What just happened? We know that malicious apps occasionally sneak their way onto the Play Store, but that's not the only place where Google's security is a bit lapse. The company has just removed 106 extensions from its Chrome Web Store for collecting sensitive user data.
A report from Awake Security identified 111 malicious Chrome extensions that had been downloaded almost 33 million times by May 2020---when the company contacted Google.
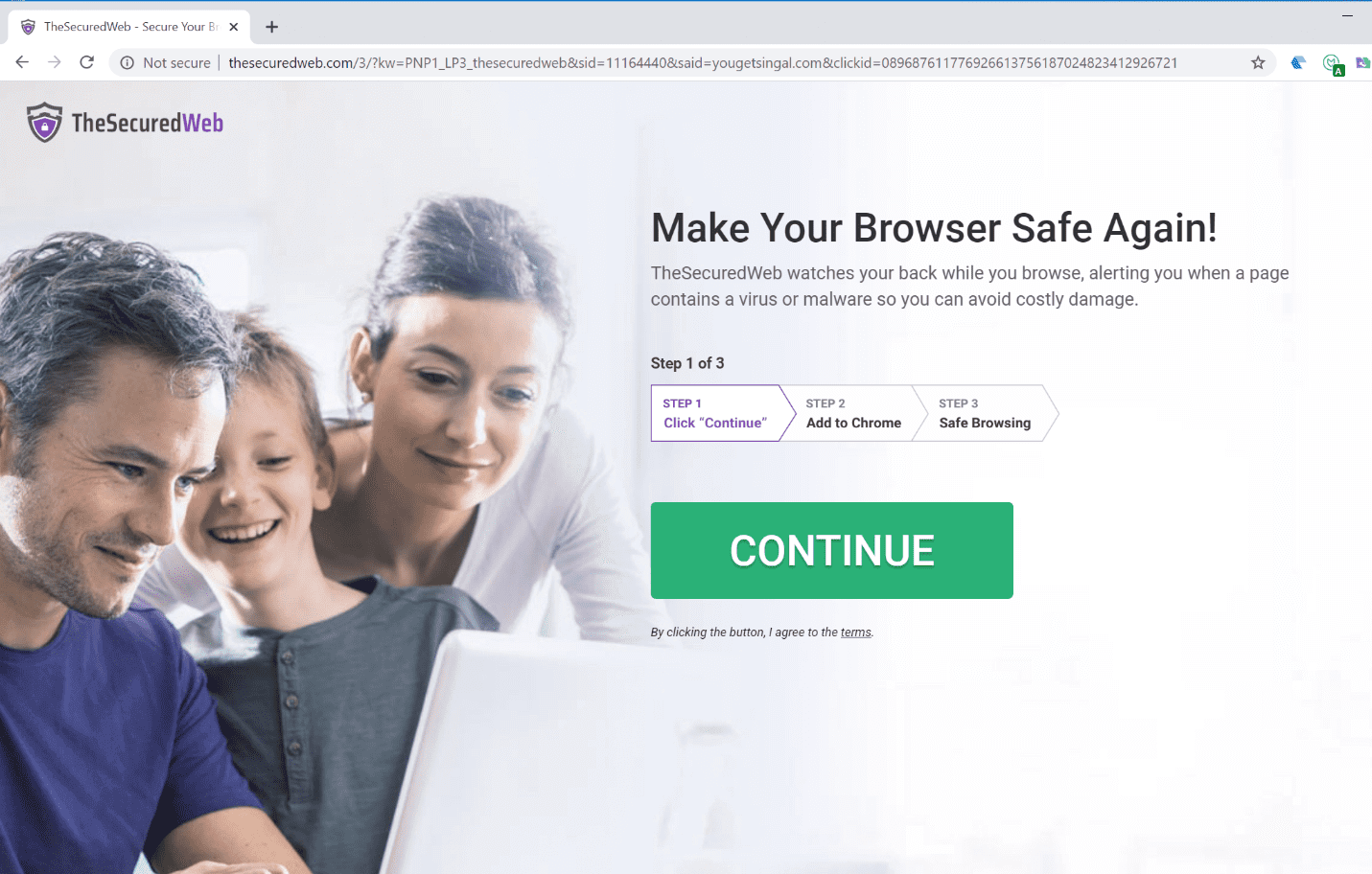
Most extensions purported to warn users about dangerous websites, improve web searches, and convert file formats. But their real primary function was to take screenshots, read the clipboard, gather browsing history, use keystrokes to steal passwords, and collect authentication cookies.
It's believed that all the extensions were the work of the same unidentified bad actor as many share almost identical graphics codebases, version numbers, and descriptions. According to Awake, the creator(s) gave Google false contact information when submitting the extensions to the Chrome Web Store.
The extensions were designed to avoid detection by antivirus/security software that evaluates the reputation of web domains. Researchers found that they would connect to a series of websites and transmit sensitive information. Those using Chrome on corporate networks, however, were safe as the extensions would not send the data or even connect to the malicious websites.
There were more than 15,000 malicious domains used, all of which were purchased from a small registrar in Israel called Galcomm.
"Galcomm is not involved, and not in complicity with any malicious activity whatsoever," Galcomm owner Moshe Fogel told Reuters. "You can say exactly the opposite, we cooperate with law enforcement and security bodies to prevent as much as we can."
Google has removed all but five of the malicious extensions from the Chrome Web Store. Those who installed them will find the extensions are still in their browsers, but have been disabled and marked as malware.