The FBI has seized control of a key domain that was used to infect 500,000 infected routers in 54 countries. The move comes after security reports from Cisco and Symantec revealed a modular, multi-stage malware dubbed VPNFilter, which can collect data, infect other devices, steal credentials, and even destroy a device.
According to an FBI affidavit (via the Daily Beast), Kremlin-linked hacking group Sofacy, also known as Fancy Bear, was behind the operation. The same attackers were responsible for a number of past incidents, the most famous being the 2016 hack of the Democratic National Committee.
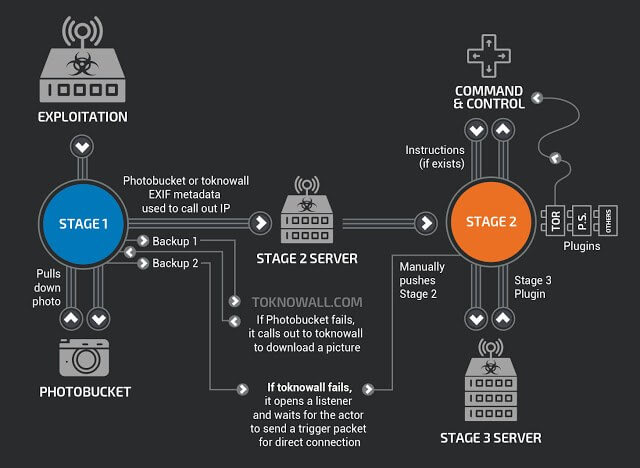
There are several stages to VPNFilter that make it particularly malicious. The first stage sees the malware write itself to device's memory so it persists even after a reboot, making it one of the few types of IoT malware that's able to do this. Stage 2 covers file collection, command execution, data exfiltration, and device management. It's this stage that can also overwrite a critical portion of a device's firmware, rendering it unusable.
Stage 3 contains at least two plugin modules: a packet sniffer for collecting traffic, including website credentials, and a communications module that allows stage 2 to communicate over Tor.
Ukraine's SBU security service said the malware proved Russia was getting ready for a major cyberattack on the country "aimed at destabilizing the situation" during the Champions League soccer final in Kiev on Saturday and possibly the country's annual Constitution Day celebrations.
The FBI, which has been investigating the campaign since August, received permission from a federal judge in Pennsylvania to seize ToKnowAll.com. The domain hosted a backup server for uploading the second stage of VPNFilter to infected routers if the primary method, which used Photobucket, was unsuccessful.
Vikram Thakur, technical director at Symantec, said the FBI had now effectively killed the malware's ability to reactivate following a reboot.
"This operation is the first step in the disruption of a botnet that provides the Sofacy actors with an array of capabilities that could be used for a variety of malicious purposes, including intelligence gathering, theft of valuable information, destructive or disruptive attacks, and the misattribution of such activities," Assistant Attorney General for National Security John Demers said in a statement.
Here is a list of all affected routers. If you own one of these models, you should follow Cisco and Symantec's advice and perform a factory reset.
- Linksys E1200
- Linksys E2500
- Linksys WRVS4400N
- Mikrotik RouterOS for Cloud Core Routers: Versions 1016, 1036, and 1072
- Netgear DGN2200
- Netgear R6400
- Netgear R7000
- Netgear R8000
- Netgear WNR1000
- Netgear WNR2000
- QNAP TS251
- QNAP TS439 Pro
- Other QNAP NAS devices running QTS software
- TP-Link R600VPN