The big picture: Software is not always able to find malicious code hidden in firmware of hardware components. Detecting hardware-based hacks is incredibly difficult, but progress is being made to thwart the effectiveness of such attacks.
In an age where Spectre and Meltdown CPU flaws have become prominent, these bugs only scratch the surface of what hackers and tinkerers have been looking at for years. Hiding malware inside of firmware within hard drives, motherboards, graphics cards, and other common components can make it impossible for OS-level software to find any anomalies.
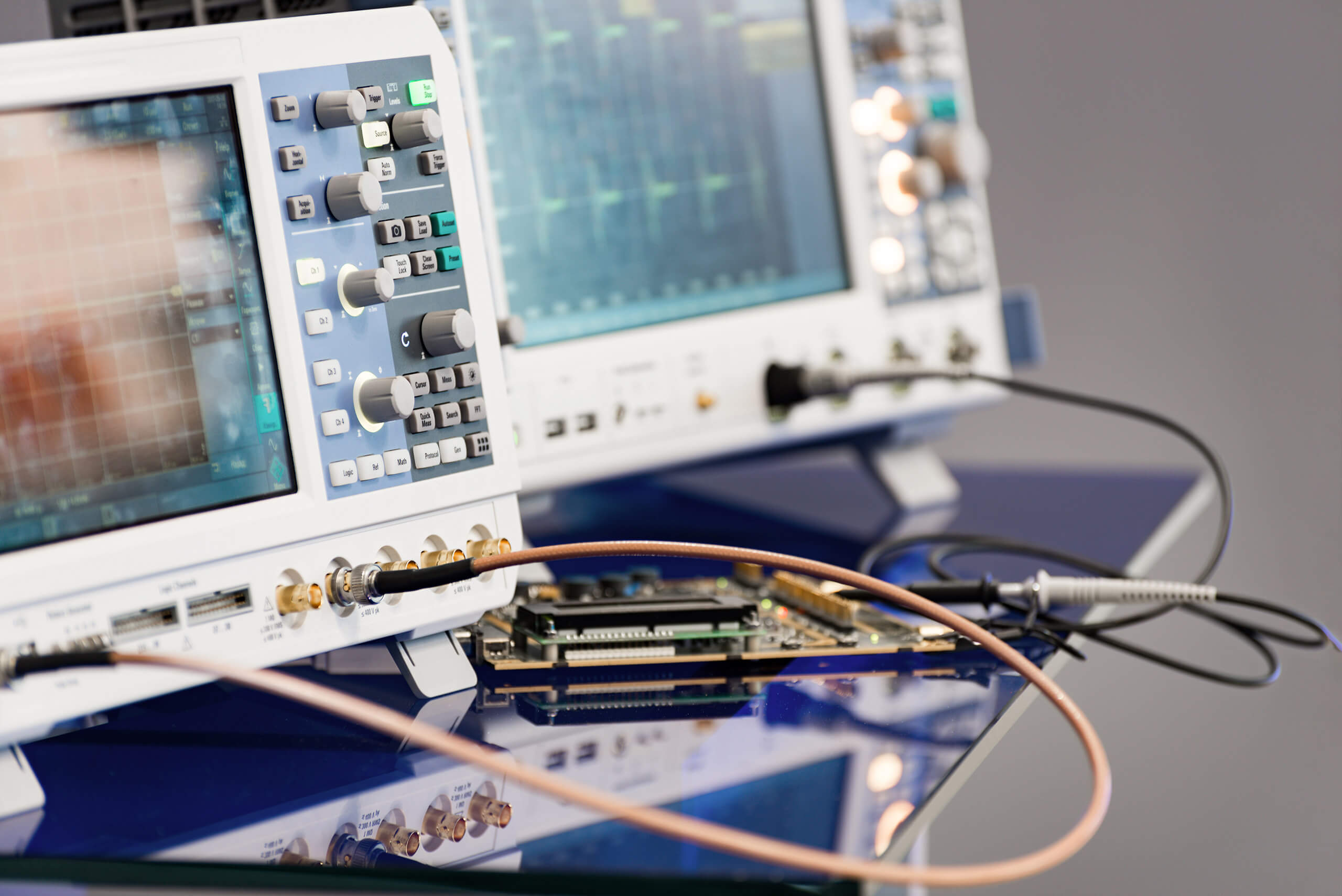
Even though malware developers have gotten even sneakier by implanting malicious code into embedded firmware, researchers from North Carolina State University and the University of Texas at Austin have developed a reliable method of identifying such intrusions. By characterizing the power usage of a system and each of the components within it, the type of malware present can be determined. Research was sponsored by Lockheed Martin and the National Science Foundation.
"The nature of micro-architectural attacks makes them very difficult to detect – but we have found a way to detect them"
Desktop computers are not the main application of such an innovation. Internet of Things devices and industrial embedded systems are the important use cases to look at. Many such devices do not have operating systems and are only executing machine code that is stored in a small section of non-volatile memory. Antivirus software is not even practical on the majority of embedded systems deployed to the real world.
Monitoring power use itself is not a new concept, but the idea of a plug-and-play solution capable of working with a variety of systems is intriguing. The only caveat here is that very carefully written malware can attempt to replicate normal power consumption. In these instances, there are times where the researchers' tool was unable to detect the presence of malware. However, data theft by the malware was slowed by 86 to 97 percent, still a major detriment to hackers that are good at covering their tracks.
Image Credit: Shutterstock by Nordroden