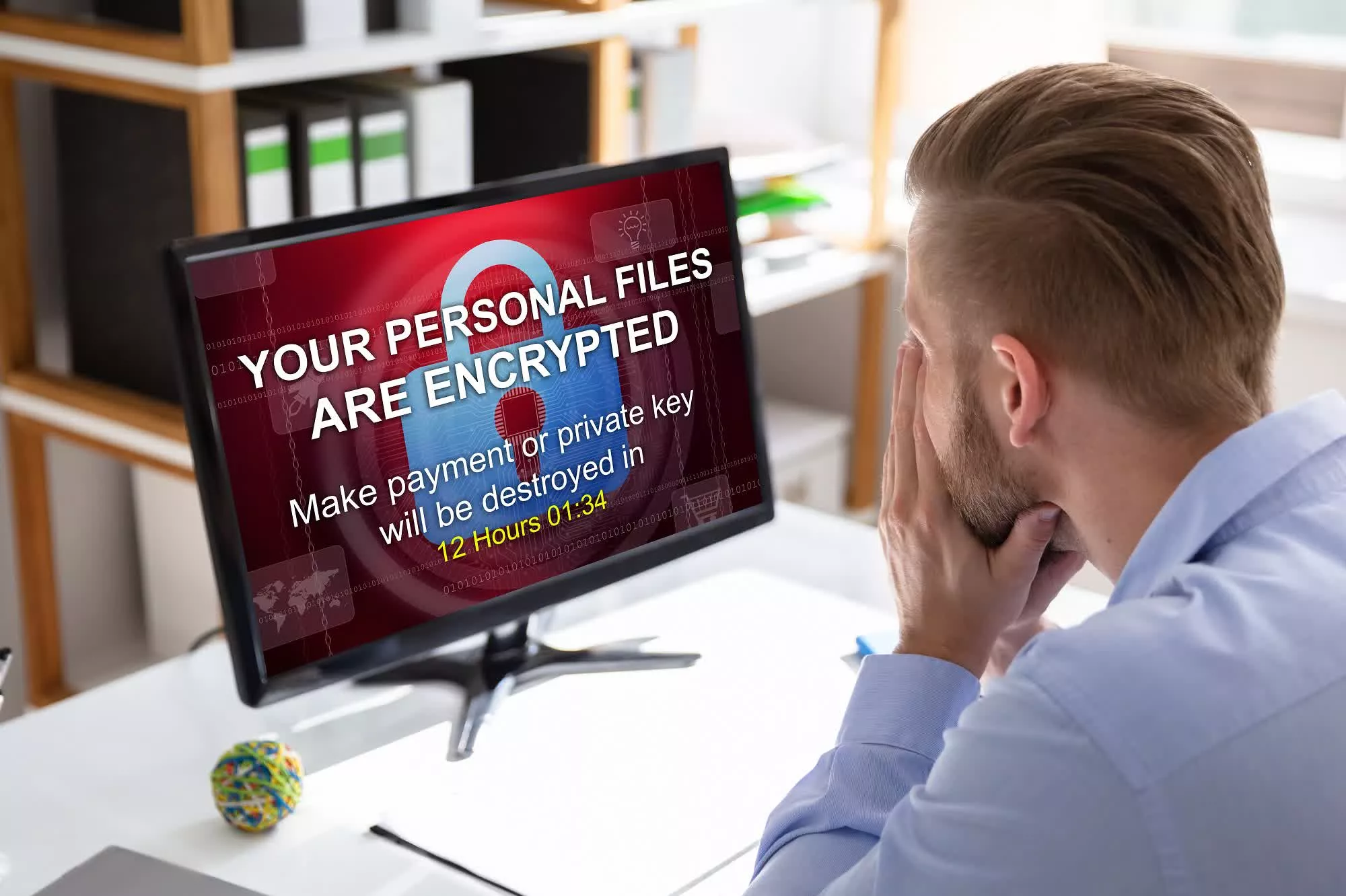
A hot potato: Authorities tend always to tell victims of cyberattacks not to pay the cybercriminals the ransom money as doing so is often fruitless, but it's sometimes the only option. In Australia, the government hopes to stop the practice and, in the process, discourage ransomware incidents by making these payments illegal.
Australia has recently been hit with two of the largest data breaches in history. First was the hack on telecom giant Optus that saw the personal information of nearly 2.1 million customers leaked, then came the attack on private health insurance provider Medibank that compromised the records of 9.7 million current and former customers.
The REvil-linked Russian hackers behind the Medibank attack have already released the records of more than one million people. They are threatening to release more unless they receive a ransom payment, which Medibank refuses to pay.
The incidents have led the Australian government to consider making ransom payments by cybercrime victims illegal. Australia's home affairs minister and Minister for Cybersecurity, Clare O'Neil, confirmed that the plans were part of a wider cyber strategy that includes 100 officers becoming part of a new joint standing operation against cybercrime.
I have a message for all cybercriminals: Australia is fighting back.#Insiders pic.twitter.com/jEyk6rzgGj
— Clare O'Neil MP (@ClareONeilMP) November 13, 2022
Criminalizing the payment of ransoms to cyberattackers would likely see incidents decrease, but another expected result would be organizations failing to declare attacks and paying hackers secretly. Ransomware can encrypt every system in a business, so when owners face potential bankruptcy or breaking the law, some might decide that quietly paying the money is a better option.
The US has also considered banning all ransomware payments. The FBI advised congress not to take this action as it would lead to further extortion opportunities for criminals—I.e., threatening to report an organization for paying the ransom/not disclosing a hack.
Not revealing hacking incidents to the authorities, often due to the negative publicity they bring, is not a new phenomenon. Last month, Joe Sullivan, Uber's former chief security officer, was found guilty of charges relating to concealing a 2016 hack on the ride-hailing giant. He was charged with obstructing justice for not revealing the breach to the FTC. He was also found guilty of actively hiding a felony, or misprision.
Masthead: Andrey_Popov
https://www.techspot.com/news/96669-australia-wants-criminalize-ransomware-payments.html