Guild Wars 2 base game now free, dev promises no aggressive microtransactions Big changes are coming to the PC MMO Guild Wars 2. Today at PAX Prime, developer ArenaNet announced that the Guild Wars II base game is available to play for free beginning now, August 29. The business model transition comes three years after the game was originally released in August 2012. In that time, the game has seen more than 40 free content updates and sold in excess of 5 million units. Gamespot
No, Microsoft is not spying on you with Windows 10 Buy tinfoil futures. I'm dead serious. There is apparently a growing and very vocal population of people who believe that Windows 10 is basically a 1984 telescreen come to life. They are convinced that with Windows 10 Microsoft has built a spying apparatus not seen since the height of the Cold War, scraping up every detail of your life and feeding it back to Redmond for who knows what nefarious purposes. ZDNet (Microsoft's Privacy Statement)
BMW: All models electric within decade German luxury car giant Bayerische Motoren Werke AG or BMW Group is looking to go all-electric over the next 10 years due to the upcoming stricter carbon emission laws. Virtually every BMW model would be converted to electric drivetrains, including range-extending engines and plug-in hybrids. The transition will see even the company's top-selling 3 Series sport sedans turned into plug-in hybrids. Nasdaq
The virtual reality of John Carmack From the storyteller on a Greek stage to the latest in curved-screen tvs and IMAX theaters, the holy grail of entertainment has always been immersion: putting the audience "inside" the drama, transporting them to another time and place. To date, that has been an "over there" experience, leaving a physical gap that reminds our senses that we're not truly immersed. But that's beginning to change, thanks to the advent of modern Virtual Reality (VR) technology. D Magazine
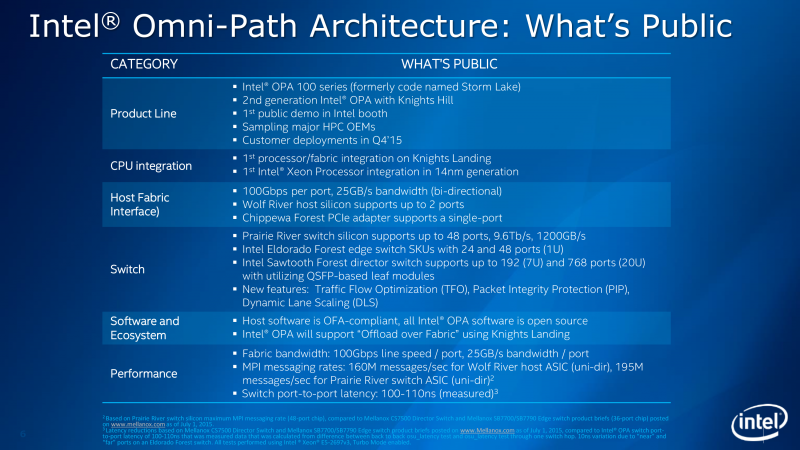
Intel reveals details of its Omni-Path Architecture interconnect One of the toughest challenges in computing is building large-scale systems like those used in the world of high-performance computing (HPC). Currently, such systems typically communicate between nodes over an interconnect like Ethernet or Infiniband, but Intel intends to replace those technologies with a new interconnect known as Omni-Path Architecture. The Tech Report
In search of the keys to the virtual city I'm not the first man to believe that he might fix London. It's unlikely that, in 1666, the baker Thomas Farriner started the Great Fire because he was fed up with the preposterous rent of the city's shoebox apartments, the disembowelment of its cultural institutions, or its plague of franchise eateries and foreign oligarchs. Nevertheless, London had to be rebuilt (by Wren, Hawksmoor, and the rest) on the ashes of Farriner's mistake (an unattended oven), just as, when I loaded up my first game of Cities: Skylines, released in March by the Finnish developer Colossal Order, I planned to rebuild the city on the embers of my resentment. The New Yorker
Crash-tolerant data storage In a computer operating system, the file system is the part that writes data to disk and tracks where the data is stored. If the computer crashes while it's writing data, the file system's records can become corrupt. Hours of work could be lost, or programs could stop working properly. At the ACM Symposium on Operating Systems Principles in October, MIT researchers will present the first file system that is mathematically guaranteed not to lose track of data during crashes. MIT
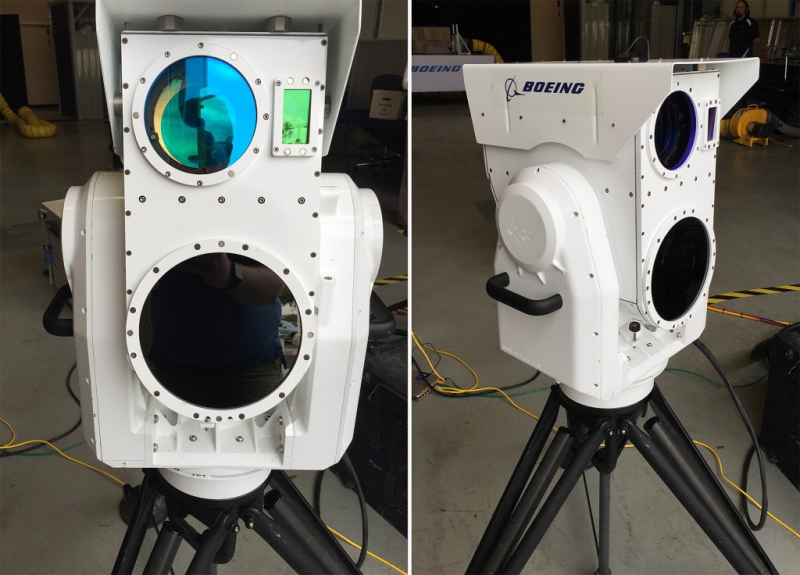
