Ransomware is bad enough in its current form, but a new variant of the malware has been discovered that is possibly worse than what we've seen before. The malicious software, called Petya, doesn’t just target individual files, it encrypts entire hard drives.
While the majority of ransomware is spread via email attachments or is hosted in sites and delivered by exploit kits, Petya has been found in emails containing hyperlinks to a Dropbox storage location (since removed by the company), making it appear more legitimate.
According to a Trend Micro blog post, the email masquerades as an application letter from someone seeking employment in a company. One of the links supposedly points at the applicant's CV, but is actually a self-extracting executable file. This link downloads a Trojan which blinds any antivirus programs before downloading and executing Petya.
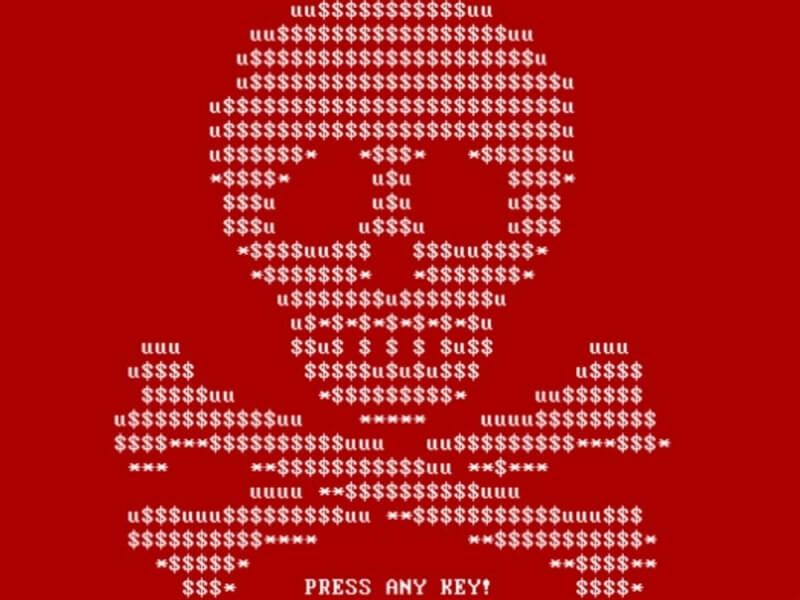
Once executed, Petya will overwrite the master boot record of the entire hard drive, triggering a critical Windows error – the dreaded Blue Screen of Death. When the machine is rebooted, the PC appears to perform a check disk operation but, during this time, Petya is actually encrypting the master file table (MFT), rendering the PC useless.
At this point, victims are presented with a lock screen and instructions on how to connect to TOR, visit a specific website and pay the fee, which is 0.99 bitcoins, or around $430. If the ransom is not paid within seven days the price doubles.
The attackers, who call themselves 'Janus Cybercrime Solutions,' say that attempting to fix the master boot record won’t decrypt the ransomware, and may result in the purchased decryption key not working.
So far, emails containing the Petya links have been aimed primarily at companies in Germany, but they could start reaching beyond the country’s borders. Researchers are still investigating this new form of ransomware, but there's still no fix available.
https://www.techspot.com/news/64271-new-form-ransomware-uses-disk-level-encryption-lock.html