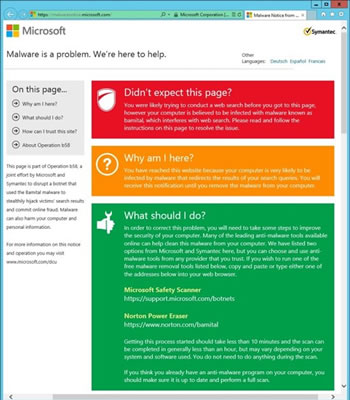
In partnership with Symantec, Microsoft has disrupted yet another botnet, marking its sixth takedown in the three years since starting Project MARS (Microsoft Active Response for Security). Called "Bamital," the malware network has evolved into several variations since Symantec began tracking it in 2009.
It largely spread through drive-by-downloads as well as infected files on P2P networks and it targeted users with click fraud schemes along with hijacking search engines by Microsoft, Yahoo and Google.
Research gathered by Microsoft and Symantec shows that Bamital has attacked more than eight million computers over the last two years. During a six-week period in 2011, investigators watched the activity of a single Bamital command and control server, which communicated with over 1.8 million unique IP addresses and resulted in three million clicks being hijacked every day.
It remains unclear precisely how much profit the operation generated, but a conservative estimate says at least $1 million a year.
As with previous takedowns, Microsoft and its partners disabled Bamital by suing to cut communication between the botnet's servers and the infected systems it controlled. That suit was filed on January 31 and by February 6, Microsoft and US Marshals were rolling into web-hosting facilities in Virginia and New Jersey to seize evidence. It's believed that the botnet originated in Russia or Ukraine and last week's filing identifies 18 "John Doe" ringleaders across the US, Russia, Romania, Britain and Australia.