One of the benefits of using an obscure operating system like Linux is that, well, nobody uses it. That means you don't really have to deal with all of the virus and malware associated with Windows and to a lesser extent, OS X.
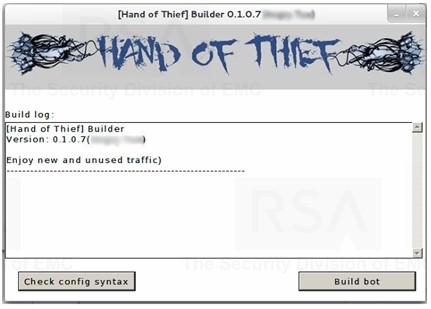
Those times, however, may be changing as a new Linux trojan has been discovered in the wild. According to the RSA (the security division of EMC), a Russian-based cybercrime team has unleashed a banking trojan known as the Hand of Thief.
The trojan is said to be no different than what you'd find on a Windows machine. At its core, it consists of a "form grabber" designed to steal the login credentials of those using Internet banking. Specifically, the trojan captures the username and password in addition to the timestamp of when you logged in, the URL of the site you logged in to and perhaps even your web browser's cookies.
The collection of data is then sent to a command-and-control server at which time your information will likely be sold to the highest bidder. From there, a crook would begin to rack up charges on your behalf either until the account is drained or you notice the suspicious behavior.
The trojan is said to work on 15 different Linux distributions including popular choices like Ubuntu, Fedora and Debian. It attacks the most common web browsers such as Firefox, Chrome, Aurora and Ice Weasel. The good news at this point is that there isn't really a solid delivery mechanism for the package. The trojan's "sales agent" suggests using e-mail and social engineering as methods of infection.