Encryption methods currently in use are quite strong and secure by today's standards but that won't always be the case, especially if large quantum computers end up being built.
As Google software engineer Matt Braithwaite explains, quantum computers take advantage of aspects of quantum physics to solve specific problems dramatically faster than conventional computers are currently capable of. One area they are especially effective at solving has to do with securing digital communications.
In theory, if a large quantum computer is built, it may be able to retrospectively crack the cryptographic primitives used in TLS, the security protocol behind HTTPS. That means that any encrypted Internet communications recorded today could be unmasked with a quantum computer in the future which is a major concern for data that needs to remain confidential for decades to come.
Again, there's no guarantee that large quantum computers will ever be built but Google doesn't want to take any chances which is why they're experimenting with post-quantum cryptography, or the study of cryptographic primitives that remain secure even against quantum computers.
Braithwaite said they've launched an experiment in Chrome where a small number of connections between desktop Chrome and Google's servers will use a post-quantum key-exchange algorithm called New Hope in addition to the standard elliptic-curve key-exchange algorithm. Stacking them, he said, allows them to experiment without affecting user security.
New Hope won't be the de-facto standard, Braithwaite adds, as they plan to discontinue it within two years and hopefully replace it with something even better.
The experiment is currently enabled in Chrome Canary, the most cutting-edge release of Chrome. To determine if it's being used, you can open the recently introduced Security Panel and looking for "CECPQ1."
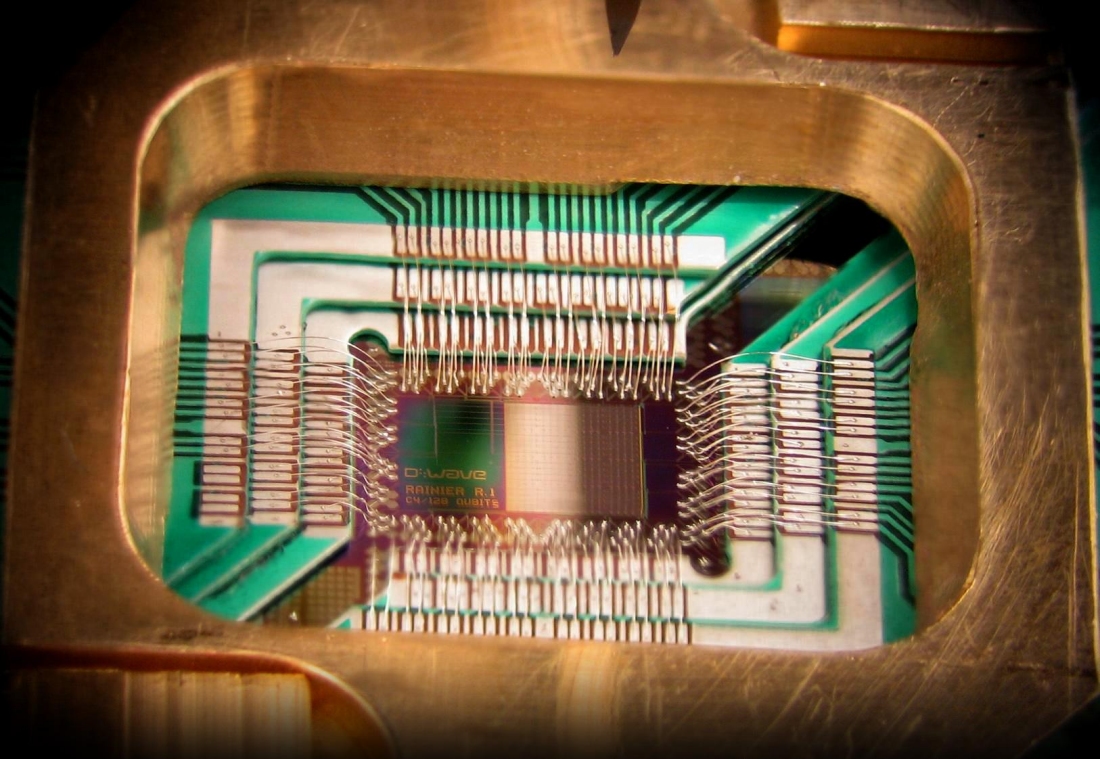
Image courtesy D-Wave Systems