
Security researchers are always on the lookout for breaking encryption algorithms. Brute force techniques aren't viable solutions given the time and resources required, which has led to the development of other, more creative methods of getting around encryption. Using the background electromagnetic radiation given off by a computer system's electronics, a team of researchers at Fox-IT and Riscure were able to recover an AES256 key in just 5 minutes using a $230 device.
This AES attack is a type of side-channel attack and is one of the more popular modern ways to obtain classified or encrypted information. The attacks involve capturing data based on the physical implementation of a system rather than a brute force or exploit of the system itself. Other similar attacks include power analysis to characterize the system doing different encryption operations, acoustic analysis to pick up minute audio queues from the processor, and attacks that purposefully introduce faults into the system.
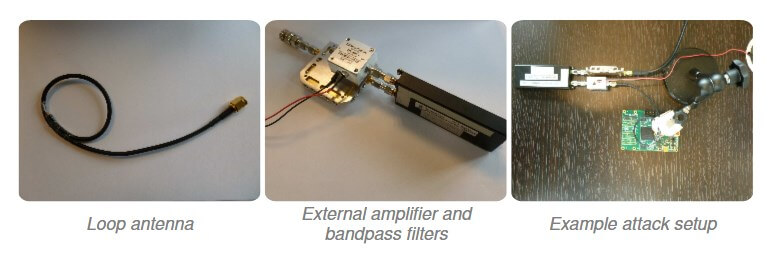
Without proper shielding or masking, systems can be very difficult to protect since traditional security methods like patches or complex encryption won't have much of an effect. The researchers were able to carry out the attack with a loop antenna, an amplifier, a filter, and a software-defined radio receiver on a USB stick. The whole setup is small enough to fit in a pocket or briefcase and only needs 5 minutes to capture a key from a meter away.
The device works by capturing electromagnetic radiation coming from the target. It then correlates these data to power usage and known encryption profiles. By comparing characteristic power usage spikes to the known values for each of the 256 values of a byte, researchers were able to effectively recover the key. They only needed to try 8,192 guesses instead of the 2^256 that a brute force would take.
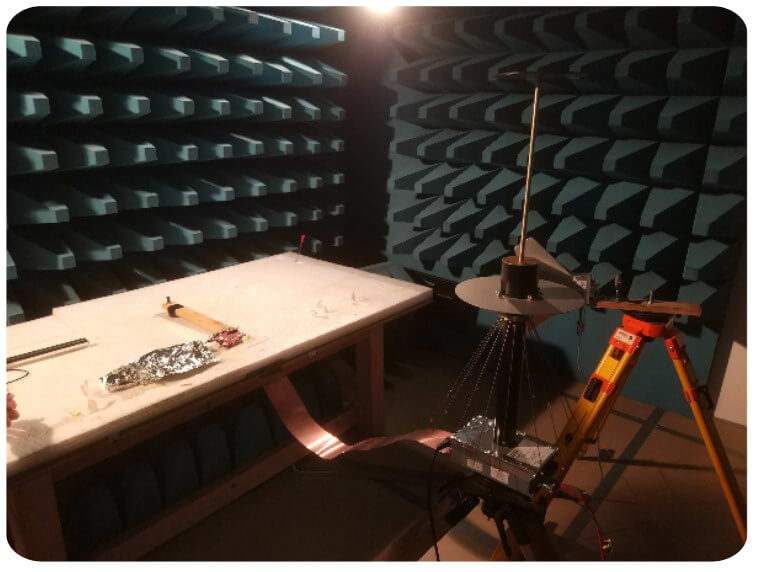
If all of this has you worried, you'll be happy to know that this was carried out in a controlled lab environment. The device and target were both shielded from all external electromagnetic waves. The same technology, known as Van Eck Phreaking, has also been used by an Israeli team to capture a computer password through a thin wall and other mobile phone keys.
https://www.techspot.com/news/70172-researchers-recover-aes256-key-using-230-device.html