McAfee issued a report today detailing what is at minimum a five-year, sustained, global hacking campaign launched against more than 72 high value targets. Known as "Operation: Shady RAT", the long-term cyber intrusions are said to have involved classified government networks, public agencies, multi-national companies and even, ironically, computer security firms.
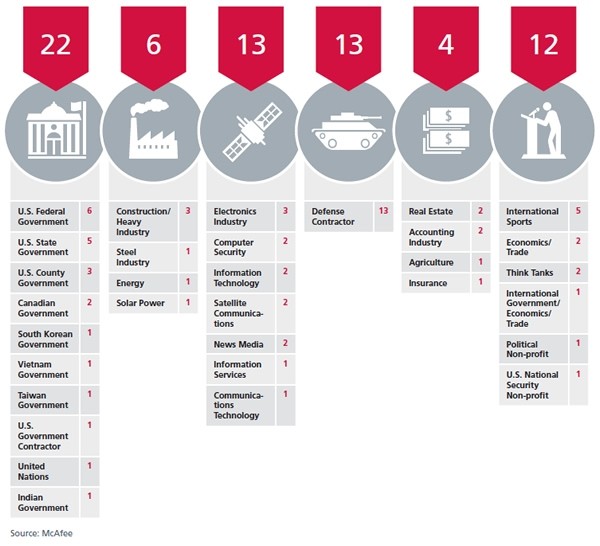
McAfee refrains from being too specific about the victims, but they do identify a handful of targets, including the Department of Energy, the United Nations and the World Anti-Doping Agency in Canada. Overall, 72 identifiable entities were infiltrated, however many other unidentified targets still remained. More specifically, 22 government agencies were compromised in addition to six industrial companies, 13 technology companies, 13 defense contractors, six financial firms and 12 organizations.
"McAfee has gained access to one specific Command & Control server used by the intruders. We have collected logs that reveal the full extent of the victim population since mid-2006 when the log collection began. Note that the actual intrusion activity may have begun well before that time but that is the earliest evidence we have for the start of the compromises. The compromises themselves were standard procedure for these types of targeted intrusions: a spear-phishing email containing an exploit is sent to an individual with the right level of access at the company, and the exploit when opened on an unpatched system will trigger a download of the implant malware."
"... After painstaking analysis of the logs, even we were surprised by the enormous diversity of the victim organizations and were taken aback by the audacity of the perpetrators. Although we will refrain from explicitly identifying most of the victims, describing only their general industry, we feel that naming names is warranted in certain cases, not with the goal of attracting attention to a specific victim organization, but to reinforce the fact that virtually everyone is falling prey to these intrusions, regardless of whether they are the United Nations, a multinational Fortune 100 company, a small non-profit think-tank, a national Olympic team, or even an unfortunate computer security firm."
Source: Dmitri Alperovitch, VP of Threat Research at McAfee

The report includes illuminating details regarding the duration and geographical location of cyber attack victims, many of which were compromised for several months or more. A handful of those organizations were victimized for less than one month, however for one Asian Olympic committee, the infiltration lasted for more than two years.
Over the span of five years, the barrage of intrusions are said to have transferred over a petabyte of data. Alperovitch suggests that such a wealth of information may likely include company trade secrets and classified information which unscrupulous competitors or organizations may be using to their advantage. However, the author then goes on to hypothesize that perpetrators may not have solely been motivated by profit, given the broad diversity of targets and the inclusion of non-profit organizations.
Alperovitch said he was also intrigued by the idea of comparing the dates of intrusions against geo-political events. Based up the available puzzle pieces, some reports have already speculated that individuals in China may indeed be the culprits.