Another day, another drive-by cryptomining report. Following yesterday's news that over 4200 websites were found to contain Monero-mining malware, Malwarebytes has discovered what is thought to be the first large-scale campaign targeting mobile users.
Researchers from the security firm spotted the campaign in January but believe it began in November last year. It works by directing Android users to malicious websites set up for the sole purpose of using the processors in visitors' phone to mine Monero cryptocurrency. While some people may be redirected through regular browsing via malvertising, it's thought that infected apps with malicious ad modules are the main culprit.
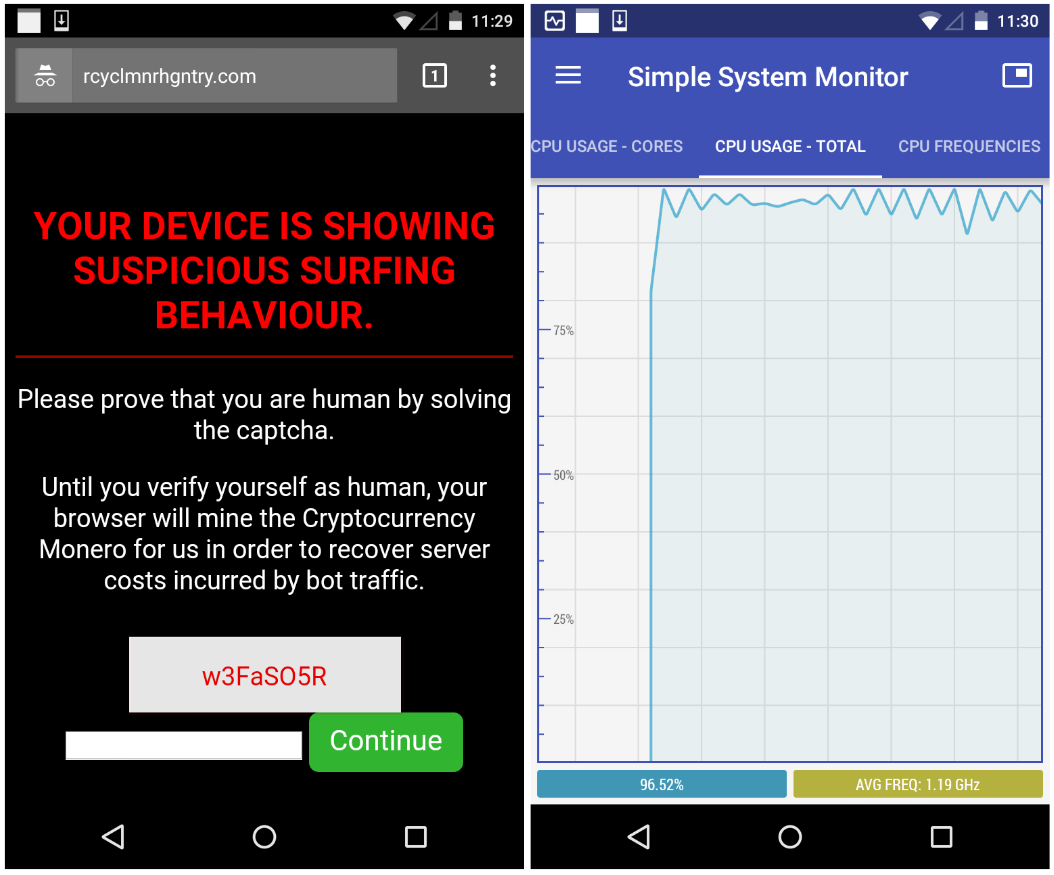
Unlike most other drive-by cryptomining sites, visitors to these pages are informed of the process. A message claims the mining is needed to pay for server costs incurred by bot traffic, and visitors must prove they are human by solving a captcha. Once they enter the code, the mining ends and users are redirected to the Google home page.
"Your device is showing suspicious surfing behavior. Please prove that you are human by solving the captcha. Until you verify yourself as human, your browser will mine the Cryptocurrency Monero for us in order to recover the server costs incurred by bot traffic," states the warning.
Malwarebytes identified five internet domains using the same captcha code but with different Coinhive site keys. Traffic analysis suggests most visitors spend around four minutes on the sites. But even though the combined domains had around 80,000 visitors per day and at least two of them had over 30 million visits per month, the company thinks the campaign isn't making a huge amount of money---at least not yet.
"It is difficult to determine how much Monero currency this operation is currently yielding without knowing how many other domains (and therefore total traffic) are out there. Because of the low hash rate and the limited time spent mining, we estimate this scheme is probably only netting a few thousand dollars each month," wrote Jerome Segura, lead malware intelligence analyst at Malwarebytes.
"However, as cryptocurrencies continue to gain value, this amount could easily be multiplied a few times over."
Malwarebytes recommends Android users increase their chances of avoiding the campaign, which is still active, by not downloading apps from outside the Play store and using web filters and security software.
Back in December, it was reported that a newly discovered piece of Android malware mines Monero so intensely that it can cause physical damage to a phone.
