Why it matters: A resurgence in vulnerable CLDAP servers is making DDoS attacks more powerful and dangerous. Windows network administrators should adopt strict security practices or take the server off the internet if there is no practical need for using the CLDAP protocol.
A specific DDoS operation known as a "reflection attack" is again finding widespread use by cyber-criminals, abusing unprotected Microsoft servers to overload targeted websites with traffic. Black Lotus Labs notes the culprit is the Microsoft variant of the industry-standard Lightweight Directory Access Protocol (LDAP) known as CLDAP.
The LDAP protocol is used to access and maintain distributed directory information services (like a central system to store usernames and passwords) over an IP network. A CLDAP implementation is similar but limited to the Active Directory database system used in the Windows Server family of operating systems. Generally speaking, CLDAP services are on by default in many versions of the OS, but they are usually harmless for servers not connected to the public internet.
However, when a CLDAP machine is online, the UDP-based service is vulnerable to reflection DDoS assaults. This attack vector spoofs the target's IP address and sends a UDP request to one or more third parties. Those servers then respond to the spoofed address, which reflects back, creating a feedback loop. This breed of DDoS amplifies the traffic tens, hundreds, or thousands of times and conceals the attacker's IP.
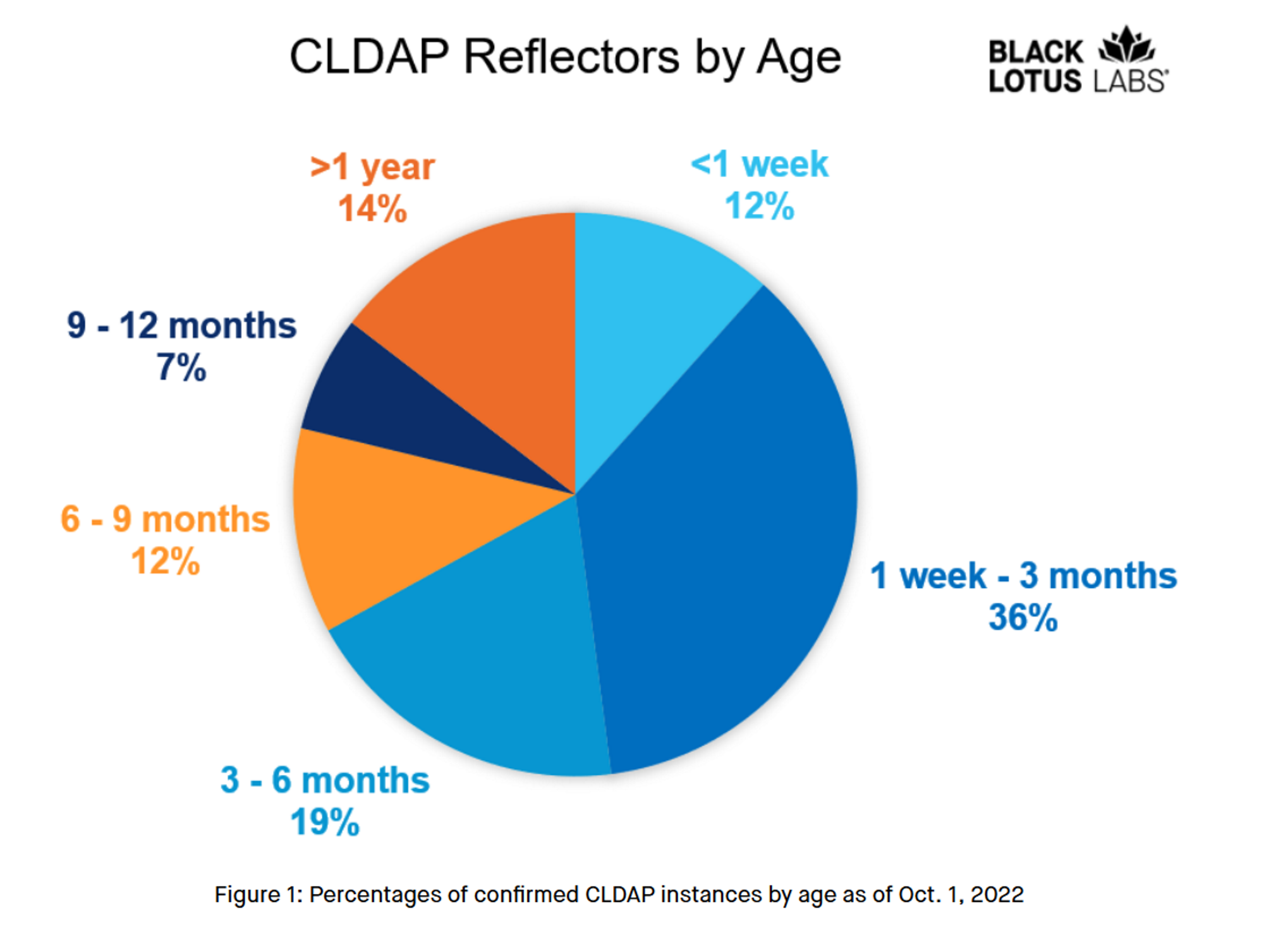
Reflection attacks abusing CLDAP servers are not particularly new. In the last 12 months, there has been a more than 60% increase in CLDAP abuse with over 12,000 instances of "zombified" servers. Black Lotus Labs said some "CLDAP reflectors" have lived online for a long time, and others come and go quickly.
The most troublesome CLDAP reflectors are the ones hackers have used for years in multiple powerful DDoS attacks. Black Lotus profiled some of those serial offenders, like the server belonging to an unnamed religious organization that was generating (between July and September 2022) traffic bursts of up to 17Gbps.
Another CLDAP reflector located in North America was capable of delivering peak traffic rates of more than 2Gbps over 18 months. A third vulnerable service hackers have exploited for over a year now belongs to a North American telecom provider. Yet another in North Africa, belonging to a regional retail business was responsible for nine months of ferocious DDoS attacks delivering up to 7.8Gbps of traffic.
Black Lotus suggests that if a CLDAP server absolutely needs to stay online, network administrators should take "pains" to secure it by turning off UDP support, limiting the traffic generated on port 389, using firewalls, or implementing some advanced measures to prevent spoofed IP traffic like Reverse Path Forwarding (RPF).
