
Based on a successful freemium model where users can clean already infected machines for free or get real-time protection for a one-time fee, Malwarebytes Anti-Malware already counts hundreds of millions of downloads and over five billion infections cleaned.
We recently had the chance to chat with founder and CEO Marcin Kleczynski about the company's early days, the evolution of malware, his views on the industry, and more.
Julio: Malwarebytes was a bootstrapped company and that usually makes for a unique story on how you got started. Tell us a bit about your background, what motivated you and how you went on creating the company.
Marcin: It's actually a very interesting story. I was working at a computer repair shop in Chicago as a technician during my last year in high school. It was me and the owner of the store. Every time a computer came in we would basically reformat it, regardless if it had a minor infection. Rootkits were still new, Ad-Aware was still the popular software and threats were just starting to evolve. But I never quite understood why we would never try to attack the problem using tools that existed until I got infected at home. When that happened I tried McAfee, I tried Symantec, I tried a lot of stuff and nothing would remove the piece of malware.
This was six or seven years ago. I googled the problem and found a forum called SpywareInfo that was very popular back then. I signed up on the forum, posted my problem and three days later my machine was clean. We went through the typical process, HijackThis logs, running this and that tool... I was very happy that three days later my computer was fixed, but it was still three days later!
So I decided to stick around that forum. They were really cool people, I know a lot of them. Some time after that I started developing very small utilities. One of them was called "About Buster", which was the first freeware utility that I actually wrote. It tackled a common infection known as About:Blank that typical anti-viruses at the time could not clean. The app started to become popular, I was working individually at the time and someone approached me saying "We have this domain called Malwarebytes, we're not using it - do you want to buy it from us?" I said yes and that's how Malwarebytes was kind of unofficially founded.
"I was very happy that three days later my computer was fixed, but it was still three days later! Three days of waiting, not being able to use the machine as well as I wanted to."
As I was getting through college about four or five years ago, my college roommate and I started writing a utility called RogueRemover. It tackled a specific type of infection known as rogues, which are basically scams to try and steal your credit card information by tricking you into downloading a fake anti-virus software and warning you about a supposed infection that doesn't really exist.
RogueRemover ended up becoming the engine that got Malwarebytes Anti-Malware going. I started selling it to a very niche market. I setup a forum where people could report anything that I had missed or any false positives, helping me improve the software.
One guy by the name of Bruce Harrison was a very common contributor. It got to the point where he would report something and I would Google it but couldn't find any information. He was so quick I actually thought he was working for the bad guys. So I told him, "Hey, listen. I'm working on a product called Malwarebytes. I was wondering if you'd be interested in helping me out. I can't pay you right now, we don't have any money. We're doing this for free."
He agreed and we worked for a year developing this product. He handled the database side of things while I handled the rest. A year later we had a product. This was January 21st, 2008. It's when we actually launched our first Malwarebytes Anti-Malware version.
We were very upfront with our community. Every couple of days or so we uploaded the latest database and asked for people's help spotting things we had missed. That's been our approach ever since.
Bruce became our VP of Research and he currently manages the team of about 10 researchers globally. We brought on our VP of Development Doug Swanson who was actually a physics PhD student – we have a very diverse team. He had done some freeware utilities, same kind of story as mine. Doug stopped being a physics student and became a developer for Malwarebytes because he is very good at it.
We brought on Marcus Chung who's our COO and had previously worked on companies like GreenBorder, which was acquired by Google, and Sygate, which was acquired by Symantec. He helped move things forward from a business standpoint - opened an office in San Jose; brought in our support team in-house; built a sales team, and so on. We've just kind of been moving along trying to keep true to our community, keep providing that freeware utility but also try to build a company and sell some products, and be able to improve the technology, so that we can help people protect themselves against malware.
What would you say was Malwarebytes' big break that made you realize this was actually something you could do for a living?
Marcin: When I asked Bruce if he wanted to work for free and build this Malwarebytes anti-malware utility, I had no intention of ever making a living doing this. It was a side project to help everybody... It was a common problem and I wanted to do my part helping out. That's still true. I enjoy doing what I do and every time I get a letter saying, "Thank you so much for helping me" it makes me happy.
"Businesses understand that they can't get these kinds of products for free because we've spent millions of man-hours developing and providing support."
It finally hit me that we could build a business out of this when Marcus came on and we started selling to businesses. Businesses understand that they can't get these kinds of products for free because we've spent millions of man-hours developing, providing support, and so on. The minute that happened we started working on the enterprise edition, we started doing support for corporate customers, and so on. That was really the turning point for us, when I saw that corporate customers actually wanted to pay for our product and buy in bulk. Now there are Fortune 500 companies that are using Malwarebytes, sports teams, banks, huge companies.
Malwarebytes Anti-malware is a very popular Windows download on TechSpot. You offer this for free and it's fully functional. What kind of usage data can you share from the consumer side things?
Marcin: The first thing I should note is that the free product is not necessarily "fully functional". I mean, if you have an infection you can download the free tool and remove it, we don't charge you anything for that. However, we do sell a real-time protection module for users that need a more proactive solution with scheduled scanning. We also offer a 14-day trial for this.
