Kali Linux is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering.
Because Kali Linux is multi-platform, it gives you a strong, stable, known baseline to operate from regardless of where you use it: desktops, servers, virtual machines, live environments, cloud or containers.
Why is Kali Linux popular among hackers and IT security professionals?
Kali Linux is widely used in the cybersecurity community due to its focus on penetration testing, digital forensics, reverse engineering, and security research. It comes pre-installed with hundreds of tools tailored for ethical hacking. Its mainstream visibility was boosted by popular media like the TV series Mr. Robot, but its utility, reliability, and backing by Offensive Security are what make it a standard in the field.
How many tools does Kali Linux include?
Kali Linux includes over 600 pre-installed tools used for various aspects of cybersecurity. These tools cover everything from network scanning and traffic analysis to password cracking and web application testing. Some of the most well-known tools in Kali Linux are nmap for port scanning, Wireshark for packet analysis, John the Ripper for password cracking, Aircrack-ng for wireless network testing, and Burp Suite and OWASP ZAP for web application security assessments.
How secure is Kali Linux?
Kali Linux is developed with a strong emphasis on security and integrity. Only a small group of trusted developers can commit packages, and each package is signed to ensure authenticity. The distribution also uses a custom kernel that is patched for features such as packet injection, which is essential for wireless network assessments.
Is Kali Linux portable?
Kali Linux is highly portable. It can be installed directly onto a hard drive for regular use, or it can be run in live mode from a USB or CD without installation. It also supports virtualized environments such as VirtualBox and VMware, allowing users to run it within other operating systems. In addition, Kali Linux can be used on Arm-based devices like the Raspberry Pi, through the Windows Subsystem for Linux (WSL), or in cloud environments such as AWS and Azure.
What Linux distribution is Kali Linux based on?
Kali Linux is based on Debian Testing. This foundation gives Kali Linux a stable and widely supported base while allowing it to include newer tools and packages optimized for security research.
What version of Kali Linux should I download?
If you have a 64-bit system and want to install Kali permanently, the standard 64-bit ISO is recommended. For temporary use or testing, the live version allows you to run Kali without installation.
Virtual machine images are ideal for users who prefer to run Kali in a controlled environment, and Arm images are available for devices like the Raspberry Pi. For Android-based penetration testing, Kali NetHunter is the appropriate version. If you're using Windows 10 or 11, Kali Linux can also run through the Windows Subsystem for Linux.
Can I use Kali Linux as my daily OS?
While technically possible, using Kali Linux as a daily driver is generally discouraged. Kali is optimized for security testing, not for general-purpose computing. It may lack certain conveniences and stability found in mainstream distributions, and using it for everyday tasks could pose security risks if not properly managed.
What's New
Kali Linux 2026.1 Release (2026 Theme & BackTrack Mode)
New year, new release - Kali 2026.1 is here! There is everything from a fresh coat of paint to a nod to our roots, with normal ongoing improvements. Building on from December's 2025.4, the summary of the changelog:
- 2026 Theme Refresh - Our yearly theme refresh
- BackTrack Mode For Kali-Undercover - New mode celebrating BackTrack's 20th anniversary
- Kali's 13th Birthday Event - A little community event
- New Tools - 8 new programs
2026 Theme Refresh
As with previous 20xx.1 releases, this major update brings our annual theme refresh, a long-standing tradition that keeps the Kali Linux interface as modern and innovative. This year's release unveils a brand-new theme from the moment you boot. Everything from the boot menu, installer to the login display, and a fresh set of desktop wallpapers.
Boot Animation
The changes to the boot animation are subtle, but now the animation is fixed for live images, where it used to get stuck at the beginning, showing only the tail. It will also restart the loop in case the boot process takes longer, making it look smoother.
