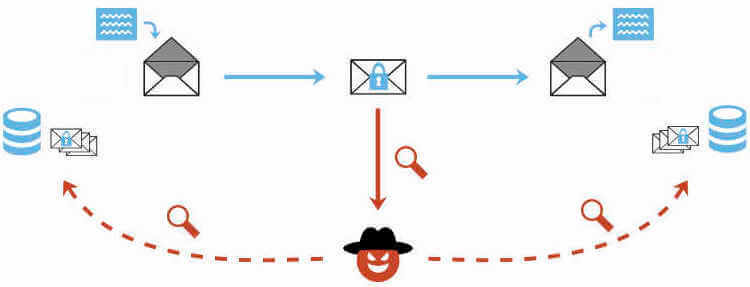
Pretty Good Privacy (PGP) is an encryption tool used to sign emails, documents, directories, and even full hard disks. According to security researcher and professor Sebastian Schninzel of FH Münster, PGP and S/MIME email encryption contains a flaw that allows for the plaintext form to be recovered.
This is a major concern for anyone who is using the encryption to protect sensitive information. Previously encrypted emails may now become available for decryption without having the proper credentials to do so.
Although the research will not be released until Tuesday at 7am UTC (scratch that, it's out already), the Electronic Frontier Foundation was granted access to the full publication ahead of time in an effort to warn the community of the risk. Schninzel and the rest of his team are intentionally warning users ahead of time as part of a responsible disclosure procedure.
Both the researchers involved and the EFF recommend that all users of PGP immediately disable or uninstall the tool they are using until the exact issues are better understood. Alternatives such as Signal are believed to remain secure methods of communication.
There are currently no reliable fixes for the vulnerability. If you use PGP/GPG or S/MIME for very sensitive communication, you should disable it in your email client for now. Also read @EFF's blog post on this issue: https://t.co/zJh2YHhE5q #efail 2/4
--- Sebastian Schinzel (@seecurity) May 14, 2018
Currently, there is no fix that has been developed to fix the flaws found. All we know for right now is that PGP and S/MIME should be avoided until there is more information to determine their future viability.
