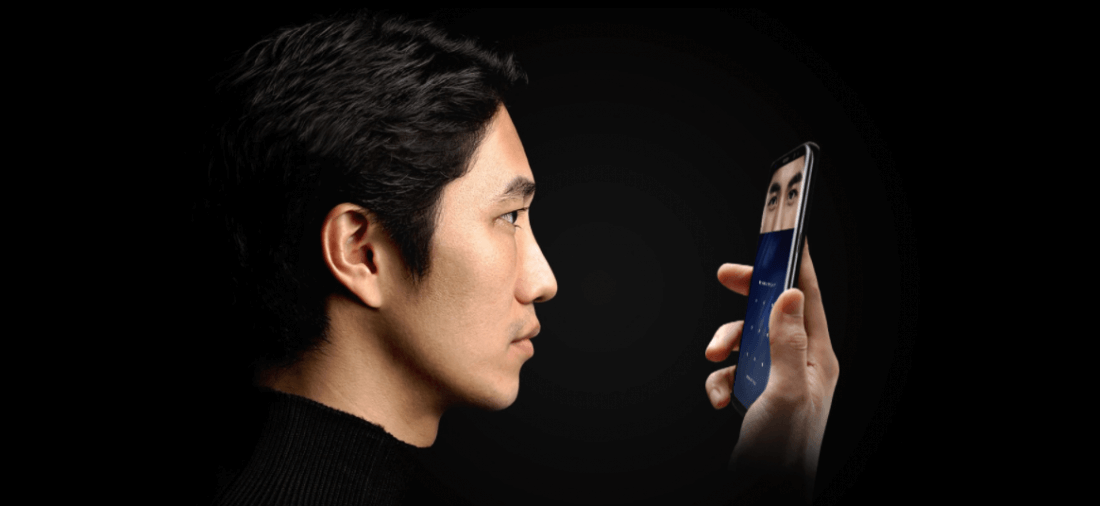
Samsung takes security very seriously. For the Galaxy S8 and S8+, the company wanted to ensure that the devices had top-notch security features. So they incorporated biometrics into the devices. The S8 line adds three biometric entry methods to the regular password, pin, and pattern locking methods. Now you can unlock the S8 using the fingerprint scanner, facial recognition, or an all new iris scanner.
The S8's facial recognition has already proven itself to be more of a novelty than a feature as it can be bypassed with a photograph. Researchers also discovered that facial recognition, in general, can be defeated with wacky printed glasses. However, you would think iris scanning would be more secure, right?
"The patterns in your irises are unique to you and are virtually impossible to replicate, meaning iris authentication is one of the safest ways to keep your phone locked and the contents private," says Samsung's promotional copy.
Of course, a statement like that is nothing more than an invitation to a challenge for hackers like Jan Krissler, who goes by the hacker handle Starbug. Krissler is the hacker who circumvented Apple's Touch ID only days after it was available to the public. According to Ars Technica, he also duplicated the fingerprints of Ursula von der Leyen, Germany's defense minister, using only photographs of her fingers.
Krissler was up to the task of trying to skirt Samsung's iris scanner, and he did it in typical Starbug fashion. First, he takes a picture of the victim's eyes. In his video demonstration (seen above), he used himself and had someone else take the picture. The photo does not even have to be a close-up. It can be taken from a medium distance away, so it does not even have to look like the person is the subject of the picture. The only condition is that the photo has to be an infrared image. Many inexpensive digital cameras have an IR mode, so this should not pose a problem to the dedicated infiltrator.
Next Krissler prints out a zoomed image of the eye on a laser printer. The printed image does not have to include the entire face, only the eye, but it has to be zoomed sufficiently to be life-sized. The size is important because once he has a printed image of the victim's eye, he places a contact lens over it to replicate the cornea of the eye.
Holding the picture with the contact lens attached to it up to the phone and aligning it with the circles opened his phone instantly. Granted, this in not the most straightforward solution, but it is simple enough that even a kid could pull it off.
The lesson here is to take Samsung's or any other company's promotional material regarding biometric security with a grain of salt. Any hacker creative and determined enough can find a way around these measures.