Windows' Security, Mobile, Competitors
In your opinion has Windows gotten any better security wise in the past five years?
Marcin: To some extent. Clearly from XP to Vista to Windows 7 there have been attempts to make machines more secure, with the introduction of User Access Control, for example. It was buggy in Vista and kept asking users over and over again if they wanted to allow a certain program to run.
I think it wasn't very clear to users what User Active Control really was. When people keep seeing the same prompt they don't think twice, they just click yes. It got to the point that users either disabled it or just clicked allow and got going. And that's why malware is so successful, people don't want to be bothered with every little thing, they just click yes and keep doing what they are doing. Windows 7 fixed some of this.
When people think Microsoft they don't necessarily think security. A lot of people prefer to rely on a third party solution – especially in a corporate environment.
Microsoft has been bundling more and more software to help protect users' machines, such as Security Essentials and Windows Defender. So, I think that's been a great leap forward. I don't feel those products are mature enough as some third-party security solutions, but they are moving in the right direction.
Another thing is that when people think Microsoft they don't necessarily think security. A lot of people prefer to rely on a third party solution – especially in a corporate environment.
Same with Internet Explorer. Microsoft's browser has been moving in the right direction and becoming more secure. You remember Internet Explorer 6. Well, 7 and 8 are far better. But people that are worried about security still use Chrome or Firefox, and for good reasons. A lot of people just choose to use third party software, versus relying on Microsoft software.
Do you see a future for Malwarebytes outside of Windows and on alternative operating systems like OS X and Linux, maybe mobile?
Marcin: We have a website blocking module that basically blocks your computer from ever accessing servers that can contain malware. So, if you visit a website that was hijacked and has an 'iframe' in there trying to pull a malicious executable and get it on your system, Malwarebytes will let the page load but block access to the executable from a malicious server. We're hoping this website blocking module can be ported, we've actually started the process to get it on Linux, Mac and mobile platforms.
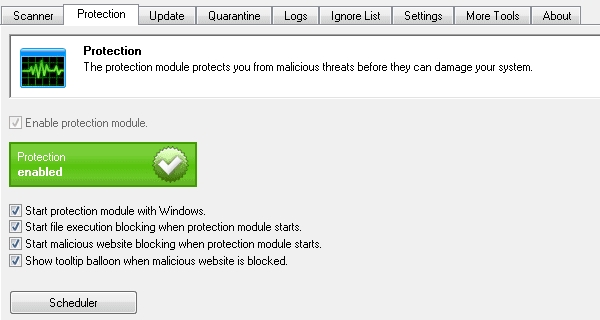
We expect to have at least that part of our technology available by the end of this year, if not sooner, because it is a very valuable piece of technology that lets users block malware from the source.
The Flashback malware that hit OS X a few months ago, for example, that wouldn't have been an issue for someone with this blocking module. We would track servers pushing the malware and block them. So, this is just a part of our technology and it's a start. It could evolve into a full security product for those platforms, but that's a bit of a tougher issue.
To clarify, this module works only within the browser or is it more like a firewall that monitors your entire network stream?
Marcin: It's not a browser add-on. It works at the lowest possible level. If you are in your browser, if you're in Skype. I've actually had it block a torrent transfer – a legitimate download of LibreOffice – because I was downloading from a peer that had been involved in malicious activity.
There are two more things I want to add here. Let's say you download a sketchy piece of software, and once you start the installation process, it starts installing malware as well because they get paid money for every installation that people do. This is not an uncommon issue, whether it's adware or toolbars, some free applications make their money this way. In those cases our IP blocking module detects that connection and blocks it. So you can actually continue your install without installing any malware. So, that's number one.
Number two is let's say you download malware from a specific server that we failed to detect. That's our miss and unfortunately the malware is now installed. However, we can still mitigate part of the problem, because as soon as it starts pulling other malicious software from a server that we do know, we will block that transfer. This can prevent vital components of the malware to be downloaded, thus lowering the risk for you.
How do you think closed ecosystems like Apple's iOS or Microsoft's Windows Phone, which try to proactively filter out malicious software from making it into their stores, will affect your ability to get into the mobile market?
I personally don't see mobile phones as a valuable market for security software today. Potentially in the future and if that's the case we'll definitely be in there.
Marcin: That's a very interesting question. Unfortunately, I'm not well-versed in the mobile market. It seems to me that most of the time smartphones get compromised with malware it's because the owner installed applications from an unverified source at a third party store such as Cydia or the like. Maybe it's for the best that these ecosystems remain closed, whereas for desktops it's a different story. So, yeah, I don't have an answer to that question right now but those are some of my initial thoughts.
That means you're not actively looking to get into the mobile market?
Marcin: Not necessarily. It means that we need to find the experience that can help us do that. We've been researching and we do have some prospects. Part of it is porting over some of our technology as I was mentioning earlier. But I personally don't see it as a valuable market today. Potentially in the future and if that's the case we'll definitely be in there. I've never bought a security product for iOS, and I don't think many people have. I know they're already promoting some stuff for Android, though. We need to see where the market is going.