Welcome to the world, drone-killing laser cannon Hang on to your drone. Boeing's developed a laser cannon specifically designed to turn unmanned aircraft into flaming wreckage. The aerospace company's new weapon system, which it publicly tested this week in a New Mexico industrial park, isn't quite as cool as what you see in Star Wars – there's no flying beams of light, no "pew! pew!" sound effects. But it is nonetheless a working laser cannon, and it will take your drone down. Wired
How security flaws work: The buffer overflow The buffer overflow has long been a feature of the computer security landscape. In fact the first self-propagating Internet worm – 1988's Morris Worm – used a buffer overflow in the Unix finger daemon to spread from machine to machine. Twenty-seven years later, buffer overflows remain a source of problems. Windows infamously revamped its security focus after two buffer overflow-driven exploits in the early 2000s. Ars Technica
The cheapest FreeSync monitors you can get under $200 There's an interesting trend going on. Nvidia graphics still dominate the graphics cards market in sales and in critical acclaim while AMD has clearly fallen behind. And yet, AMD is getting every monitor manufacturer to adopt its Adaptive Sync-based FreeSync monitor frame rate synchronization technology. All this while Nvidia's G-sync has nearly no support at all in the gaming display segment. Softpedia
Sony's Xperia Z5 smartphones will include a fingerprint sensor on the side Over the last few weeks, we've seen an increasing pace of leaked photos of Sony's next smartphone, the Xperia Z5. Actually, we're expecting three different models: the Z5, the Z5 Compact, and the Z5 Premium (or maybe Z5 Plus, depending on who's doing the leaking). All three will stick to Sony's tried and true design language, which is a spartan and squarish combination of metal rails and glass. The Verge (press pics)

Apple takes Washington As Apple chief Tim Cook quietly slipped out of a public meeting at the White House for a private lunch with Eric Holder in December 2013, the attorney general braced himself for a rough encounter. His Justice Department had sued Apple more than a year earlier, after all, for the way that the company priced its e-books, touching off a bruising legal war between the two. And this time Apple seemed even more apoplectic. Politico
Google tells developers how to get around Apple's new security rules so they can keep selling ads Apple says it cares a lot about privacy. Just ask Tim Cook. Hence, its new iOS 9 operating system will boast a new feature, called App Transport Security, or ATS, which is supposed to require iPhone app developers to use an advanced security protocol. The idea is to keep the operating system lock tight. Recode
A salute to solo programmers Parkinson's Law tells us that "work expands so as to fill the time available for its completion". Applied to software, this means that applications tend to bloatware, obese programs whose complexity makes them nearly impossible to debug and maintain. Today, we look at happier counterexamples, past and current, of ambitious products created by "hermit programmers". Monday Note
Learning Verilog for FPGAs: Hardware at last! Getting into FPGA design isn't a monolithic experience. You have to figure out a toolchain, learn how to think in hardware during the design, and translate that into working Verliog. The end goal is getting your work onto an actual piece of hardware, and that's what this post is all about. Hackaday
Writing a Game Boy Advance game I spent a lot of time as a kid playing (generally, pretty terrible) games on my Game Boy. Having never written code for anything other than 'regular' general purpose computers before, I've been wondering recently: how easy is it to write a Game Boy (Advance) game? Reinterpretcast