The big picture: Microsoft isn't entirely responsible. In fact, none of the top most exploited vulnerabilities are in Office itself but rather, exist in related components. Still, the Redmond tech giant does shoulder some of the blame due to decisions made when creating Office.
Kaspersky at its recent Security Analyst Summit (SAS) shared a trend that surprised even its own researchers.
In the fourth quarter of 2016, cybercriminals largely favored web-based vulnerabilities that could be exploited via browser software. Just two years later in the fourth quarter of 2018, the security company found that Microsoft Office is now targeted in a whopping 70 percent of attacks.
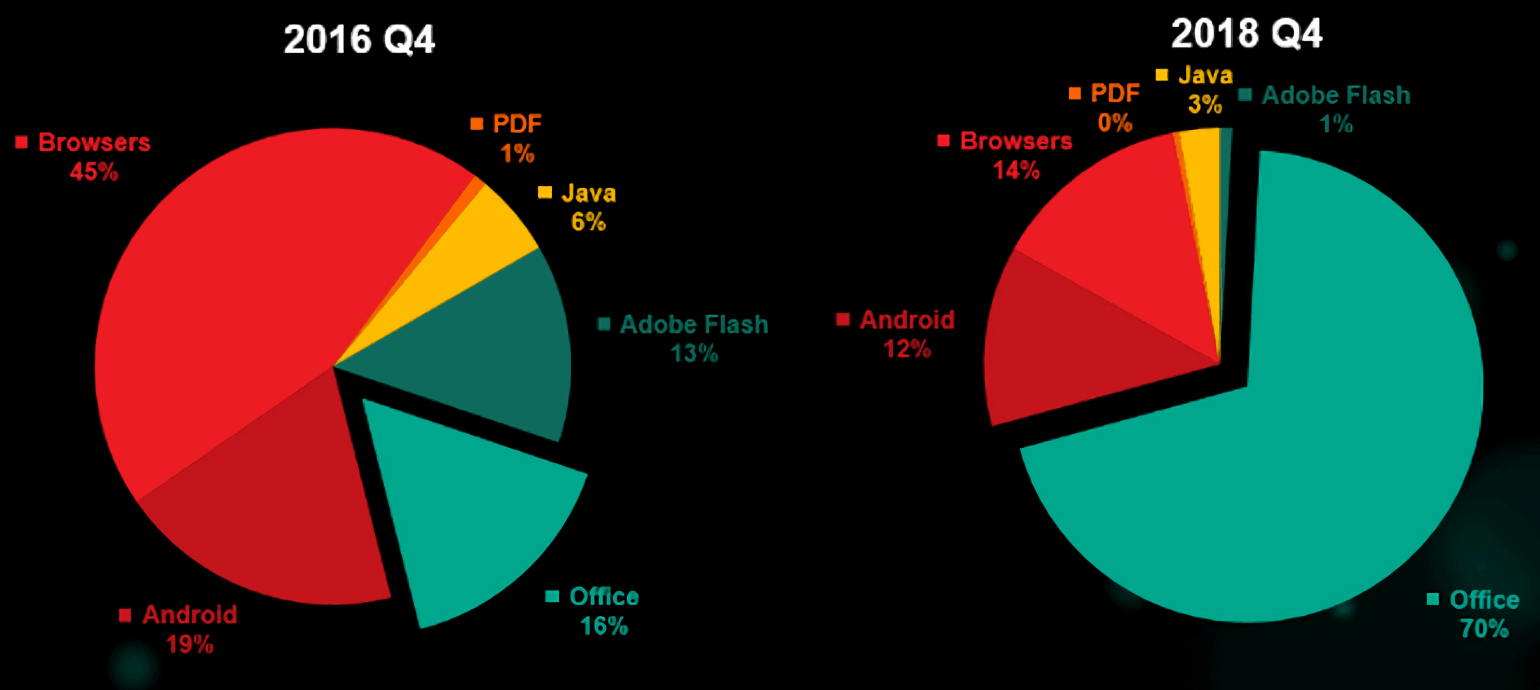
Browsers accounted for 45 percent of attacks in 2016; now, that figure is down to just 14 percent.
Kaspersky noted that the turnaround time for exploiting a vulnerability has shortened substantially, adding that malware authors now prefer simple, logical bugs. This is evident by looking at the most exploited bugs in Office: equation editor vulnerabilities CVE-2017-11882 and CVE-2018-0802.
Simply put, they are reliable and work in every version of Word released in the past 17 years. And, most important, building an exploit for either one requires no advanced skills. That's because the equation editor binary didn't have any of the modern protections and mitigations you'd expect from an application in 2018.
The problem, Kaspersky said, is that Office's attack surface is huge. What's more, some of the decisions Microsoft made when creating Office now look flat out bad but changing them would "devastate backward compatibility."
Threat intelligence company Recorded Future last month found that eight of the top 10 vulnerabilities in 2018 targeted Microsoft products.
Lead image courtesy dennizn via Shutterstock
