In context: Researchers continue to find ways to abuse and exploit speculative execution on modern CPUs. The newest vulnerability has been named "Spoiler," and while it'll likely be a thorn in Intel's side for some time to come with no viable solution, AMD's processors are unaffected claims the CPU maker.
Researchers at Worcester Polytechnic Institute in the US, and the University of Lübeck in Germany, recently discovered another speculative execution vulnerability impacting Intel processors. Dubbed "Spoiler," and like Spectre before it, the flaw preys upon the CPU's speculative execution engine that presciently guesses upcoming computations to boost performance.
As the research paper explains, Spoiler is entirely independent from Spectre, so existing mitigations for Spectre and Meltdown have no effect on the new flaw. Spoiler is a complicated problem, but the paper offers a summary of sorts.
We have discovered a novel microarchitectural leakage which reveals critical information about physical page mappings to user space processes. The leakage can be exploited by a limited set of instructions, which is visible in all Intel generations starting from the 1st generation of Intel Core processors, independent of the OS and also works from within virtual machines and sandboxed environments.
The researchers also tested AMD and ARM-based processors, but found that they were not susceptible in the same way Intel's processors are. This makes Spoiler a problem unique to Intel, and it's already found itself reeling after the frenzy that was Spectre and Meltdown. And just like those two flaws, there's no viable software-only mitigation; microarchitecure level changes could help, but it'd come at the cost of performance.
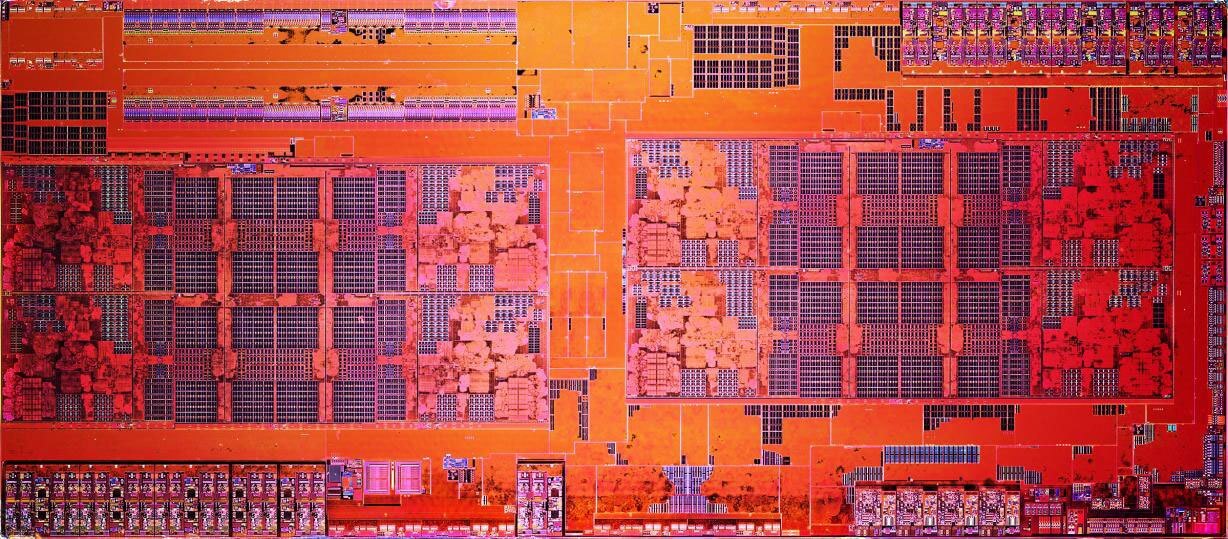
No doubt relieved, AMD has confirmed Spoiler does not impact Ryzen processors.
We are aware of the report of a new security exploit called SPOILER which can gain access to partial address information during load operations. We believe that our products are not susceptible to this issue because of our unique processor architecture. The SPOILER exploit can gain access to partial address information above address bit 11 during load operations. We believe that our products are not susceptible to this issue because AMD processors do not use partial address matches above address bit 11 when resolving load conflicts.
While AMD did have to issue some mitigations for Spectre, they seem to have dodged a bullet here. The same can't be said for Intel, unfortunately, who will have to continue to analyze their CPU design at the silicon level for improved security in the future.
https://www.techspot.com/news/79234-amd-addresses-spoiler-vulnerability-ryzen-users-safe-one.html