Experts at Russian computer security company Kaspersky have come to the conclusion that parts of the Duqu Trojan are written in an unknown programming language. Much of the code is identified as standard C++ but the team is clueless as to the origin of other segments and is asking the programming community for assistance.
Duqu borrows heavily from another high-profile security threat, Stuxnet, with some even referring to it as Stuxnet 2.0. The code in question is part of the Payload DLL, a section of the trojan that sends and receives instructions from an outside source once it has infiltrated a system. It is object-oriented but otherwise unlike anything the team at Kaspersky has seen before.
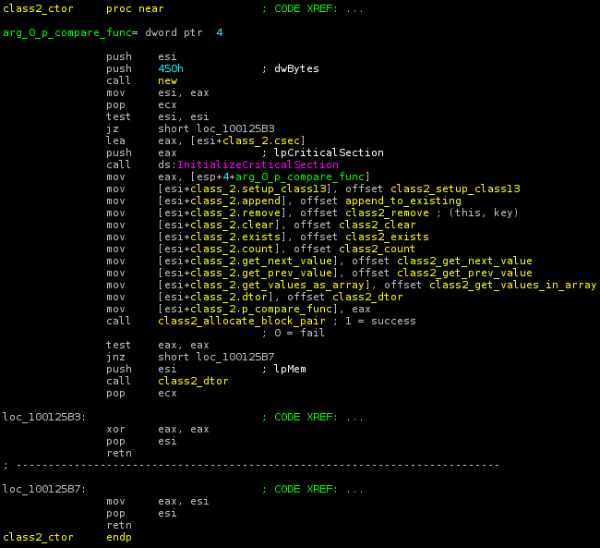
Experts have dubbed this portion of code the Duqu Framework and based on the sheer complexity of the instructions, it's believed that the trojan is funded by a wealthy organization or a national effort.
"With the extremely high level of customization and exclusivity that the programming language was created with, it is also possible that it was made not only to prevent external parties from understanding the cyber-espionage operation and the interactions with the C&Cs, but also to keep it separate from other internal Duqu teams who were responsible for writing the additional parts of the malicious program," said Alexander Gostev, chief security expert at Kaspersky.
Igor Soumenkov from Kaspersky has authored a blog post detailing information on the Duqu Framework and asking those in the programming community to help identify the mystery code. This is what the team has concluded thus far.
- The Duqu Framework appears to have been written in an unknown programming language.
- Unlike the rest of the Duqu body, it's not C++ and it's not compiled with Microsoft's Visual C++ 2008.
- The highly event driven architecture points to code which was designed to be used in pretty much any kind of conditions, including asynchronous commutations.
- Given the size of the Duqu project, it is possible that another team was responsible for the framework than the team which created the drivers and wrote the system infection and exploits.
- The mysterious programming language is definitively NOT C++, Objective C, Java, Python, Ada, Lua and many other languages we have checked.
- Compared to Stuxnet (entirely written in MSVC++), this is one of the defining particularities of the Duqu framework.
Those with any insight are encouraged to submit a comment on the blog post.