In brief: To most people, fax machines are an outdated piece of technology that's gone the way of the VHS tape, but there are around 46.3 million of them still being used around the world today---popularity that makes a recently discovered vulnerability all the more concerning.
Israeli cybersecurity firm Check Point presented a paper on the fax machine exploit, dubbed Faxploit, at the annual Defcon hacker event in Las Vegas yesterday. It found that all an attacker would need is a fax number, which is used to transmit an image---or a file that the machine believes to be an image---that's embedded with malicious code.
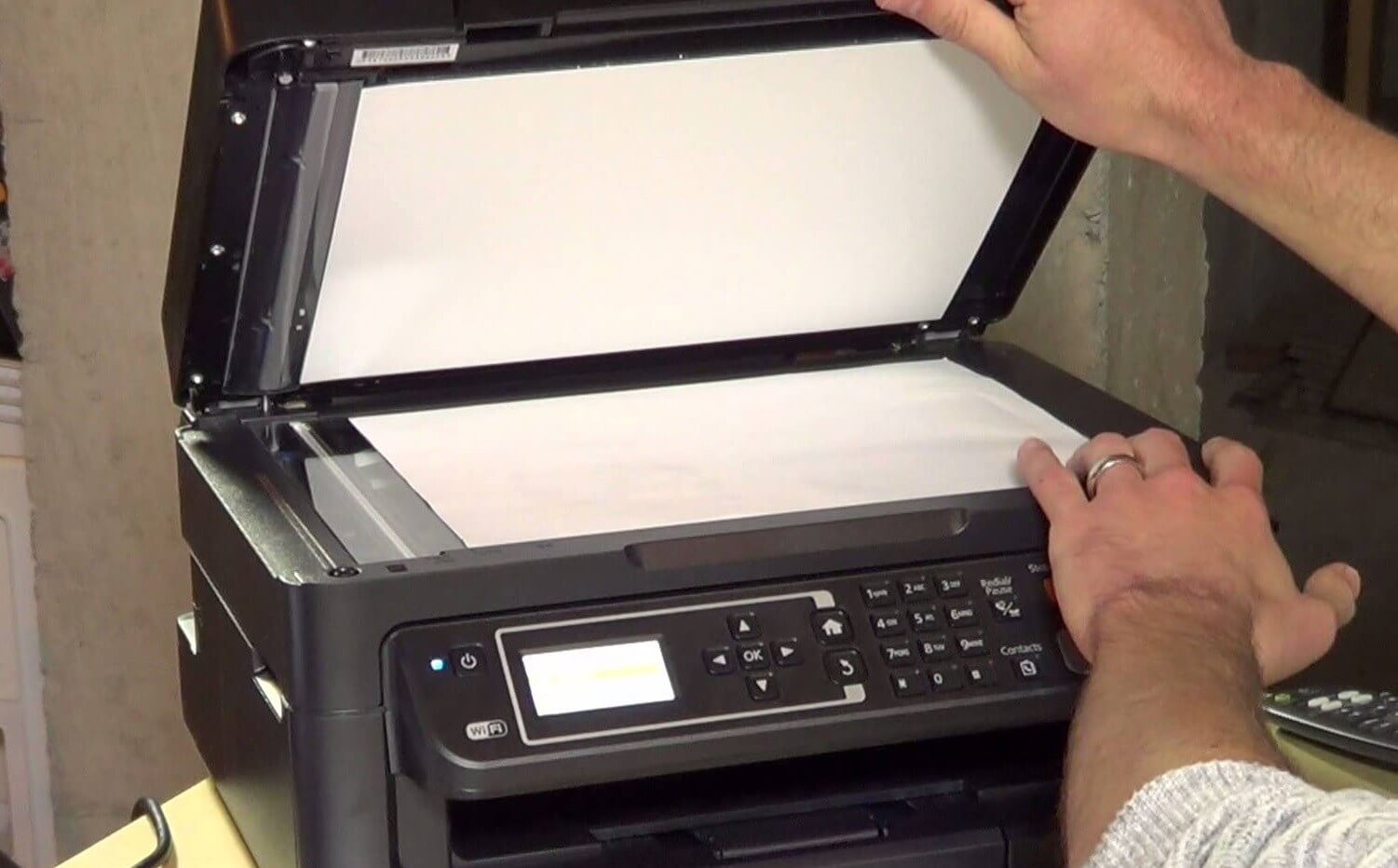
Check Point used an HP Officejet Pro all-in-one printer/fax machine to demonstrate the vulnerability, though HP issued a patch before the findings were revealed. But as the problem lies in the fax protocol, devices from other companies are likely to also be at risk.
Because most modern fax machines are all-in-one units connected to home or office networks, the malware payload sent by fax could potentially spread across an entire connected network. Moreover, the researchers said that as many of these units are so old and there are so few of them, some manufacturers feel they're not worth patching.
Check Point is advising companies to regularly check if there any firmware updates available for their all-in-one fax machines and apply them asap. It also recommends placing the fax devices on a separate, secure network, though this will likely be an inconvenience and limit their functionality.
"Once unauthorized access is gained, network segmentation can provide effective measures to mitigate the next stage of intrusion into a network and limit the spread of the attack by lateral movement across it," said Check Point.
Both the US and UK medical sectors rely heavily on communications via fax, and there are said to be 17 million fax machines still in operation in America.