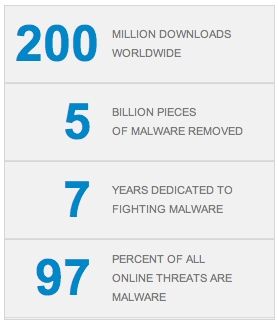
We have a few hundred million downloads and a few tens of millions of active users. But beyond those numbers what we care about is reach, how many people are we helping... We're working on some form of reporting for the site to show how many people we've protected, how many malware infections we've removed and so on.
You started this on your own and a lot of helpful people joined your team along the way. But now you have a reputation to maintain, and once you miss one thing, that might be enough reason for somebody to doubt your program. How do you keep up with new breeds of infections?
Marcin: That's a good question. Let's start with saying that we are an anti-malware product. We complement your antivirus software, we don't try to replace it. And even though we have a great detection rate, we never position ourselves as a do-it-all security software.
Our team can process three samples that look the same or act the same, write one signature / heuristic for it, and from there it will detect the entire family or even other families of malware.
I mean I only run Malwarebytes on my computer, and many advanced users can probably manage with this as well, but I would never recommend that to the average customer. For my mother, my grandmother, I always recommend a traditional anti-virus because they do go after stuff we don't: patched files, cookies, and so on. There are different criteria and having a layered security approach is a good idea. Our product is so light that it shouldn't be an issue.
That being said, we do have 10 researchers on our team who work full-time, and are exposed to all types of malware.
When we started the company I thought there was no way we could keep up with new threats. Antivirus companies have 500 people in research or more. But we were able to scale down the problem. Our team can process three samples that look the same or act the same, write one signature / heuristic for it, and from there it will detect the entire family or even other families of malware. We're very reliant on being able to use heuristic pattern matching and a combination of signatures to be able to do that.
Our researchers have about 300 different ways they can detect a piece of malware, so they pick and choose which tools they want to attack the malware with, and if it's done a good job it should actually detect more malware than that specific file. We've also built trace detection tools so researchers only need a specific piece of the malware and our engine will go find and filter out the rest.
That takes a huge burden off our researchers so they have extra time to spend on certain samples that require it or on potential false positives. We're very dynamic, our researchers are a very tight group, and they can move very quickly to handle all these things.
So, would you say these algorithms that help the process of identifying threats is a competitive advantage of yours that lets you get a lot done with a relatively small group of researchers?
Marcin: Absolutely. If you think about it, many traditional antivirus programs use engines that were built 15 years ago. They had no idea what malware would look like today. Our engine was built three years ago and that makes it easier for us to adapt as malware evolves.
Tell us about the process of taking community feedback and putting it into your software.
Marcin: We receive community feedback and implement it within two to six hours. We have two sub-forums as part of our larger forum called "False positives" and "Malware contribution". False positives are a big deal so if we have a researcher online and working at the moment the report comes in, it is typically answered within an hour. Say, for some reason we're detecting Microsoft Office as malware, someone will report this on the forum and an hour or two later after verifying the false positive we'll update a new database.
On the other sub-forum, as the name indicates, users can report anything we're missing and we'll download it, run it through our automated tools, do as much research on it as we can, and push out an update once we've figured it out. These are our users who are reporting malware so we act as quickly as possible. We know some of them might be managing huge networks of hundreds or thousands of computers so speed is important.

Now we're actually about 50 people strong. These people are working full-time on things like support, sales, forum moderation. I was doing all of this by myself when I first started. Over time the forum started looking a bit loaded, so I optimized some things here and there – merging some forums, improving descriptions, deleting inactive or spam accounts. I could have handed all this to someone else, but I feel the community is such a critical part of what we're doing, it's important to be involved.
What would you say is the difference between a virus and a malware?
We complement your antivirus software, we don't try to replace it. And even though we have a great detection rate, we never position ourselves as a do-it-all security software.
Marcin: Traditionally, viruses infected your system and tried to harm it for no specific reason. That's how traditional virus infections started. Malware, on the other hand, has a specific purpose, usually making money. So you have adware plaguing your machine with annoying ads, spyware stealing your passwords, Dialers which back in the day used your money to call paid numbers, keyloggers, and so on... all categorizable as malware.
Today both terms have started to merge together and become a bit more complicated. The main reason we call our software anti-malware is to distinguish ourselves from old antivirus software. We feel we react far quicker to threats that are hostile. We are more of a rapid detection engine for threats that evolve quickly and are more likely to affect you near term. Antivirus software often fails at that but they are a good support system for threats that have existed for the longest time but might still infect some users. Conversely, if you test our software with viruses that existed 10 years ago and are no longer active, we'd probably fail to detect them.
Would you say people writing viruses just want fame and people coding malware want money?
Marcin: Definitely. I think most of it has really moved into money nowadays, though.
Are infections getting more sophisticated?
Marcin: They definitely are. Things are getting sneakier, that would be one of the best ways to put it. Infections are hiding themselves better, they're tricking users using social engineering, and often times they are much more legitimate looking than before.
Back in the day when the first rogues came out they used to be very unsophisticated. Just taking a glance at a rogue website, for example, anyone with a bit of experience online could identify it as a scam. There were typos, awkward images, everything looked fake. Nowadays, you could see a rogue site for Microsoft Security Essentials and have a harder time telling it apart from the legitimate one at first glance.
Everything looks very professional, they even have online chat support, prices similar to the actual software they are spoofing, etc. They're also using advanced technology and rootkits to get around security software or make it harder for them to remove the threat even after a reformat – that's one of the first things we look for. It makes you wonder why aren't more of these guys working for us if they're so good at this.
