In three weeks, the FBI could knock millions of infected systems offline by disabling some DNS servers. In November, Estonian authorities arrested six men suspected of using "DNSChanger Trojan" malware to redirect victims to malicious websites and block them from genuine security sites that might've removed the infection.
According to a report by Brian Krebs, the Trojan was on over four million computers in more than 100 countries, including 500,000 in the US – and not just home users, either. The malware is reportedly still present on computers at half of the Fortune 500 companies and at approximately half of all federal agencies.
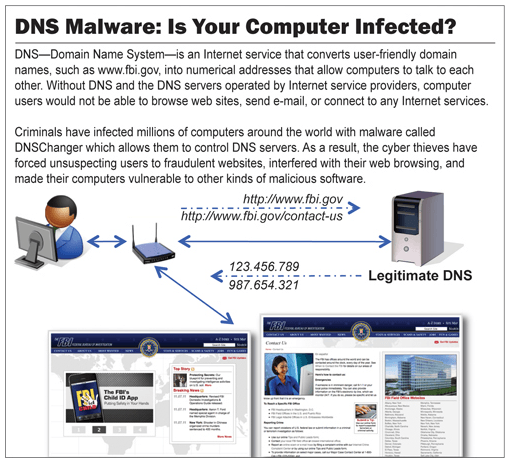
When the criminals were arrested, authorities replaced their malicious DNS servers with legitimate ones. Without doing so, victims would be presented with DNS errors as their machines sent requests to the disabled rogue servers. The clean servers allow infected users to visit their desired destinations as normal.
With the fresh servers in place, investigators could monitor the IP addresses of affected users and alert their Internet Service Providers. From there ISPs aided users in cleaning their computers. Sadly, that process hasn't been as quick as desired and many users could learn about their infection the hard way next month.
Come March 8, the court order allowing the feds to replace the bogus DNS servers will expire. Unless that's extended, the surrogate servers will be unplugged and millions still plagued by DNSChanger will lose Web access. Even the order is prolonged, experts worry the cleanup will take years as with Conficker.
"At this rate, a lot of users are going to see their Internet break on March 8," said Rod Rasmussen, president and CTO of security firm Internet Identity. He added that pulling the plug might hasten the cleanup process. "It certainly would be an interesting social experiment if these systems just got cut off," he quipped.
Checking your system for DNSChanger is relatively simple. You can use ipconfig /all in the Windows command prompt to get your DNS information, which can be compared against the numbers here. The DNSChanger Working Group also provides a list of free resources that'll help you clean your machine(s).