Fiat Chrysler has been criticized after a patch it released for the Jeep Cherokee security flaw was mailed to more than a million customers on a USB drive via the US Postal Service.
In July, two hackers demonstrated a zero-day exploit involving the infotainment system of a Jeep Cherokee. The pair showed how they were not only able to remotely control the vehicle's windshield wipers and radio, but could also kill the engine, put the jeep into neutral and apply or completely disable the brakes.
Chrysler's decision to mail a patch out on a USB stick has come under fire from several security experts, who say it could pave the way for a future attacker to send out their own spoof letters and USB drives so as to trick users into installing rogue software on their vehicles.
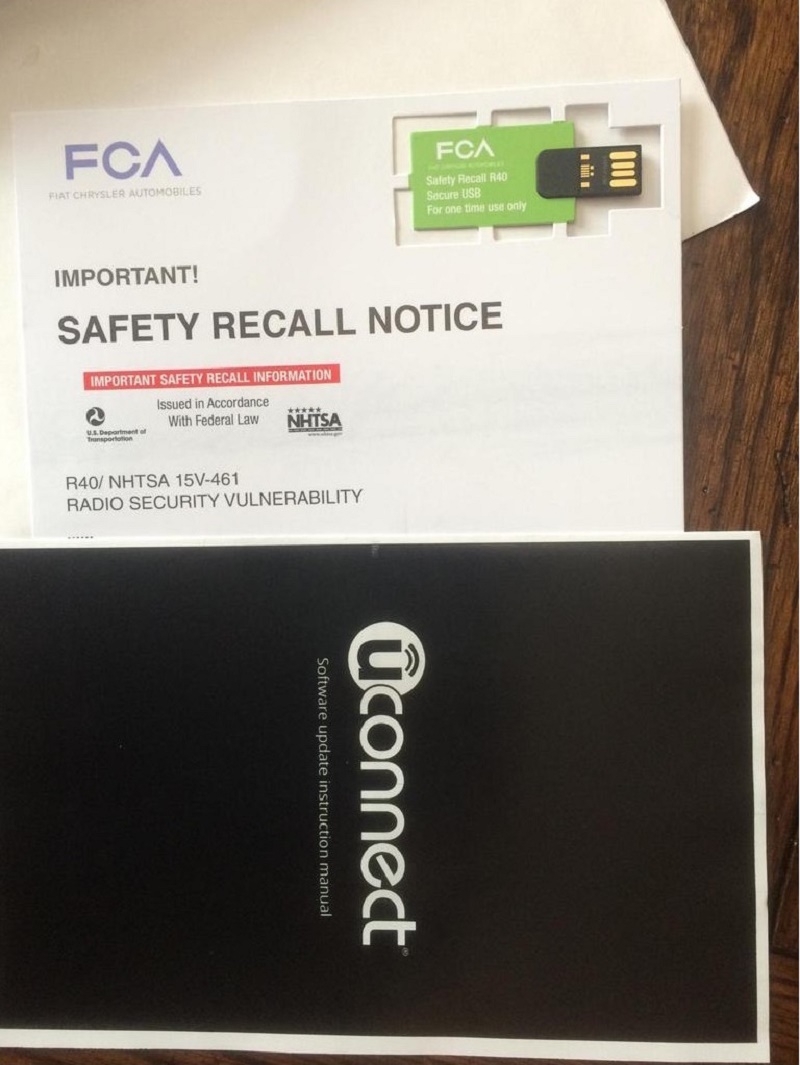
It's been suggested that Fiat should include a method for validating the authenticity of the USB drive so users can verify it really has come from them before it's plugged in. There's also the fear that hackers will be able to pull the data off the USB and reverse-engineer it, giving them an insight into how the vehicles receive their software updates and perhaps finding new vulnerabilities to exploit.
"An auto manufacturer is basically conditioning customers into plugging things into their vehicles," says Mark Trumpbour, an organizer of the New York hacker conference Summercon.
Chrysler has responded by pointing out the security concerns arising from the letters are only "speculation," it also pointed out the USB drives are read-only. "Consumer safety and security is our highest priority," the spokesperson added. "We are committed to improving from this experience and working with the industry and with suppliers to develop best practices to address these risks."
Days after the Jeep hack story went public, Chrysler released a security update for download on its website. It also implemented a layer of protection on the Uconnects' Sprint network designed to block the wireless attack.
