When I mentioned to a few friends that I was writing a feature about two-step authentication, the typical response was an eye-roll and "Oh, that annoying thing?..." Yes, that annoying extra step. We've all had that thought when we needed to get a code before we could log in or verify our identity online. Can I please just login without a barrage of requests?
However, after much research about two-factor authentication (often referred to as 2FA), I don't think I'll roll my eyes at it anymore. Let's get to know two-factor authentication a little better, the different options out there, and dispel some myths surrounding that "annoying" extra step.
Most Common Alternatives For Using 2FA
SMS Verification
It's commonplace for apps and secure services to suggest you add 2FA at least via SMS messages, for example when logging into your account – either at all times or just when doing so from a new device. Using this system, your cell phone is the second authentication method.
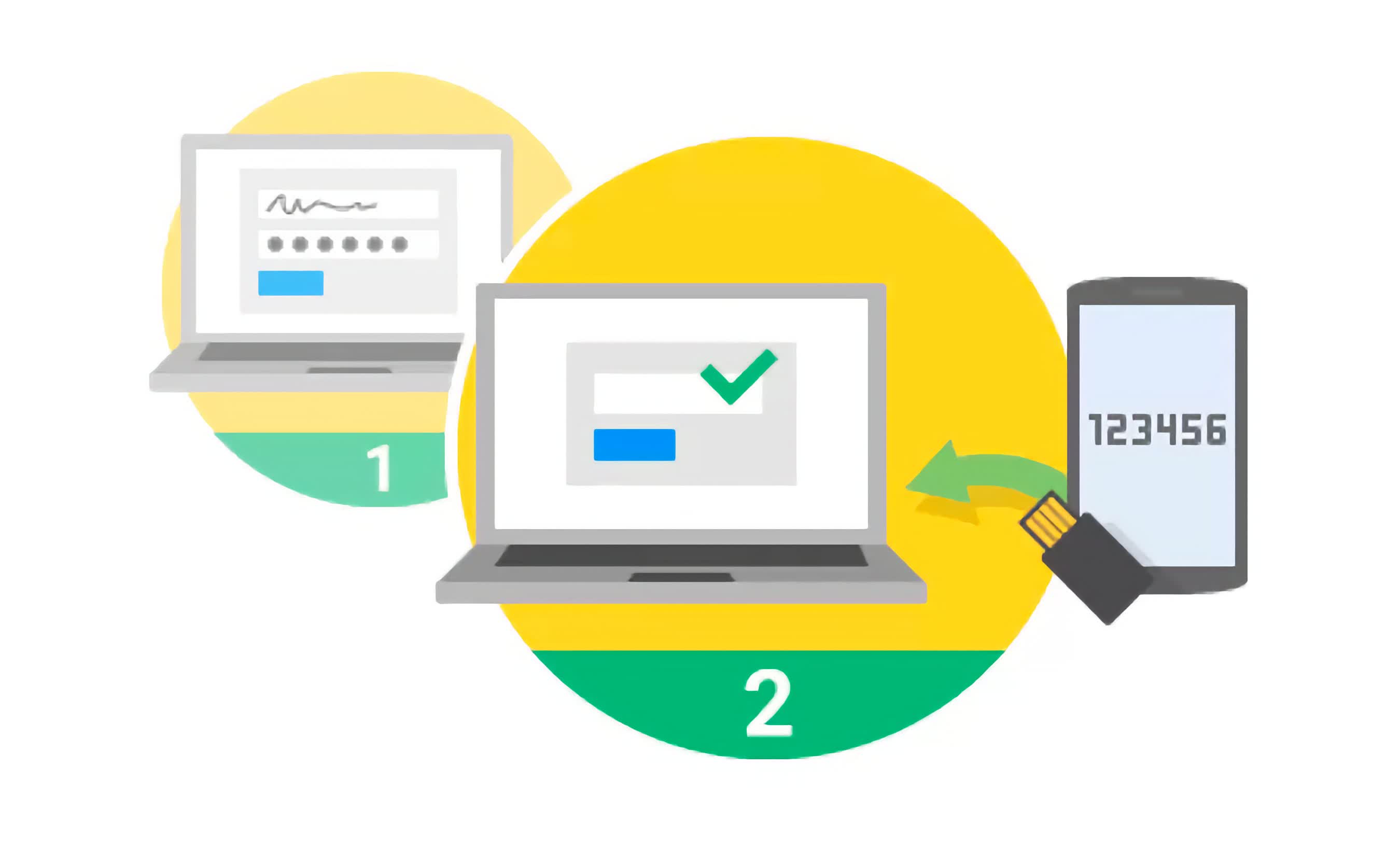
The SMS message consists of a short single-use code that you enter into the service. This way, Mr. Joe Hacker would need access to your password and your phone to get into your account. One rather obvious concern is cell coverage. What if you're stuck in the middle of nowhere without a signal, or traveling abroad without access to your common carrier? You won't be able to get the message with the code and won't be able to log in.
