Back in March, the United States Computer Emergency Readiness Team issued a warning that Russian organizations have been targeting key infrastructure such as the power grid, nuclear sites, water and aviation installations.
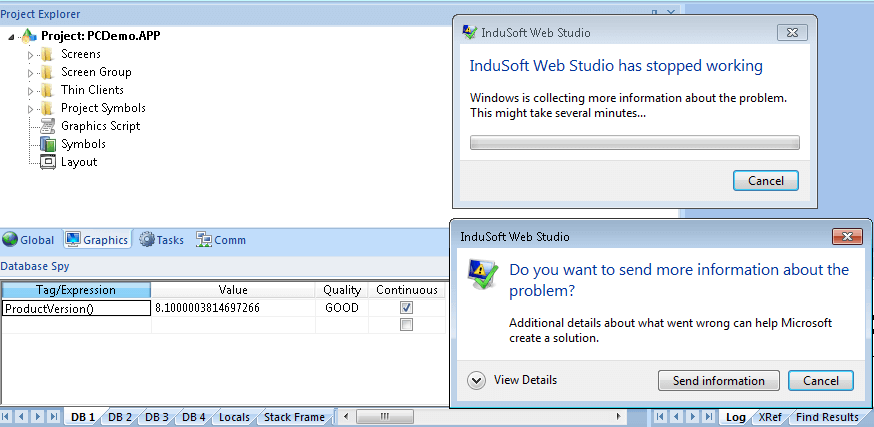
Since then, industrial equipment manufacturers have been scrambling to patch their broken products that oversee many critical systems to keep day-to-day life proceeding as usual. Most recently, several flaws allowing for remote code execution have been discovered in Schneider Electric's InduSoft Web Studio and InTouch Machine Edition software.
Both pieces of software are part of Supervisory Control and Data Acquisition (SCADA) systems that are used to build applications for embedded devices. It is possible to remotely exploit the software on a TCP port and execute arbitrary code without going through any authentication procedures.
The exploit leads to a full compromise of a server running the software as well as human machine interfaces connected to it. This could allow for important controllers to be shut down or altered to cause serious problems.
Blackouts, loss of access to medical equipment, lack of ability to process waste water and shutdowns of assembly lines were all possibilities. Thankfully, a patch was issued on April 6 to fix both pieces of software.
Cyber attacks are becoming a larger threat than ever now that critical infrastructure is heavily dependent on modern technology. In August last year, a Saudi Arabian petrochemical facility using Schneider Electric's programmable logic controllers was almost destroyed by malware attempting to cause an explosion.
Going forward, it is evident that more rigorous validation of product security is necessary for components that are used in mission-critical environments.
