Microsoft has disrupted an emerging botnet along with more than 500 strains of malware after taking control of a malicious .org domain this week. Last August, Microsoft learned that many systems sold in China were preloaded with malware, including strains linked to Nitol, a botnet the company had been investigating.
Microsoft's Digital Crimes Unit (DCU) purchased 20 computers (split between laptops and desktops) from several sources in China. One of the systems contained Nitol malware, while three others had different infections. Microsoft determined that the computers were infected via counterfeit versions of Windows laced with malware, presumably installed by cybercriminals at unsecure points throughout the supply chain.
Of the four compromised PCs, only the Nitol-containing system attempted to contact a command and control server, so that's where DCU focused its efforts. The group gathered all sorts of technical information on Nitol, a summary of which you can read here (PDF). The most important detail is that Microsoft tracked the botnet to the domain 3322.org, which also turned out to be a haven for other forms of malware.
"In addition to hosting b70, 3322.org contained a staggering 500 different strains of malware hosted on more than 70,000 sub-domains," assistant general counsel of Microsoft's Digital Crimes Unit Richard Domingues Boscovich said. The malware included variants that could remotely enable a computer's microphone and webcam, record a user's keystrokes, participate in distributed denial-of-service (DDoS) attacks and more.
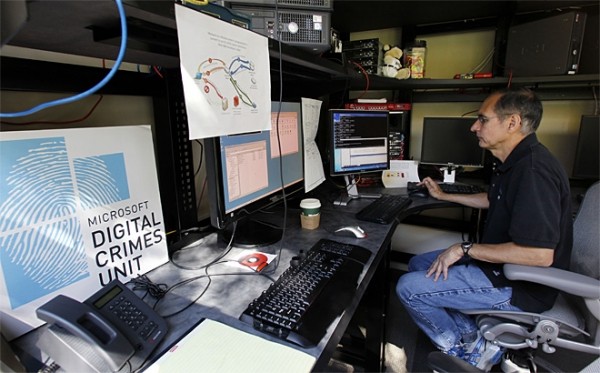
Senior manager David Anselmi pictured in the DCU labs (credit: AP/Elaine Thompson)
On September 10, Microsoft obtained a US court order to seize 3322.org along with an ex parte temporary restraining order against its registered owner, Peng Yong, as well as his company and other John Does. In doing so, Microsoft has been able to block the operation of Nitol along with the 70,000 malicious subdomains. It's unclear how many innocent users are involved, but Microsoft says over 37 million malware connections have been blocked from 3322.org since the company gained control of the domain.
This marks Microsoft's second botnet takedown in six months and the fourth in less than three years. In February 2010, the company aided security experts and law enforcement with disabling Waledac, one of the 10 largest botnets in the US at the time. Microsoft claimed another scalp last March when it tackled Rustock, a botnet that had been composed of more than a million infected machines worldwide. The company helped shut down the 41,000-strong Kelihos botnet last September, and in March of this year, Microsoft sued 39 individuals involved with the operation of Zeus, malware suspected of infecting over 13 million PCs.