PSA: Apple has averaged about one zero-day vulnerability per month since January. The latest came with iOS 16, which hackers may have actively exploited over the last month. Apple issued iOS and iPadOS versions 16.1 and 16 earlier this week. Users with compatible devices should update them immediately.
On Monday, Apple released a patch for iOS 16 and iPadOS 16 to fix a critical vulnerability. The security weakness allows attackers to execute code with kernel-level privileges. An anonymous bug hunter reported it to Apple on October 11. Cupertino acknowledged that bad actors may have already exploited this zero-day flaw.
The vulnerability (CVE-2022-42827) could allow an app to commit an out-of-bounds write. This occurs when the software attempts to place data before or after the intended buffer. If the write is not checked, it creates a memory corruption that could result in a crash or open the OS up to arbitrary code execution.
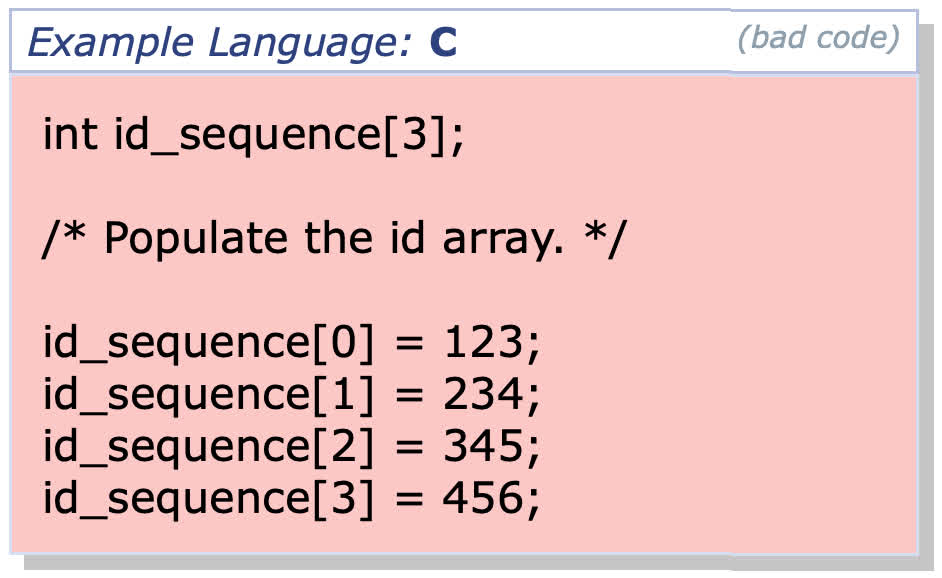
For instance, if a memory array is defined in the OS to have three elements, attempting to write to a fourth results in an out-of-bounds error. If the algorithm is not programmed to handle that exception, then a hacker can intentionally create the fault and exploit it to execute arbitrary code in a sensitive area of the operating system, like the kernel (example below).
Patch notes for iOS 16.1 and iPadOS 16 say the update repairs the flaw with "improved bounds checking." Impacted devices include the iPhone 8 and later, all iPad Pro models, third-generation iPad Air and later, and iPad and iPad mini models fifth-gen and later. Apple urges users to update as soon as possible.
Zero-day exploits are not that uncommon. By definition, they are security flaws that go public before the software vendor has a chance to discover and fix them on its own or with help from third-party researchers and bug bounty hunters. This one is Apple's eighth this year, according to Google researchers. Google itself has fixed seven zero-days, and Microsoft has had five since January.
The emergency patch contains 19 other security fixes, including two other kernel-level holes allowing code execution. Researchers discovered both and reported them to Apple before they could be exploited.