Bottom line: Gigabyte has addressed a sketchy feature found on more than 260 motherboard models that could have allowed an attacker to install malware on a system. Some may be surprised that Gigabyte isn't shutting down the updater entirely. It is sticking around, just with better security to make it harder for a prospective attacker to leverage it for malicious activity.
Firmware security services provider Eclypsium came forward with their findings late last month. In short, they discovered Gigabyte was using code in motherboard firmware to quietly run an updater program that connects to the Internet to download and subsequently install firmware updates. The researchers noted that code was being downloaded to users' computers without being properly authenticated. Worse yet, it sometimes was delivered over an HTTP connection instead of the more secure HTTPS.
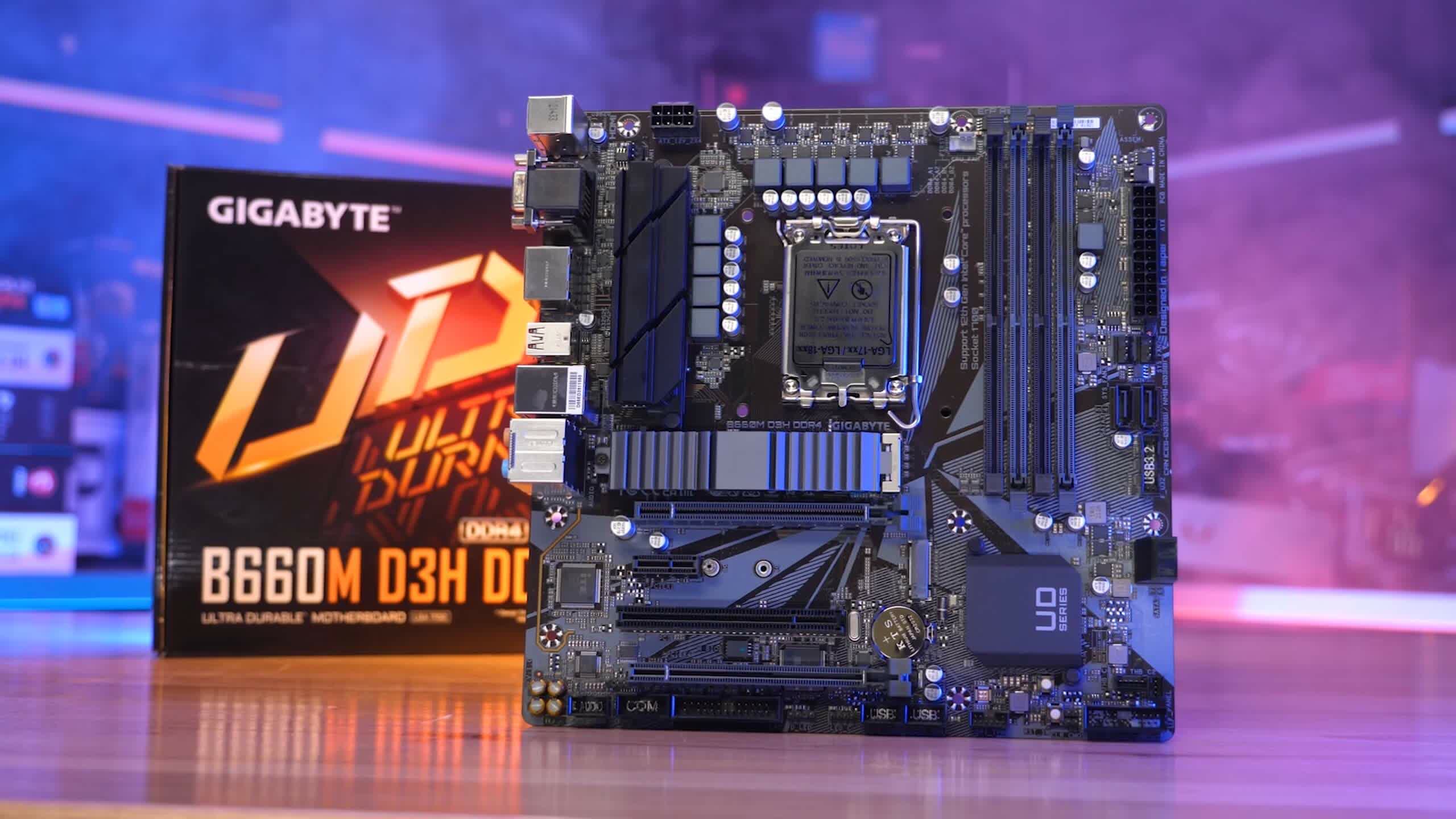
Shortly after Eclypsium broke its story, Gigabyte announced it had updated Intel 700 / 600 and AMD 500 / 400 BIOS available on its website to download and install. Gigabyte said updates for Intel 500 / 400 and AMD 600 series boards would also be released on the same day, and it seems that has indeed happened.

According to Gigabyte, the fix involves stricter security checks during the OS boot process including:
- Signature Verification: Gigabyte has bolstered the validation process for files downloaded from remote servers. This enhanced verification ensures the integrity and legitimacy of the contents, thwarting any attempts by attackers to insert malicious code.
- Privilege Access Limitations: Gigabyte has enabled standard cryptographic verification of remote server certificates. This guarantees that files are exclusively downloaded from servers with valid and trusted certificates, ensuring an added layer of protection.
If you are running one of the more than 260 affected Gigabyte motherboards, it would be a good idea to go ahead and pick up the latest BIOS update. In the description on Gigabyte's support page for your update, you should see a reference addressing download assistant vulnerabilities reported by Eclypsium Research.
For those that'd rather not fool with the feature at all, head to the UEFI / BIOS and look for the the App Center Download & Install feature, and disable it if the option exists.