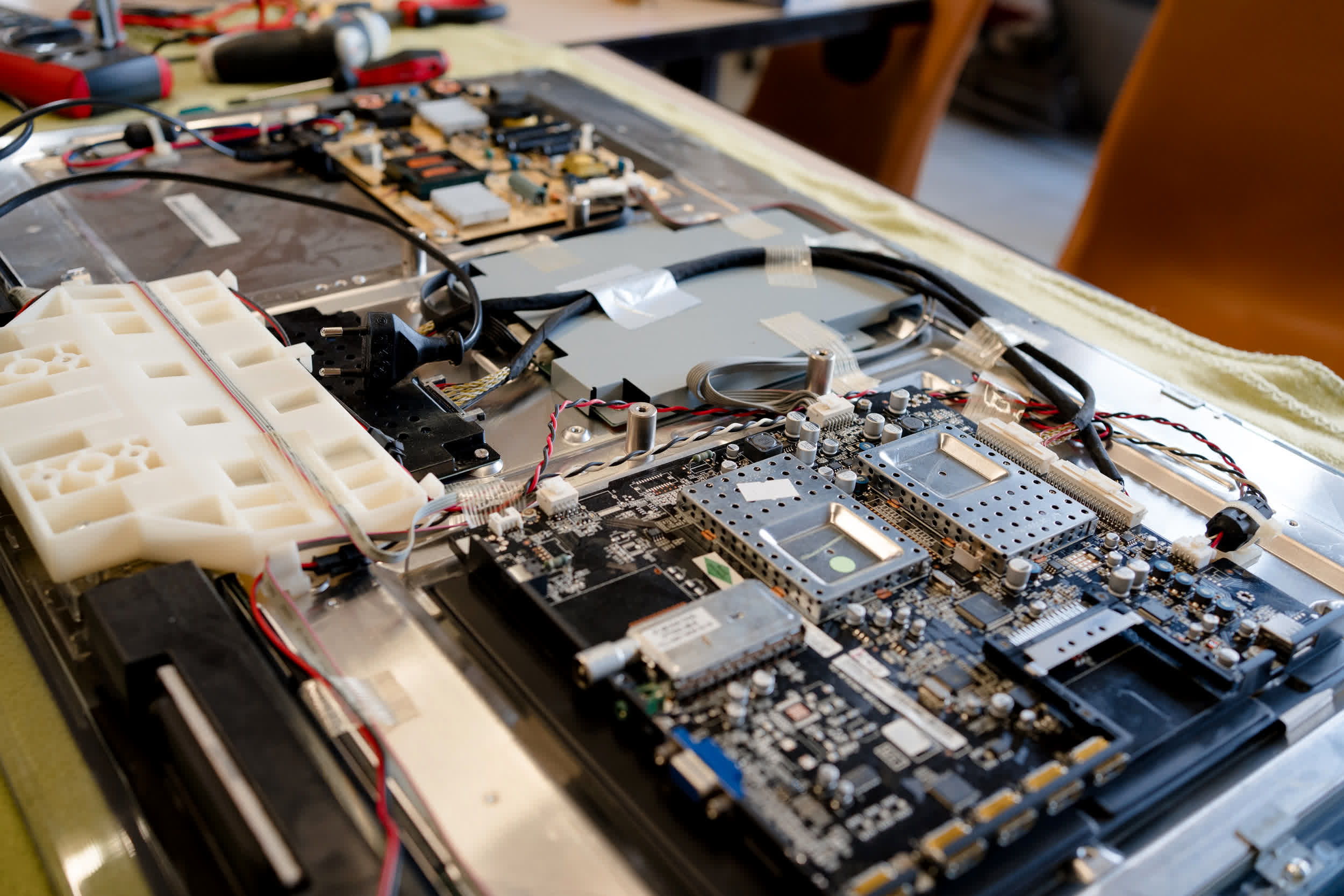
An Acer spokesperson told The Register that the server in question hosted documents used by repair technicians.
As security expert Erich Kron correctly highlights, not all data breaches need to contain financial details or information about customers or employees to be damaging. "In this case, Acer is potentially looking at the release of some of its intellectual property and potentially sensitive company documents," Kron added.
Technical details about products or corporate procedures could be extremely valuable to competitors seeking to replicate Acer's success. What's more, hackers could glean important insights about the inner workings of products or services from the documents that could lead to new exploits.
This is not the first major security incident Acer has dealt with in recent memory. Back in March 2021, the company was hit by the REvil ransomware. Attackers demanded $50 million in Monero in exchange for the decryption key.
Months later, hackers infiltrated Acer servers operating in India, reportedly making away with 60GB of data in the process. A secondary attack on servers in Taiwan followed. In both incidents, a group known as Desorden claimed responsibility.
Image credit: Hugo Clement