A couple of years ago we heard about an unfortunate incident with another security vendor which took your malware database and used it as their own. Is this the type of thing common in the industry? Were you forced to implement more efficient ways of detecting theft?
Marcin: I wouldn't say that's common in the industry but it did happen to us once. A couple of people approached us saying they had found a rival anti-malware product using our database as theirs. So what we did is plant a fake definition into our database and filtered it out on our end so our software didn't detect it, but theirs did. We called them out publicly. Of course, they played it down and said they weren't using our database, that it was just a false positive, but this was a file that we built ourselves, nobody had access to it and their software detected it as malware. So it was very easy for us to verify that they were in fact using our database.
We do have some other protections to make sure people can't easily take a part of the database and reverse engineer how our technology works. So that was a huge wake up call for us and we started taking some additional precautions since then.
Now we do a check every month or so with every vendor just to be sure. But it's not a common thing in the industry, it hasn't happened again, not even partially. Reputable security vendors have their own teams and processes and their own way of doing things, so they just focus on that. They don't need to steal from others.
What has been your experience competing against huge established players like Symantec, for example, which have been around for way longer than Malwarebytes, some of them for a decade or two.
I think the very, very huge vendors that have been around for a long time got too comfortable and had to kind of start overhauling their solutions. Speaking of Symantec, for example, it was a great product 15 years ago, a terrible one 5 years ago, and now they've gotten much better.
Marcin: The first thing I'd like to point out is that we don't pitch ourselves as direct competitors to those companies. As I said earlier, we want to complement anti-virus software, not replace it. We overlap in some areas and we do have a great detection rate, but we never position ourselves as a do it all security software.
But to answer your question, I think the very, very huge vendors that have been around for a long time got too comfortable and had to kind of start overhauling their solutions. Speaking of Symantec, for example, it was a great product 15 years ago, a terrible one 5 years ago, and now they've gotten much better. They are on the right direction. I still think they are a bit resource hungry compared to other solutions out there that are equally or more effective than theirs, though. I mean Malwarebytes is 10MB and can be uninstalled in 30 seconds.
They are doing a good job in some areas. They have 100, 200, or 1,000 times more customers than we have and dealing with all the support and sales part of the business is not easy. We rely a lot in our community. We have people contributing with us freely because they don't see us as the corporate giant that's trying to take all their money – and we're not. We're trying to provide a useful service for our users.
So that's my view. There are a few great products out there, like Avast, ESET, GFI, among others. All of these are reputable companies. We're compatible with all of them, we've even had some business discussions with them about marketing stuff and so on.
Some security vendors get deals with OEMs like Dell and HP to get their software pre-loaded on machines. To be honest, we're not big fans of this practice because usually what you get is a limited time trial, or one that we wouldn't have chosen in the first place. But it's one way to get market share. Have you considered or are already doing something like this?
Marcin: We do some of this in a very limited fashion. We work with a small distributor in Utah and a couple of others. But we're not dealing with HP or Dell, we're talking about somebody that installs two or three very reputable products and they actually bought the license on the customers' behalf. So it's already purchased when the computer reaches the customer's hands. The other thing we do is white label rebranding.
Basically, we have some deals in place with a handful of companies that sell rebranded versions of our products. They often remove some features to make it as easy to use as possible for a specific scenario, or make some interface tweaks to appeal a specific demographic.
For example, we license our software to a company that specializes in software for women, and also to companies that sell computers and offer customer support whenever anything goes wrong. I'm not saying any of these are our customers but think Geek Squad, Staples, Home Depot, and the like. That's just one of the opportunities we've taken and it's a growing part of our business.
The most likely source of infection in any computer environment is usually its weakest link: the user. Obviously, that works fine if you are in security software business, but do you think Microsoft and developers of other ubiquitous software like Adobe are doing enough to keep their users safe?
Marcin: I don't think that these companies are investing enough resources into the security of their products. I think security comes first, then usability. You already mentioned Adobe. Java is another good example. I know they try to fix bugs as fast as they can, but... come on, you need to bring in consultants, you need bring in the community to help you find vulnerabilities and make it worth their while.
If you look at Google Chrome – and I think Firefox too - they acknowledge people that find bugs within their software and even offer compensation depending on how significant the flaw is. So there are some things they could do to take the security of their users more seriously and to my knowledge they don't always do.
Clearly, Java and Flash have been some of the biggest exploitable tools out there and that hasn't changed much. And people think it's Microsoft's fault where it may not always be the case.
One last closing question: What's on your desk? Tell us about the platforms you rely on day in and day out for desktop computing, mobile and other any other gadgets
Marcin: Desktop, pen and paper for writing down ideas, iPhone reminders for anything that comes up during the day and I'm not by my computer. Lightning calendar for scheduling, headphones for taking calls. No other real gadgets.
Thanks for taking the time to answer our questions, Marcin. It's been a pleasure chatting with you. Any closing thoughts for our audience?
Marcin: A message that we want to get out there is that anti-malware and anti-virus software work together. Users should be running both to get sort of a layered security system. We're starting a campaign around that. Using only an anti-virus is not enough. They're not as fast as they used to be. We're here to help fill the gaps.