But most of the time, this method is convenient (we all have our phone handy most of the time). And there are even some services that have an automated system speak the code so that it can be used with a landline phone if you can't receive text messages.
Google Authenticator, Authy, App-Generated Codes
A potentially better alternative to SMS, because it doesn't rely on your wireless carrier. Google Authenticator is the most popular app in its category, but if you don't want to rely on Google for this kind service, there are comprehensive alternatives like Authy, which offers encrypted backups of the codes generated over time, as well as multi-platform and offline support. Microsoft and Lastpass also have their own authenticators as well.
These apps will keep generating time-specific codes till kingdom come, with or without an internet connection. The only tradeoff is that setting the app setup is slightly complicated.

After setting up a given service with Authenticator, you'll be prompted to enter an authentication code in addition to your username and password. You'll rely on the Google Authenticator app on your smartphone to provide you with a fresh code. The codes expire within the minute, so sometimes you'll have to work fast to enter the current code before it expires and then the new code is the one to use.
Physical Authentication Keys
If dealing with codes and apps and text messages sounds like a headache, there's another option that is on the brink of popularity: Physical authentication keys. It's a small USB device you put on your keychain – like the security key pictured below. When logging into your account on a new computer, insert the USB key and press its button. Done and done.

There's a standard around this called the U2F. Google, Dropbox, GitHub accounts and many others are compatible with the U2F token. Physical authentication keys can work with NFC and Bluetooth to communicate with devices that don't have USB ports as well.
App-Based and Email-Based Authentication
Many apps and services skip the above options altogether and verify through their mobile apps. For example, enable "Login verification" on Twitter and when you log into Twitter for the first time from a new device, you must verify that login from the logged in app on your phone. Twitter wants to make sure that you, not Mr. Joe Hacker, has your phone before you log in.
Similarly, Google accounts offer something similar when logging in a new PC, it asks you to open Gmail on your phone. Apple also uses iOS to verify new device logins. When logging in on a new device, you'll get a one-time-use code sent to an Apple device you already use.
Email-based systems, as you probably figured out from the description, uses your email account as the second-factor authentication. When logging into an app or service that uses this option, the one-time-use code will be sent to your registered email address for additional verification.
Myths / FAQ
What are common services where enabling 2FA is recommended?
- Google / Gmail, Hotmail / Outlook, Yahoo Mail **
- Lastpass, 1Password, Keepass, or any other password manager you use **
- Dropbox, iCloud, OneDrive, Google Drive (and other cloud services where you host valuable data)
- Banking, PayPal, and other financial services you use that support it
- Facebook / Twitter / LinkedIn
- Steam (in case your game library happens to be worth more than your average bank account balance)
** These are particularly important because usually serve as a gateway to everything else you do online.
If there's a security breach, turn on two-factor authentication ASAP?
The problem is that you can't just flip a switch and turn on 2FA. Starting 2FA means tokens have to be issued, or cryptographic keys must be embedded in other devices. In case of a service breach, we recommend you to change your passwords first, then enable 2FA. Best practices still apply, like using hard-to-guess passwords and not reusing your password in different services/websites.
Should I enable two factor authentication or not?
Yes. Especially for critical services that contain your personal data and financial information.
Two-factor authentication is impervious to threats
No. 2FA depends on both, technologies and users that are flawed, so it is also flawed. A 2FA that uses SMS text as the second factor relies on the security of the wireless carrier. It's also happened where malware on a phone intercepts and sends SMS messages to the attacker. Another way that 2FA can go wrong is when a user isn't paying attention and approves a request for authentication (maybe it's a pop-up message on their Mac) that was started by an attacker's attempt to log in.
How 2FA can fail in case of a successful phishing attempt?
Two-factor authentication can fail in a phishing attack if the attacker tricks the user into entering their 2FA code on a fake page. The attacker then has access to both the user's login credentials and 2FA code, bypassing the security of 2FA. To prevent this, it's important for users to be aware of phishing attempts and to verify the authenticity of login and 2FA pages before entering information.
Two-factor solutions are (basically) all the same
This may have been true at some point, but there's been much innovation to 2FA. There are 2FA solutions using SMS messages or emails. Other solutions use a mobile app that contains a cryptographic secret or keying information stored in a user's browser. Reliance on third-party services is something to think about, and should be improved upon, as it has been breached and the authentication has failed in some instances.
Two-factor authentication is an annoying extra with little benefit
Well, with that kind of attitude we'll never get anywhere. In reality, some businesses or services approach 2FA as a compliance requirement, instead of something that can help reduce fraud. Some companies use the minimum required 2FA that barely does anything, just to check off the 2FA box. As a user, it can be annoying to use 2FA, but if the company is using a flexible authentication method (not just the bare minimum) it can reduce the possibility of fraud. And who doesn't want that?
