Why it matters: Last November cyber-security firm Check Point found several vulnerabilities in Epic Games' online platform that allowed it to takeover player accounts. It immediately informed the game company, which quickly patched the weaknesses without announcing them. Check Point issued a public report of its findings today.
Researchers at Check Point Software Technologies uncovered multiple vulnerabilities in Epic Games online infrastructure that could allow malicious actors to take over individual accounts in Fortnite. The hackers would have full access to the player's account and personal information. They would also be able to eavesdrop on the victim through the game's voice chat.
Israel-based Check Point disclosed the flaw privately to Epic Games in early November 2018. The game developer quietly issued a patch just before December.
It started with Check Point finding two Epic subdomains that allowed redirects. This oversight opened up the opportunity for phishing attacks. Malicious links could be crafted that appeared safe since the URLs seemed to come from Epic Games' domains. However, once clicked, the authentication token could be grabbed without users even signing in with their credentials.
"Our team's research relied on a sophisticated and sinister method, that did not require the user to hand over any login details whatsoever. By discovering a vulnerability found in some of Epic Games' sub-domains, an XSS attack was permissible with the user merely needing to click on a link sent to them by the attacker. Once clicked, with no need even for them to enter any login credentials, their Fortnite username and password could immediately be captured the attacker."
So the exploit did not steal users' credentials directly but rather hijacked the authentication token that is passed from SSO (single-sign-on) logins such as those seen with Facebook, Google, PlayStation, Xbox, or Nintendo to Epic's servers.
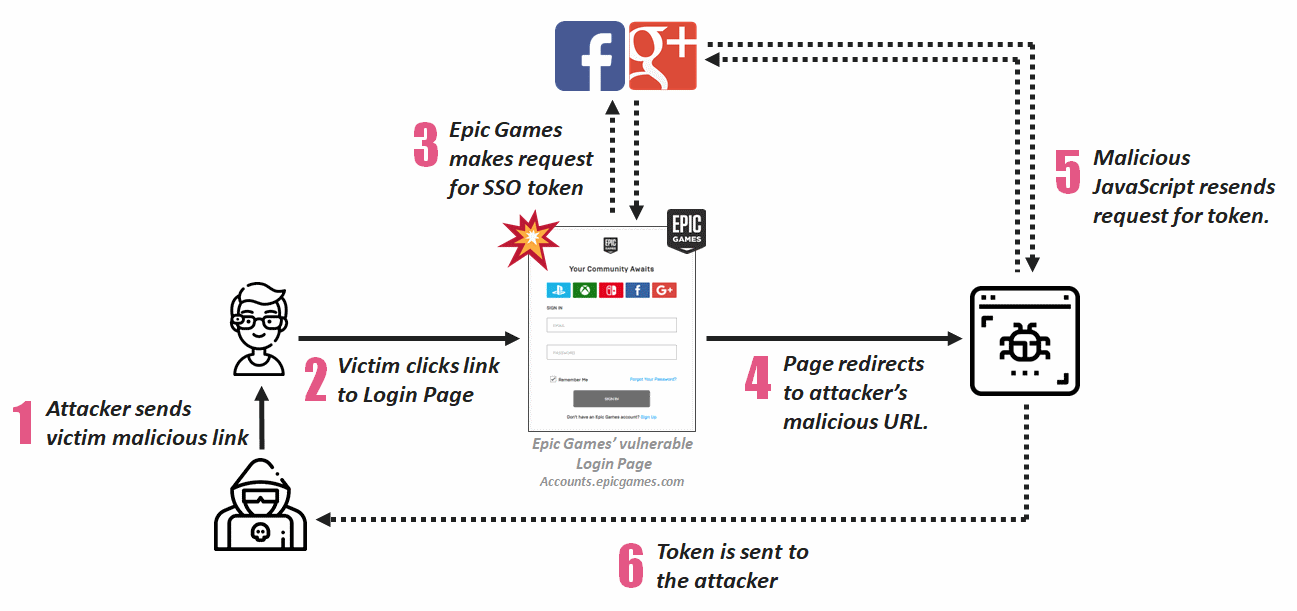
The techniques used exploited several bugs in Epic's online platform and used a handful of simple techniques including phishing, SQL injection, cross-site scripting, and WAF bypassing to name a few. Most of the flaws were not even related to Fortnite code.
Despite the sophistication of the contrived attack, the researchers said that it was not difficult to perform.
"[The attack is] not advanced at all, very simple to execute in the background," Oded Vanunu told ZDNet via email. "Token stealing is one of the emerging attack vectors....everyone is out for the authentication tokens & exploiting application logic."
The vulnerability is fixed now, so Fortnite players can rest easy knowing their accounts are safe from this attack. However, both Check Point and Epic strongly urge players to use 2FA.
"These platforms are being increasingly targeted by hackers because of the huge amounts of sensitive customer data they hold," said Vanunu. "Enforcing two-factor authentication could mitigate this account takeover vulnerability."
If you're interested in all the technical details, checkout Check Point's report.
Images via Check Point
