Less than one week removed from the Flashback Trojan, there are reports of yet another Mac Trojan that is making the rounds. Backdoor.OSX.SabPub.a is designed to steal information from infected systems and uses an exploit in Java that allows it to remain untraced by malware detection products. The Trojan is said to connect to a command and control server based in California.
Costin Raiu from Kaspersky Labs explains that the Trojan is apparently distributed through Microsoft Word documents and is being spread through e-mails that direct users to specific URLs hosted in the US and Germany. The vulnerability is known as CVE-2009-0563.
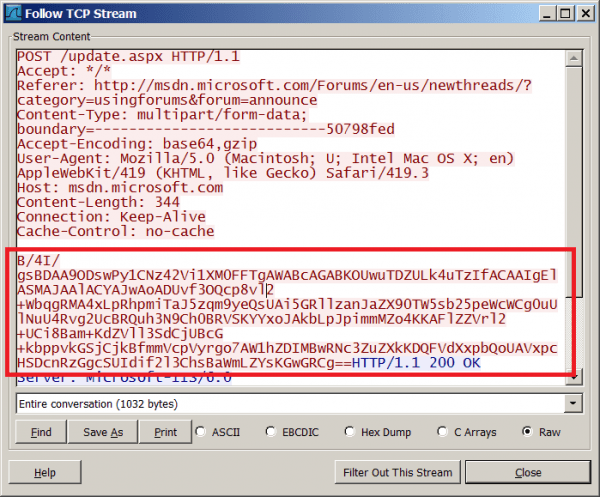
Raiu noted in his post on Securelist that that he set up a fake victim machine which was hit on April 15. Based on the team's analysis of the attack, they are pretty confident that the operation of the bot was done manually, meaning a real person was on the other end going through the system's files and even stealing some "goat" documents.
Furthermore, similarities to another Trojan called LuckyCat suggest that Backdoor.OSX.SabPub.a could be targeting Tibetan activists. One of the Word documents is related to an announcement by the Deli Lama.
Over 600,000 Macs were infected with the Flashback Trojan last week with 56.6 percent of the infections originating in the US. Victims were infected simply by visiting a webpage that loaded the malicious script. Apple eventually released an update to patch the Java vulnerabilities that led to infection.