It's been years in the making but USB Type-C finally made its grand entrance this past week on Apple's new MacBook and Google's new Chromebook Pixel 2 a day later. While it's great to finally see the successor to modern-day USB, there's plenty to keep the security conscious among us up at night.
For starters, we have to be cognizant of the fact that USB Type-C is still based on the USB standard which means it's still susceptible to all of the same nasty attacks that today's solutions are. Things like the BadUSB malware aren't exactly new but what is new is the inclusion of power over USB.
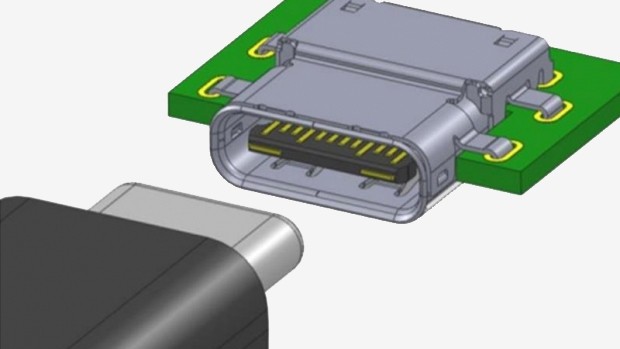
For those not aware, the USB Type-C port combines data and power into a single connection. As The Verge points out, those truly paranoid about exploitation would simply put a piece of tape over their USB port. Now that the port doubles as the power connection, that's no longer an option.
BadUSB is particularly worrisome as it takes advantage of a fundamental flaw in the way USB works. There are some USB drives that now protect against this flaw but the vast majority of drives and computers remain wide open.
One of the researchers that first uncovered the flaw, Karsten Nohl, said there is no solution even in sight with USB Type-C. That makes sense considering the fact that USB is open and built on the concept of backwards compatibility.
With power being supplied over USB, there now exists the possibility of infecting a charger. Unlike USB sticks, it's entirely plausible that people will "borrow" a charger from someone in a coffee shop or even a "friend." Once a system is infected, said infection could spread to every charger the computer comes in contact with, thus casting what could wind up being a massive web of infection.