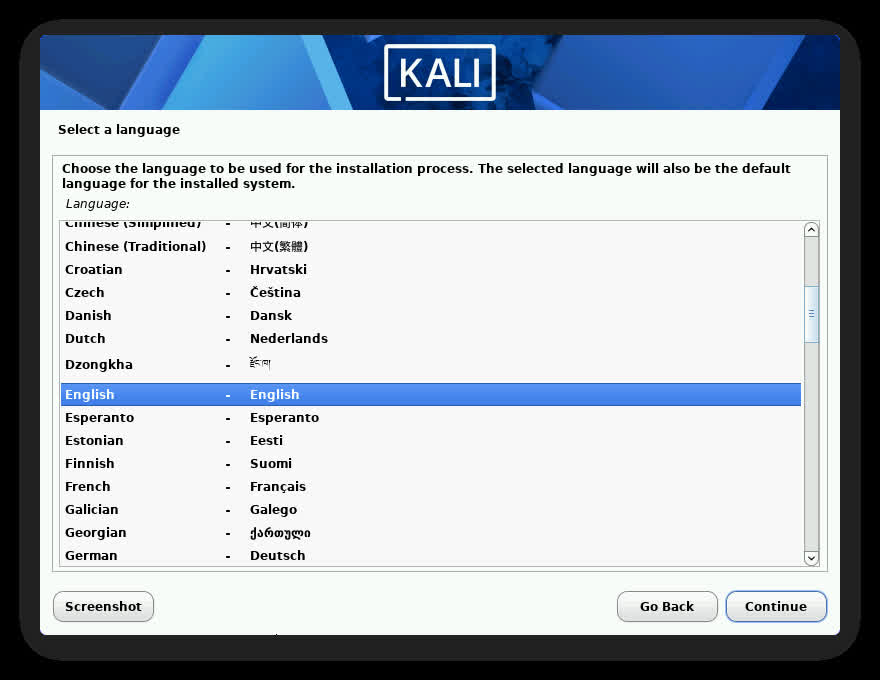
Graphical Installer
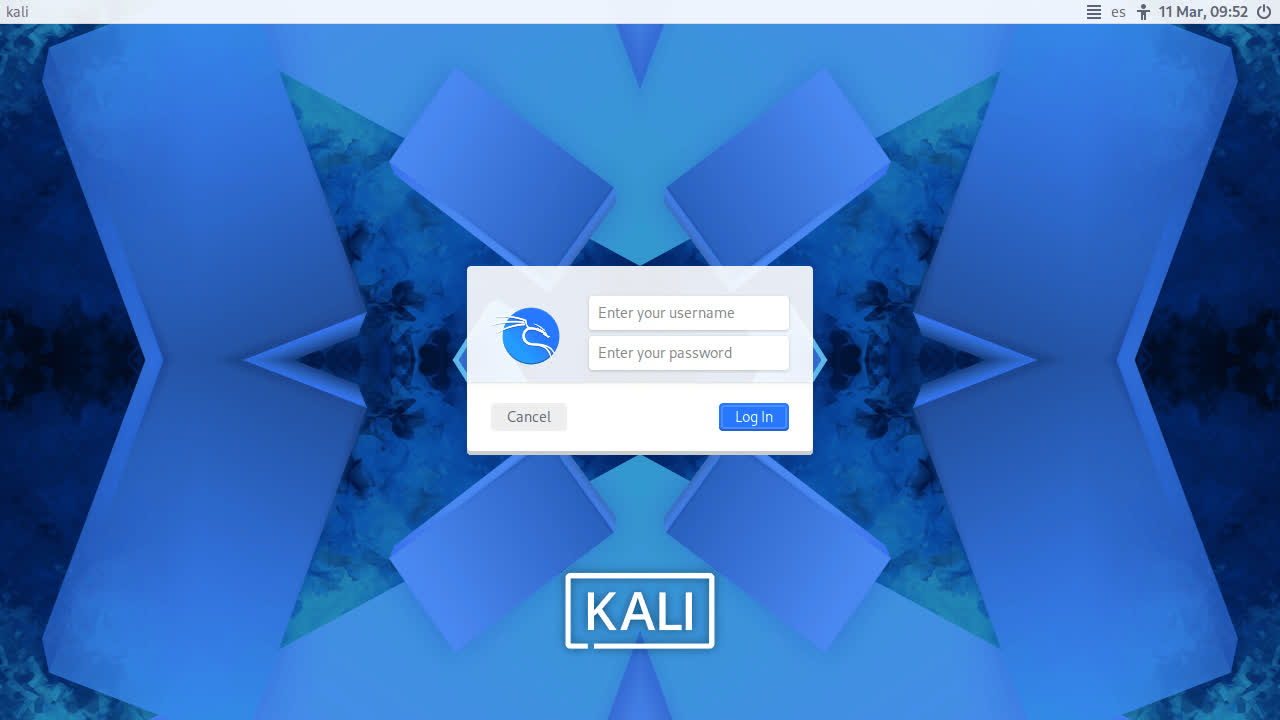
Login
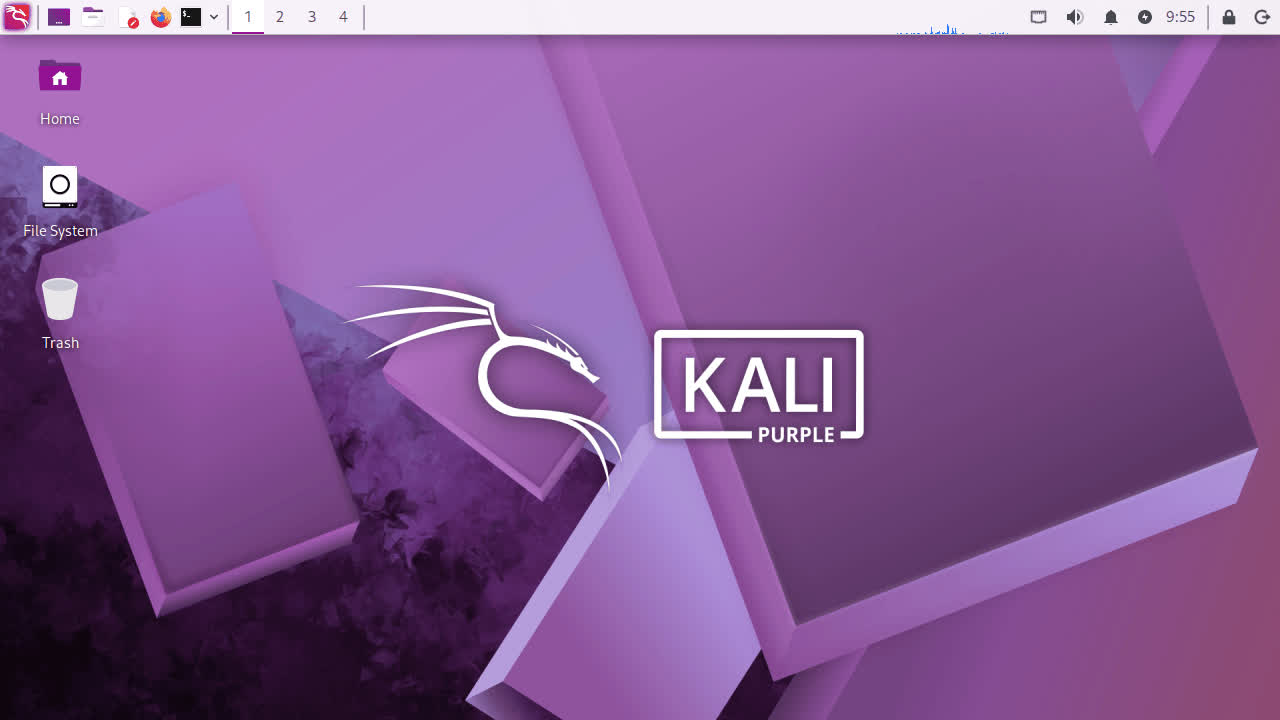
Desktop
Kali Purple Desktop
New Wallpapers
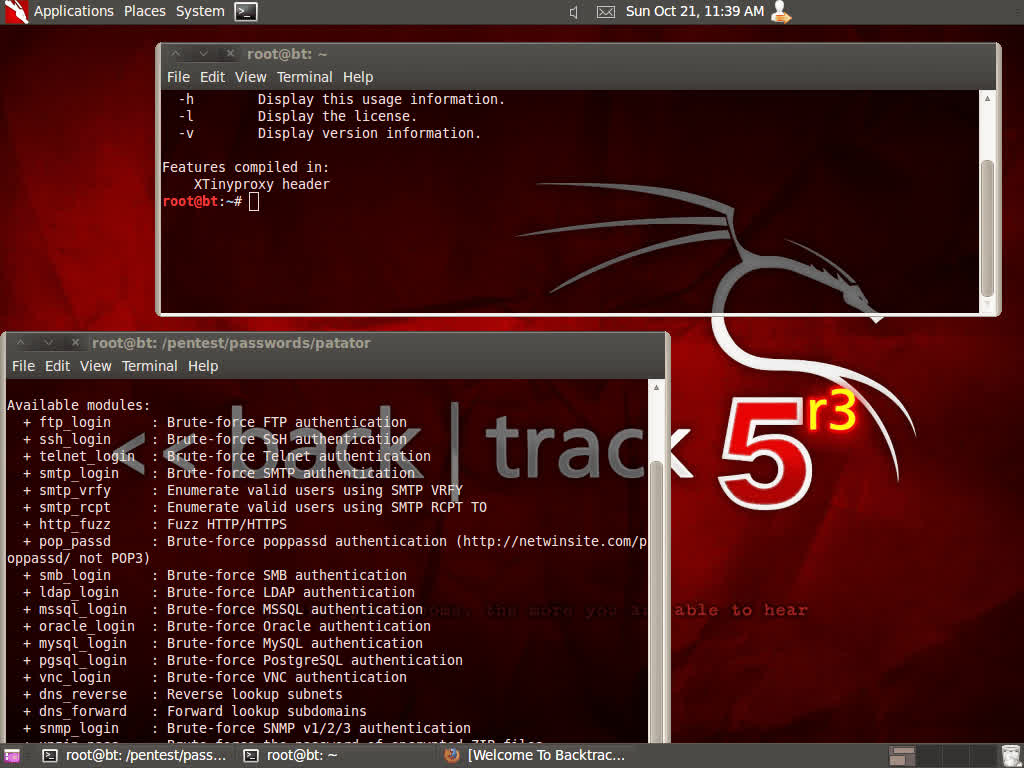
BackTrack Mode For Kali-Undercover
2026 marks the 20th anniversary of BackTrack Linux, the predecessor to Kali. To celebrate this milestone, we wanted to bring back some nostalgia for longtime users of this legendary cybersecurity distribution by adding a "BackTrack mode" to kali-undercover. This mode transforms the desktop to recreate the look and feel of BackTrack 5, with the same wallpaper, colors, and window themes.
You can run it directly from the menu or by running kali-undercover --backtrack in the terminal. You can switch back to the default Kali desktop (or not) by running it again.
Here is a screenshot of BackTrack 5, so you can compare it with our theme:
New Tools in Kali
It would not be a Kali release without some new tools! Here is a quick rundown of the 8 new tools which have been added (to the network repositories):
- AdaptixC2 - Extensible post-exploitation and adversarial emulation framework
- Atomic-Operator - Execute Atomic Red Team tests across multiple operating system environments
- Fluxion - Security auditing and social-engineering research tool
- GEF - Modern experience for GDB with advanced debugging capabilities
- MetasploitMCP - MCP server for Metasploit
- SSTImap - Automatic SSTI detection tool with interactive interface
- WPProbe - Fast WordPress plugin enumeration tool
- XSStrike - Advanced XSS scanner
There have been a total of 25 new packages, 9 removed, and 183 updates. On top of that, we also bump the Kali kernel to 6.18.