Intel has been the source of quite a bit of controversy lately following the discovery of two major security flaws within their processors. For the unaware, these flaws, dubbed Meltdown and Spectre, allow hackers to take advantage of "speculative execution" to swipe personal data from a victim's machine.
Though these flaws exist within AMD's processors as well, Intel's chips have been the most vulnerable. As such, Intel has been working closely with other tech companies to roll out software patches for known Meltdown and Spectre variants. The patches released so far have been effective but they've also come at the cost of system performance.
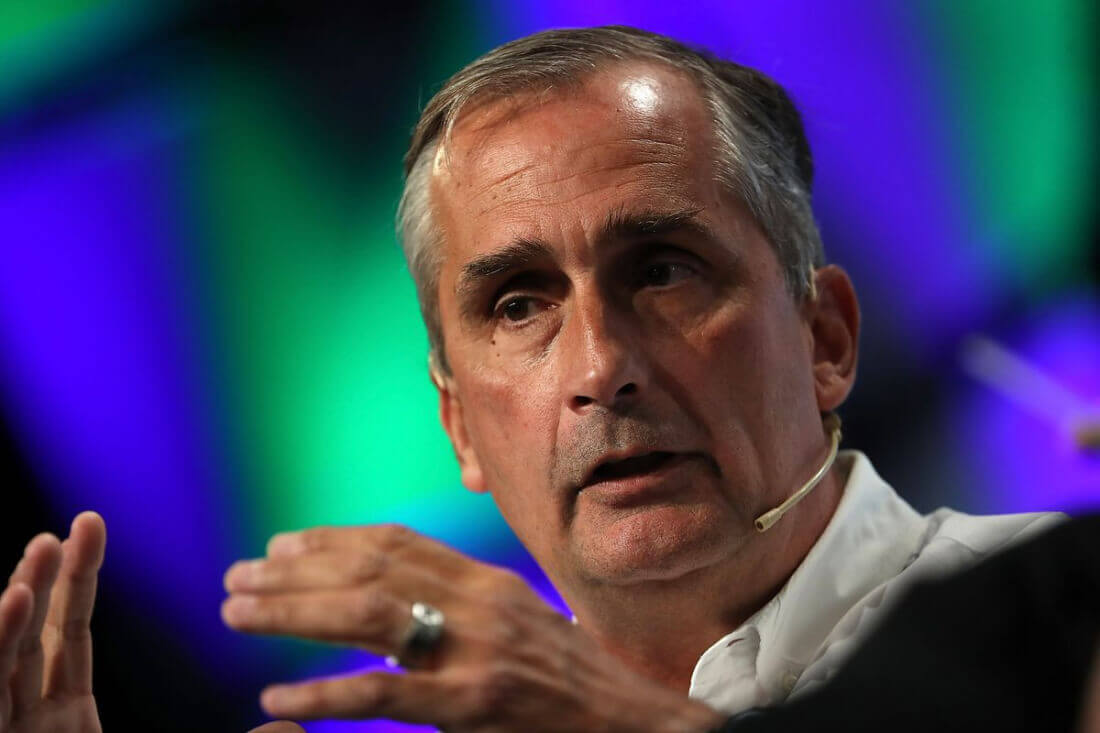
Fortunately, that may not be the case in the future. In a blog post, Intel CEO Brian Krzanich announced the company's intentions to "[advance] security at the silicon level" by ensuring their upcoming 8th-generation "Xeon Scalable" processors – codenamed "Cascade Lake" – won't be as vulnerable to Spectre variants upon release. The following excerpt details how Krzanich intends to accomplish his company's goals:
...I also want to take the opportunity to share more details of what we are doing at the hardware level to protect against these vulnerabilities in the future. This was something I committed to during our most recent earnings call.
While Variant 1 will continue to be addressed via software mitigations, we are making changes to our hardware design to further address the other two. We have redesigned parts of the processor to introduce new levels of protection through partitioning that will protect against both Variants 2 and 3. Think of this partitioning as additional "protective walls" between applications and user privilege levels to create an obstacle for bad actors.
Whether or not this "obstacle" will completely stop hackers from taking advantage of the exploits remains to be seen. Based on Krzanich's wording, it sounds like the upcoming hardware tweaks may simply slow hackers down.
Regardless, it's nice to see Intel sticking to their earlier promise to maintain a greater degree of transparency with their customers regarding the two vulnerabilities.